The 2027 Procurement Gate: Why CNSA 2.0 Compliance Starts Now

Table of Contents
Introduction
On January 1, 2027, every new acquisition for a U.S. National Security System must support CNSA 2.0 algorithms. A system delivered the day after without ML-KEM-1024 key establishment and ML-DSA-87 digital signatures is non-compliant on arrival. No waiver queue to wait in, no grandfather clause to invoke, no transition period to buy time. The gate is binary: your product supports the required post-quantum algorithms or it cannot be procured.
That deadline is eight months away as I write this. And it does not arrive alone.
On September 21, 2026, NIST moves all remaining FIPS 140-2 certificates to Historical status, meaning cryptographic modules validated under the old standard can no longer be procured for new federal systems. On November 10, 2026, CMMC 2.0 Phase 2 begins, requiring third-party assessments for most Level 2 defense contractors, with FIPS-validated cryptography as a prerequisite for Control 3.13.11. Then comes the CNSA 2.0 gate on January 1, 2027.
Three cryptographic compliance deadlines in five months. Each assumes the previous one has already been addressed. Each is harder than the last. And the organizations that will clear all three share one characteristic: they started preparing well before 2026.
Why 2027, Not 2030 or 2035, Is the Date That Matters
The CNSA 2.0 timeline includes milestones stretching to 2035, and the later dates tend to get the attention. Exclusive use of CNSA 2.0 for network equipment by 2030. Full migration by 2033 or 2035 depending on system category. These numbers are easier to absorb because they feel distant. But every one of those milestones depends on infrastructure that must be procured, designed, and deployed before it can be operated, and January 2027 is when the procurement filter activates.
Defense acquisition cycles run 18 to 36 months from requirements definition through design, development, testing, and delivery. A program that began defining requirements in early 2025 and enters the build phase now will deliver a system in late 2027 or early 2028. If that system does not support CNSA 2.0 algorithms at delivery, it arrives non-compliant. The remediation is not a patch or a configuration change; it is a redesign of the cryptographic architecture, potentially requiring new hardware if the original components cannot support the larger key sizes and ciphertexts that ML-KEM-1024 and ML-DSA-87 produce.
The acquisition gate works by shifting the compliance burden upstream. In a traditional compliance model, systems are built, deployed, and then assessed against requirements during operation. CNSA 2.0 reverses this: the requirement attaches at procurement, before the system exists in operational form. This means program managers writing requirements documents in 2025 and 2026 must specify CNSA 2.0 algorithm support. Contracting officers evaluating proposals must verify CNSA 2.0 capability. Vendors must demonstrate validated implementations before contract award.
For the broader US PQC regulatory framework, CNSA 2.0’s January 2027 gate is the sharpest enforcement point. While civilian agency PQC mandates have become more discretionary following the current administration’s shift toward agency-level decision-making, CNSA 2.0 operates under a separate governance structure (NSD-42, NSM-8, NSM-10, CNSSP 15) that is independent of executive orders targeting civilian agencies. The defense and intelligence procurement channel remains bound by these deadlines regardless of broader federal policy shifts.
The Five-Month Squeeze
The convergence of three deadlines within five months creates a compounding compliance challenge that cannot be addressed sequentially. Each deadline tightens the constraints for the next.
September 21, 2026: The FIPS 140-2 Sunset
NIST’s Cryptographic Module Validation Program moves all FIPS 140-2 certificates to Historical status on this date. Modules validated under FIPS 140-2 will continue to function (nothing breaks on September 22), but they can no longer be specified for new federal procurement. Only FIPS 140-3 validated modules qualify.
This matters for the PQC transition because post-quantum algorithm implementations must ultimately be validated under FIPS 140-3 to be acceptable for federal (and especially NSS) use. An organization that has not begun the FIPS 140-3 validation process by September 2026 faces a gap that arithmetic makes inescapable: the current CMVP process averages over 500 days from submission to active certificate. OpenSSL 3.5.4, which includes PQC algorithm support, submitted its CMVP application in October 2025. That certificate is unlikely to be active before the January 2027 gate.
The implication is that FIPS 140-3 validation for PQC modules needed to enter the pipeline by late 2024 or early 2025 to have any chance of producing an active certificate by January 2027. Organizations that entered the pipeline on time will have validated modules. Those that did not face a structural gap that no amount of urgency can compress.
November 10, 2026: CMMC 2.0 Phase 2
Phase 2 of the Cybersecurity Maturity Model Certification program begins mandatory third-party assessments (C3PAO) for most Level 2 defense contractors. Control 3.13.11 of NIST SP 800-171 requires “FIPS-validated cryptography when used to protect the confidentiality of CUI.” That phrase, “FIPS-validated,” means a current CMVP certificate: a certificate number in the NIST database tied to a specific module version. Running a system in “FIPS mode” without holding an active certificate does not satisfy the control.
After the September 21 sunset, any organization whose only CMVP certificate is under FIPS 140-2 will find that certificate classified as Historical. A C3PAO assessor evaluating Control 3.13.11 in November or December 2026 will be looking at whether the cryptographic module holds an active FIPS 140-3 certificate. The assessment will not wait for a pending validation to complete.
