Quantum Computing News, PQC News, Quantum Security News & Commentary
What’s Happening in Quantum — and What It Means
PQC Migration Framework v2.0 Released: What Changed, Why It Matters, and a Note on Attribution
The PQC migration problem shifted from "how do we prepare?" to "how do we deploy?" between March and June 2026. Version 2.0 of the Applied Quantum PQC Migration Framework responds with the operational depth that no other published methodology provides ...
Let’s Encrypt Commits to Merkle Tree Certificates for Post-Quantum HTTPS
The world's largest certificate authority has committed to Merkle Tree Certificates as its post-quantum path. With 54% of all public TLS certificates, Let's Encrypt's decision effectively sets the migration timeline for the entire web ...
IonQ Demonstrates qLDPC Breakeven on Trapped Ions — and the Flexibility Argument Just Got Harder to Ignore
IonQ's 40-ion trapped-ion device runs nine different error-correcting codes with zero hardware changes and hits breakeven on qLDPC codes — beating the only superconducting comparison by up to 9×. The real story is what this means for the qubit-efficient architectures the field is betting on ...
Atom Computing Demonstrates Quantum Error Correction With Toric Code, a First for Neutral Atoms
Atom Computing's toric code demonstration is the first sustained quantum error correction on a neutral-atom platform, running 90 syndrome extraction rounds with continuous atom reloading ...
Bernstein Demonstrates ML-DSA Key Recovery in Under One Second, Argues Solo Deployment Damages Security
Daniel J. Bernstein provides the first working attack demos against ML-DSA implementation bugs, recovers equivalent secret keys in under one second, and builds a quantitative case that solo ML-DSA deployment damages security compared to hybrid Ed25519+ML-DSA ...
OQC Raises £260M in Europe’s Largest Private Quantum Round — Where the Money Actually Goes
Europe's largest private quantum round lands at £260M, with 38% from the British Business Bank. The money is earmarked for OQC's TITAN system, but the gap between 32 qubits today and 200 logical qubits by 2028 demands closer examination ...
Joining Project Eleven as Advisor
I don't usually announce advisory roles. This one is different, because making digital assets quantum-safe may be the hardest PQC migration challenge of all ...
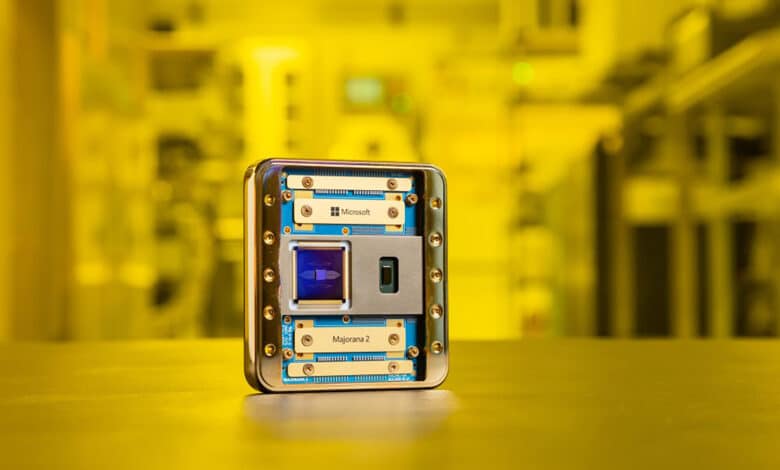
Microsoft’s Majorana 2 Chip Achieves 20-Second Parity Lifetime — But the Topological Qubit Debate Rages On
Microsoft's second topological quantum chip achieves a 1,000-fold improvement in parity lifetime by swapping aluminum for lead. The engineering progress is real. Whether these are topological qubits at all remains fiercely contested ...
IBM Commits $10 Billion to Quantum, Launches America’s First Quantum Chip Foundry
IBM's five-year, $10 billion quantum commitment funds the Starling fault-tolerant system by 2029 and Anderon, a standalone quantum chip foundry in Albany backed by $1 billion in CHIPS Act incentives ...
