What Is Harvest Now, Decrypt Later (HNDL)?
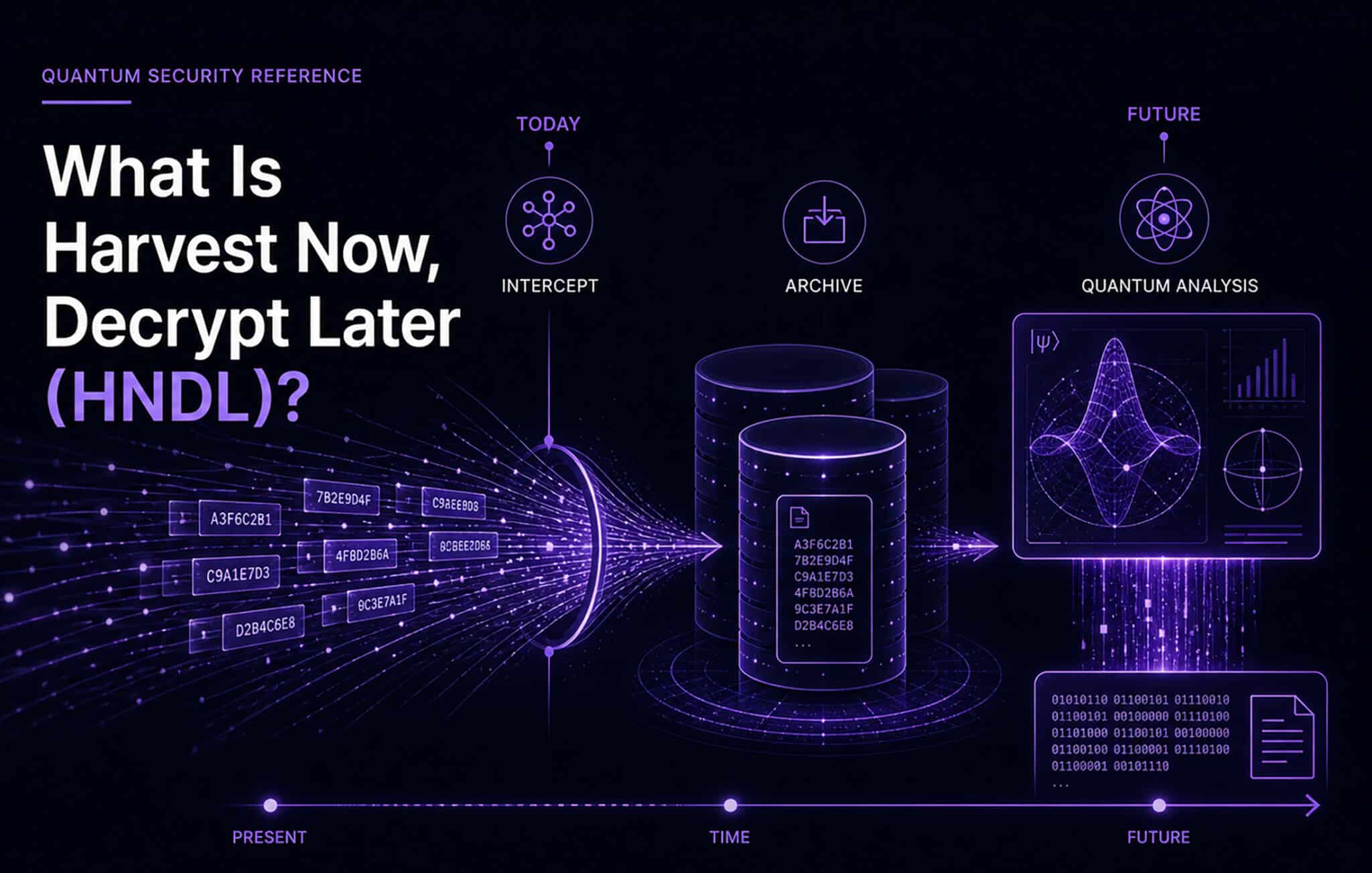
Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
Harvest Now, Decrypt Later (HNDL) is the practice of intercepting and storing encrypted data today with the intention of decrypting it in the future, once a quantum computer powerful enough to break the encryption becomes available. The concept transforms the quantum threat from a hypothetical future problem into an active, present-day risk. Data encrypted with RSA or ECC that is captured today will become readable the moment a CRQC exists.
Why HNDL Is the Argument That Changed Everything
Before HNDL entered the conversation, the quantum threat could be rationalized as a problem for a later planning cycle. The reasoning was straightforward: no quantum computer can break encryption today, so the threat can wait. HNDL demolished that logic.
The insight is simple but consequential. Encrypted network traffic and stored ciphertext can be recorded cheaply and at massive scale. Storage costs continue to fall. Nation-state intelligence services already operate bulk collection infrastructure designed for exactly this purpose. If an adversary captures encrypted data today and a CRQC becomes operational in 2035, every intercepted communication, transaction, and document from the intervening decade becomes retroactively transparent.
