Deep Dive Series
CNSA 2.0: Inside NSA’s Post-Quantum Requirements
The NSA’s Commercial National Security Algorithm Suite 2.0 is the most operationally specific post-quantum cryptography mandate in the world. It names the exact algorithms, specifies the exact parameter levels, and sets hard deadlines by system category — starting with a procurement gate in January 2027 that turns PQC from a planning exercise into a pass-fail acquisition requirement. With defense acquisition cycles running 18 to 36 months, systems being designed today will be delivered after the deadline. The planning window is already behind us for many programs.
This Deep Dive series breaks CNSA 2.0 apart from the inside out — starting with the complete algorithm and timeline reference, then examining the 2027 procurement gate that most organizations are underestimating, before mapping the growing divergence between national PQC requirements around the world. It then turns to the people who must actually implement this: the defense industrial base facing a compound compliance squeeze, financial services organizations adopting CNSA 2.0 as a voluntary benchmark, and the cryptographic choices NSA made — and didn’t make — that reveal how they think about lattice security and the road ahead.
-
CNSA 2.0

The 2027 Procurement Gate: Why CNSA 2.0 Compliance Starts Now
January 1, 2027 is when CNSA 2.0 stops being guidance and becomes a procurement gate. Combined with the FIPS 140-2 sunset in September and CMMC enforcement in November, it creates a five-month compliance squeeze that cannot be solved by urgency alone.
Read More » -
CNSA 2.0

CNSA 2.0 vs. the World: Navigating Diverging Global PQC Requirements
The world's major cryptographic authorities agree that post-quantum migration is necessary. They disagree on nearly everything else: which algorithms, which parameter levels, whether hybrid is mandatory, and whether NIST's standards are sufficient.
Read More » -
CNSA 2.0

CNSA 2.0 for the Defense Industrial Base
CNSA 2.0 applies to National Security Systems. The requirements cascade to every prime contractor, sub-tier supplier, and commercial vendor selling into classified environments — arriving alongside CMMC 2.0 enforcement and a FIPS 140-3 validation bottleneck.
Read More » -
CNSA 2.0

CNSA 2.0 Beyond NSS: Why Financial Services Is Adopting It Anyway
CNSA 2.0 technically applies only to National Security Systems. In practice, its algorithm choices are appearing in financial services procurement language, board-level risk assessments, and counterparty due diligence — creating a de facto standard for high-assurance cryptography far beyond its formal scope.
Read More » -
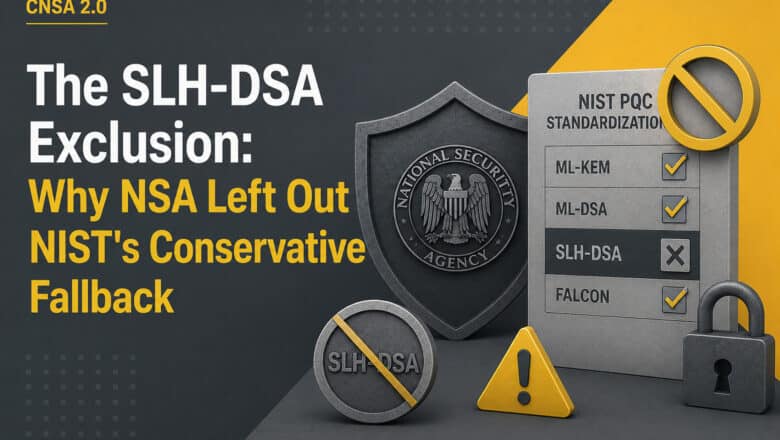
CNSA 2.0

The SLH-DSA Exclusion: Why NSA Left Out NIST’s Conservative Fallback
NSA excluded NIST's hash-based signature algorithm from CNSA 2.0 and stated it does not plan to add future post-quantum standards. The decision reveals how NSA thinks about lattice security, operational simplicity, and the trade-offs that other national authorities resolve differently.
Read More » -
Quantum Policies

The Complete US Post-Quantum Cryptography (PQC) Regulatory Framework in 2026
Three pillars anchor the US PQC framework: the Quantum Computing Cybersecurity Preparedness Act (federal law that no executive order can undo), NSM-10's 2035 migration target (still in force), and NIST's finalized FIPS standards (published August 2024). The Trump administration's June 2025 executive order streamlined, rather than eliminated, PQC obligations, removing prescriptive procurement mandates while retaining the CISA product category list and a TLS 1.3 deadline…
Read More » -
Quantum Security & PQC

NSA Updates CNSA 2.0 Guidance After NIST Finalizes Post-Quantum Standards
The updated FAQ locks in ML-KEM-1024 and ML-DSA-87 as the only approved public-key algorithms, excludes SLH-DSA entirely, and lays out enforcement timelines that start biting in 2025.
Read More » -
Policy & Sovereignty

NSA Unveils CNSA 2.0 Post-Quantum Algorithm Suite
The U.S. National Security Agency (NSA) has officially announced the release of the Commercial National Security Algorithm Suite 2.0 (CNSA 2.0), a new set of cryptographic standards designed to protect sensitive systems against future quantum-enabled cyber threats. The NSA’s cybersecurity advisory notifies National Security System (NSS) owners, operators, and vendors of the quantum-resistant (QR) algorithms that will replace current legacy encryption in classified and mission-critical…
Read More »