Google’s Secret Quantum Circuits for Breaking ECC Reproduced and Improved in Two Months
A French researcher independently matched Google's secret quantum circuits for breaking elliptic curve cryptography, then improved the gate count. Google's Craig Gidney says the zero-knowledge approach failed and open publication should resume ...
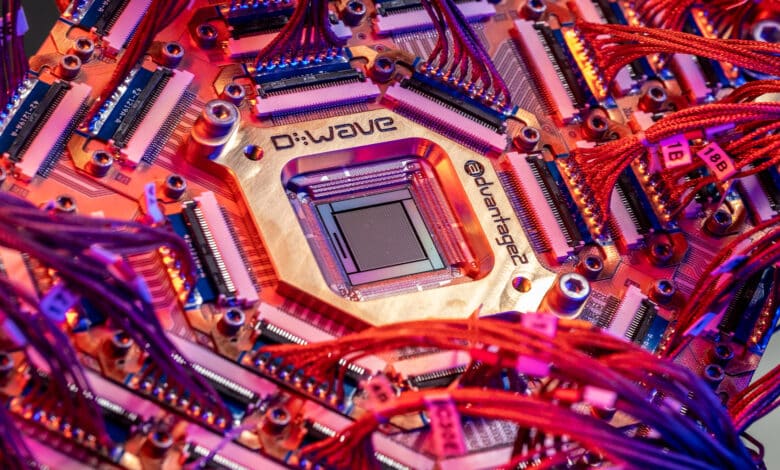
D-Wave Bets Its Future on Gate-Model Quantum Computing with 2032 Fault-Tolerance Roadmap
D-Wave's first Investor Day roadmap targets 100 fault-tolerant logical qubits by 2032 using dual-rail superconducting qubits. The annealing pioneer enters a crowded gate-model race with an unproven architecture and ambitious error-reduction targets ...
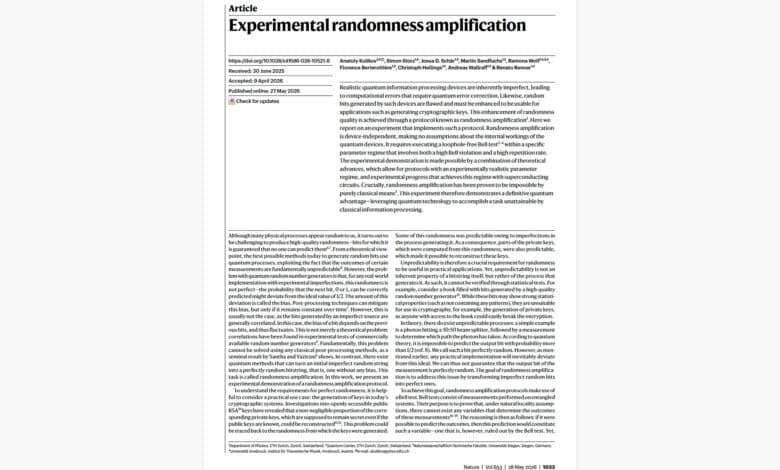
ETH Zurich’s “Perfect Randomness”: What Actually Happened
A new preprint series claims to break every major lattice-based NIST PQC standard via an improved CDPR attack. The claim has critical technical gaps that the lattice cryptography community will need to resolve ...
A New Paper Claims to Break ML-KEM, Falcon, Hawk, and NTRU. Should You Worry?
A new preprint series claims to break every major lattice-based NIST PQC standard via an improved CDPR attack. The claim has critical technical gaps that the lattice cryptography community will need to resolve ...
IBM’s Concatenated Gross Code Reaches the Teraquop Regime
IBM's QEC team packages 11 logical qubits into a single high-dimensional qudit and wraps the gross code in quantum Reed-Solomon algebra. The result: a fault-tolerant memory that reaches the teraquop regime the gross code couldn't previously access ...
France Answers the US CHIPS Act in 24 Hours, and NVIDIA Is Buying a Seat at Every Table
Macron added €1 billion to France's quantum strategy the day after the US committed $2 billion to quantum fabs. France's total quantum commitment now stands at €3.3 billion, and NVIDIA's investment in Alice & Bob landed the same afternoon ...