January 1, 2027: The CNSA 2.0 Gate
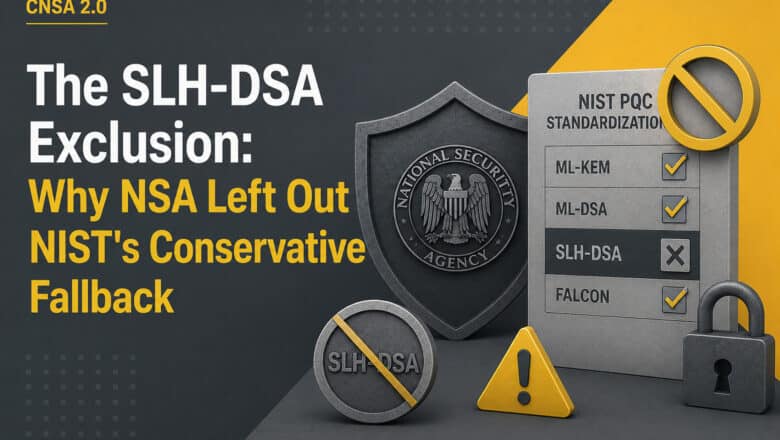
The procurement gate itself. For NSS, the requirement goes beyond FIPS 140-3 validation: products must support CNSA 2.0 algorithms specifically (ML-KEM-1024, ML-DSA-87), and they must be validated by NIAP against updated Protection Profiles. FIPS validation alone is insufficient for NSS; the “NSA-approved” designation requires NIAP validation plus correct configuration per CNSSP 15.
The three deadlines form a dependency chain. Without FIPS 140-3 validation (September gate), you cannot demonstrate CMMC Level 2 compliance (November gate). Without both, plus NIAP validation against CNSA 2.0-updated Protection Profiles, you cannot pass the NSS procurement gate (January gate). Missing the first compounds through the second and third.
The CMVP Bottleneck
The Cryptographic Module Validation Program is the unavoidable checkpoint for any organization that needs FIPS-validated cryptographic modules. And it is, by any honest assessment, a bottleneck.
FIPS 140-3 validations averaged 542 days from submission to active certificate as of early 2024, according to analysis published by Keypair.us. The average has increased since then, not decreased. NIST has acknowledged the queue issue and is exploring ways to streamline the process, but no structural reform has shortened the timeline for modules currently in the pipeline.
For post-quantum specifically, the challenge is that ML-KEM and ML-DSA implementations are new to the CMVP process. The Automated Cryptographic Validation Testing System (ACVTS) has added tests for these algorithms, but the full module validation goes beyond algorithm testing to include physical security, key management, self-tests, and operational environment assessment. A vendor cannot shortcut this process by having CAVP (algorithm-level) certificates alone. CAVP demonstrates algorithm correctness; CMVP validates the entire module.
There is one practical concession in the CNSA 2.0 guidance that eases the near-term pressure slightly. For commercial products that only perform signature verification (as opposed to generation), CAVP testing is sufficient. Since most end-user products in NSS will verify firmware signatures rather than generate them, this means CAVP-validated LMS or XMSS verification can satisfy the firmware signing requirement without full CMVP validation. The generation side, however, which runs on HSMs and signing infrastructure, requires full CMVP validation with no exceptions.
Organizations that recognized this constraint in 2024 and entered the CMVP pipeline early will have an advantage that late movers cannot replicate. The queue is a fixed resource, and joining it in mid-2026 means receiving a certificate sometime in 2028. For the January 2027 gate, that is too late.
The Upstream Cascade
The traditional mental model of compliance treats it as something that happens after a system is built: deploy, assess, remediate. The January 2027 gate inverts this. Compliance must be designed in, not bolted on, because the assessment happens at procurement rather than at deployment.
This inversion pushes the compliance burden backward through the supply chain in a specific sequence.
Vendors must have CNSA 2.0-capable products with validated implementations shipping by mid-2026 at the latest. A product that adds ML-KEM-1024 support in a Q3 2026 release cannot realistically be FIPS 140-3 validated, NIAP-evaluated, and included in a government acquisition package before January 2027.
System integrators must verify that every component in their solutions (operating systems, networking equipment, HSMs, PKI infrastructure, TLS libraries) supports CNSA 2.0 algorithms. A system integration proposal that specifies a single component without CNSA 2.0 support risks disqualification of the entire solution.
Prime contractors must flow CNSA 2.0 requirements down to sub-tier suppliers. A sub-contractor providing an embedded module that handles cryptographic operations must meet the same algorithm and validation requirements as the prime. Primes that have not issued supplier directives specifying CNSA 2.0 compliance are creating risk for programs delivering after January 2027.
Program offices must update requirements documents, solicitations, and evaluation criteria to include CNSA 2.0 as a mandatory capability. RFPs being written now for systems that will deliver in 2027 or 2028 must include these requirements, or the resulting systems will arrive non-compliant.
