-
Post-Quantum, PQC, Quantum Security

The Anatomy of Quantum Denial: What Bitcoin’s Response to the Quantum Threat Teaches Every CISO
At Bitcoin 2026, the same main stage hosted engineers building quantum-resistant upgrades and a trio claiming quantum computers can never work because Bitcoin proves time is discrete. The dysfunction that produced this scene plays out in every enterprise boardroom facing…
Read More » -
Quantum Security Reference

What Is a Logical Qubit?
Every quantum computing headline features a qubit count. Almost none of them distinguish between physical qubits and logical qubits. That distinction is the single most important concept for evaluating quantum progress — and the one most consistently misunderstood outside the…
Read More » -
Quantum Security Reference
What Is a CRQC (Cryptographically Relevant Quantum Computer)?
A CRQC is the quantum computer capable of breaking real-world cryptography. None exists today, but the engineering path is advancing across every required capability. This reference explains what a CRQC requires, how to track progress toward one, and why the…
Read More » -
Quantum Security Reference

What Is Q-Day?
Q-Day is the day a quantum computer can break widely used public-key cryptography. Predictions range from 2030 to never. But as I have argued, that debate is becoming irrelevant — regulators, insurers, and technology vendors have already set their own…
Read More » -
Quantum Security Reference

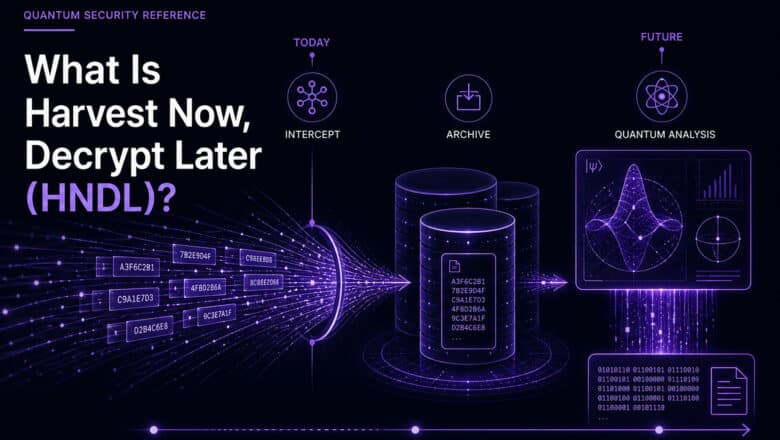
What Is Harvest Now, Decrypt Later (HNDL)?
Harvest Now, Decrypt Later is the reason the quantum threat is not a future problem. Nation-state adversaries are collecting encrypted data today, waiting for quantum computers powerful enough to break it. If your data needs to stay confidential for a…
Read More » -
Quantum Security Reference

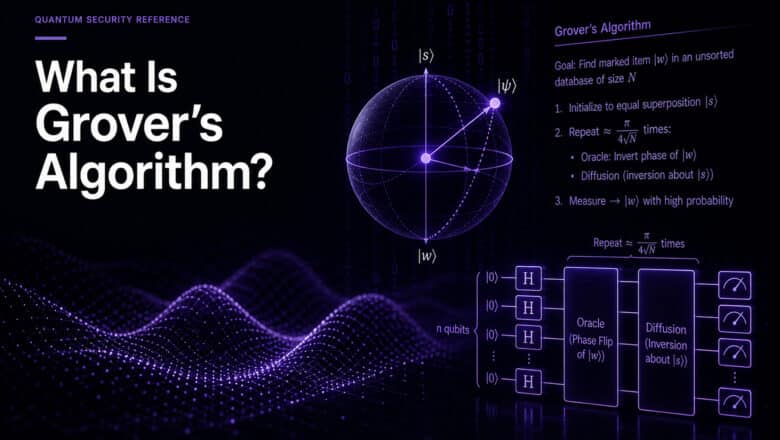
What Is Grover’s Algorithm?
Grover's algorithm is the quantum threat to symmetric cryptography. It halves effective key lengths, which sounds alarming until you do the math. AES-256 remains secure. AES-128 does not. This reference explains the algorithm, its limits, and why the common advice…
Read More » -
Quantum Security Reference