The data does not expire. The encryption protecting it eventually will.
This is why every major quantum security mandate (NIST’s guidance, NSA’s CNSA 2.0, the EU’s recommendations) treats HNDL as the primary justification for acting now. The threat is not the CRQC itself; the threat is the combination of a future CRQC and data that was collected years before it existed.
Which Data Is at Risk
Not all data carries the same HNDL exposure. The critical variable is how long the data needs to remain confidential. A marketing email encrypted in transit and read five minutes later has negligible HNDL risk. A diplomatic cable with a 50-year classification window has enormous HNDL risk.
The highest-exposure categories include government and military communications (classified intelligence, diplomatic traffic, defense planning), healthcare records (patient data with lifelong confidentiality obligations), financial data (long-term investment strategies, M&A communications, trade secrets with multi-decade commercial value), intellectual property (pharmaceutical research, advanced technology designs, proprietary algorithms), and personal identity data (biometric records, social security numbers, and other identifiers that cannot be rotated).
Data discovery and classification is the foundation of any HNDL risk assessment. Without knowing what data you hold, how it flows, and how long it must remain protected, you cannot prioritize your PQC migration.
Mosca’s Inequality: The Math of Urgency
Mosca’s theorem provides the clearest framework for assessing HNDL urgency. It defines three variables:
x = the number of years your data must remain confidential y = the number of years it will take to migrate your cryptographic infrastructure to quantum-safe algorithms z = the number of years until a CRQC exists
If x + y > z, you are already too late. The data you need to protect will outlast your ability to protect it before a quantum computer can compromise it.
The power of this inequality is that it reframes the timeline question. Even if z is 15 years away (a moderate estimate), an organization with data that must remain confidential for 10 years (x = 10) and a migration timeline of 7 years (y = 7) faces the uncomfortable arithmetic that 10 + 7 = 17 > 15. They should have started two years ago.
For large enterprises, y is almost always longer than expected. Migration involves cryptographic inventory, vendor coordination, protocol testing, infrastructure upgrades, and regulatory compliance across hundreds or thousands of systems. I have documented why PQC migration spans upwards of 120,000 tasks in a large organization. Compressing that timeline is expensive and risky.
Who Is Harvesting
Attribution in signals intelligence is inherently uncertain, but the general picture is well understood. Nation-state intelligence agencies with bulk collection capabilities are the primary HNDL actors. The resources required (submarine cable taps, satellite intercept stations, ISP-level collection agreements, massive storage infrastructure) limit HNDL to state-level or state-sponsored operators.
The Five Eyes intelligence alliance, China’s Ministry of State Security, and Russia’s FSB and GRU all operate signals intelligence programs with the collection infrastructure to execute HNDL at scale. The question is not whether bulk encrypted data collection is occurring. It is which encrypted data flows are being prioritized by which adversaries.
For organizations in defense, diplomacy, critical infrastructure, advanced technology, or financial services, the prudent assumption is that relevant encrypted traffic is being captured today.
HNDL’s Counterpart: Trust Now, Forge Later
While HNDL targets confidentiality (the secrecy of data), its counterpart targets trust. Trust Now, Forge Later (TNFL), a concept I introduced in 2018, describes the risk that digital signatures made today with RSA or ECC could be forged retroactively once a CRQC exists. Where HNDL compromises what was said, TNFL compromises who said it.
Together, HNDL and TNFL represent the two dimensions of the pre-quantum threat: confidentiality and authenticity, both vulnerable before a CRQC is built, both requiring action now.
What to Do About It
The defense against HNDL is straightforward in concept: encrypt data with algorithms that a quantum computer cannot break. In practice, this means migrating to post-quantum cryptography.
Prioritize the systems carrying data with the longest confidentiality requirements. Classify your data by HNDL exposure window. Begin migration with the highest-risk channels and work outward. The Applied Quantum PQC Migration Framework provides the methodology, and my risk-driven strategies for quantum readiness offer a pragmatic approach when a full cryptographic inventory is not immediately feasible.
As I have argued throughout PostQuantum.com, the deadlines for action are already set by regulators and industry, independent of when a CRQC arrives. HNDL is the reason those deadlines exist.
Go Deeper
Q-Day Deadlines Are Set — why ecosystem deadlines matter more than predictions
Harvest Now, Decrypt Later (HNDL) Risk — full analysis of the HNDL threat
Mosca’s Theorem and Post-Quantum Readiness — the mathematical framework for urgency
Trust Now, Forge Later (TNFL) — the signature counterpart to HNDL
Data Discovery and Classification for Quantum Readiness — identifying your highest-risk data
Risk-Driven Strategies for Quantum Readiness — when full inventory is not feasible
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.