The cascade also reaches organizations that may not think of themselves as part of the NSS ecosystem. A commercial cloud provider whose platform is used by a defense agency for a classified workload becomes subject to CNSA 2.0 through that usage. A SaaS vendor whose product processes data in an NSS-adjacent environment inherits the requirement through the system boundary. The supply chain for National Security Systems extends further than many commercial vendors realize.
The PKI Challenge
Algorithm migration at the protocol level is the visible part of the CNSA 2.0 transition. Adding ML-KEM-1024 to a TLS 1.3 handshake or integrating ML-DSA-87 into an IKEv2 key exchange is engineering work with clear specifications and available reference implementations. This is the tractable part.
The harder problem is certificate infrastructure. Deploying ML-DSA-87 in a production PKI environment means that Certificate Authorities must issue, manage, rotate, and revoke certificates using algorithms that produce signatures and public keys far larger than their classical equivalents. An ML-DSA-87 signature is roughly 4,600 bytes; an ML-DSA-87 public key is approximately 2,600 bytes. Compare that to ECDSA P-384, where a signature is 96 bytes and a public key is 97 bytes. These larger sizes affect certificate chain validation, OCSP response sizes, CRL distribution, and the bandwidth of every TLS handshake that carries these certificates.
For large-scale enterprise PKI, the operational questions multiply. Can existing HSMs generate and store ML-DSA keys at scale? Can certificate lifecycle management tools handle the new key types? Will embedded devices and legacy appliances that perform certificate validation ever receive firmware updates that add ML-DSA verification support?
The practical bridge for most organizations is a hybrid certificate strategy. Three approaches are converging in the industry: composite signatures (one certificate carrying both a classical and a post-quantum signature in a single X.509 field), catalyst certificates (a parallel PQC certificate chain that coexists with the classical chain), and cross-signing (classical and PQC CA hierarchies that cross-certify each other). Each has trade-offs in complexity, backward compatibility, and tooling maturity.
The organizations that are on track for the January 2027 gate have already begun hybrid certificate pilots. Those that have not will discover that PKI migration is the long pole in the CNSA 2.0 tent: slower, more complex, and more operationally disruptive than protocol-level algorithm substitution.
What “On Track” Looks Like
The organizations positioned to clear the January 2027 gate share a recognizable posture. They have completed a cryptographic inventory across every product line that touches or could touch National Security Systems. They hold CAVP certificates for ML-KEM-1024 and ML-DSA-87 implementations and have FIPS 140-3 module submissions in the CMVP pipeline. They have LMS or XMSS firmware-signing pilots running in production or near-production environments. They are characterizing the performance impact of post-quantum TLS handshakes, measuring the latency and bandwidth effects of larger certificates and key exchanges before committing to production rollout parameters.
Their procurement teams have updated solicitation templates to require CNSA 2.0 capability from vendors. Their engineering teams have characterized the impact of ML-DSA-87 signature sizes on their certificate infrastructure and developed hybrid deployment strategies. Their compliance teams understand the interaction between FIPS 140-3 sunset, CMMC enforcement, and the CNSA 2.0 gate, and have mapped each deadline to specific evidence requirements.
The organizations that will miss the gate look different. They are still framing CNSA 2.0 as a 2030 or 2035 concern, focused on the later “exclusive use” milestones rather than the procurement gate. They have not entered the CMVP pipeline. They are waiting for their cryptographic library vendor to ship PQC support without verifying the validation timeline. They are treating the January 2027 date as a deployment deadline rather than a procurement deadline, missing the distinction that determines whether their products can even be specified in an acquisition.
The Deadlines Are Set
I have made this argument many times on PostQuantum.com, and CNSA 2.0’s January 2027 gate is the most concrete example of why it holds: the reason to act on PQC is not a prediction about when a quantum computer will break cryptography. The reason to act is the ecosystem of deadlines that are already locked in.
Whether a cryptanalytically relevant quantum computer arrives in 2032 or 2042, the January 2027 acquisition gate arrives in eight months. The FIPS 140-2 sunset arrives in four months. The CMMC enforcement phase begins in six months. These dates are not contingent on quantum computing progress. They are contingent on calendars, procurement cycles, and validation queues.
For organizations beginning their PQC migration, the PQC Migration Framework provides a structured methodology that works regardless of whether the driver is CNSA 2.0, commercial risk, or customer requirements. The Practical Steps to Quantum Readiness guide covers the first concrete actions. And for the strategic-level question (how to make the case to a board or executive team that this migration cannot wait), Quantum Ready addresses the organizational dimension directly.
The January 2027 date is not the end of the CNSA 2.0 transition. Harder milestones follow: exclusive use for networking equipment by 2030, mandatory algorithms across all NSS by 2031, full migration by 2035. But January 2027 is the gate that determines who is in the game and who is watching from outside it. The procurement contracts being signed through the remainder of 2026 will determine what gets delivered after that gate closes. For anyone selling into the defense and intelligence ecosystem, the eight months between now and January 1, 2027, are the most consequential eight months in the history of U.S. cryptographic policy.
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.