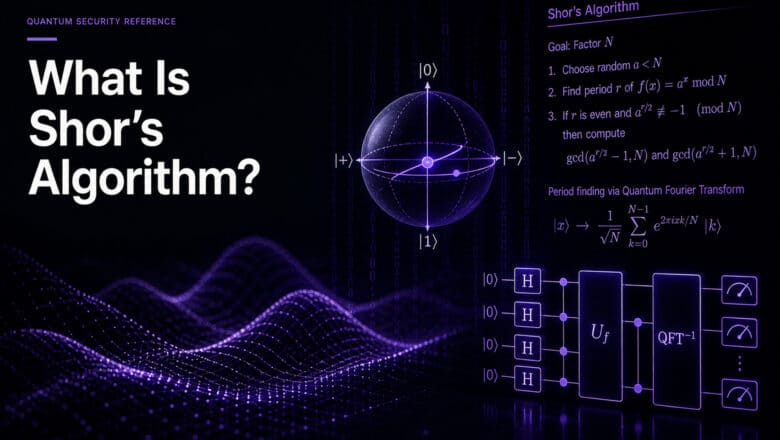
What Is Shor’s Algorithm?
Shor's algorithm is the reason post-quantum cryptography exists. Published in 1994, it proved that a quantum computer could break RSA, ECC, and Diffie-Hellman. The resource estimates for executing it keep dropping. This reference explains the algorithm's implications without the mathematics.
Read More » -
Quantum Security Reference

What Is Quantum Safe?
Every vendor now claims their product is "quantum safe." This reference explains what the term actually means, how it differs from related labels, what standards define it, and how to evaluate quantum-safe claims in procurement, compliance, and architecture decisions.
Read More » -
Quantum Security Reference

What Is Quantum Computing Security?
Quantum computing security has two meanings: protecting classical systems against quantum attack, and protecting quantum computers themselves. Both matter, but the first is why every CISO has a deadline. This reference covers what breaks, how soon, and what the dual…
Read More » -
Quantum Security Reference

What Is Quantum Cyber Security?
Quantum cyber security is no longer a research topic. NIST has finalized the standards, regulators have set hard deadlines starting in 2027, and the migration to quantum-resistant cryptography will touch every system in your organization. This reference covers what security…
Read More » -
Quantum Security Reference

What Is Quantum Cryptography?
Quantum cryptography uses quantum physics to protect information, most commonly through quantum key distribution (QKD). It is not the same thing as post-quantum cryptography. This reference explains what quantum cryptography actually is, how QKD works, why countries disagree on its…
Read More » -
Quantum Security Reference

Quantum Security: A Complete Guide for Security Leaders
Sixteen concepts. One imperative. The quantum threat to cryptography is no longer a future concern — the deadlines for action are already set, and most organizations haven't started. This guide maps the complete quantum security landscape for CISOs and security…
Read More » -
Quantum Security Reference

What Is Post-Quantum Cryptography (PQC)?
NIST finalized the first post-quantum cryptography standards in August 2024. Browser vendors, cloud providers, and HSM manufacturers are already shipping implementations. This reference explains why current public-key cryptography will break, how the replacement algorithms work differently, which standards NIST selected,…
Read More » -
Post-Quantum, PQC, Quantum Security

Crypto-Agility Is an Architecture Problem, Not a Library Swap
Every PQC migration guide tells you to "be crypto-agile." After leading migrations at Fortune Global 500 scale, I can tell you where that advice fails: HSMs that can't upgrade, protocols with hard-coded algorithms, and embedded devices that will outlive the…
Read More » -
Research

IBM’s Quantum Advantage Claim: What the Heron-Fugaku Experiment Actually Shows
IBM says quantum advantage arrives in 2026. A new Heron-Fugaku experiment provides the evidence. Whether it proves the claim depends on how you define “advantage.”
Read More »