What Is Quantum Computing Security?

Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
Quantum computing security covers two related challenges. The first, and far more urgent, is protecting existing digital infrastructure against the cryptographic threats that quantum computers will pose. The second is securing quantum computing systems themselves as they become operational infrastructure. For security leaders, the first challenge demands action now; the second is emerging.
What Quantum Computers Will Break
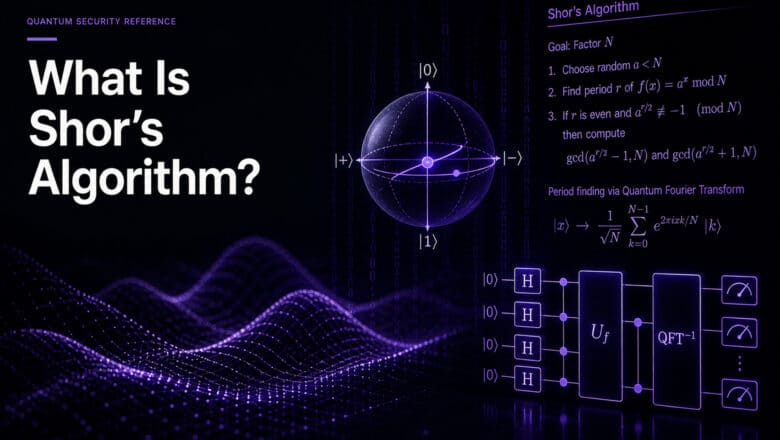
The threat is specific. Quantum computers running Shor’s algorithm can efficiently solve the mathematical problems that underpin today’s public-key cryptography. RSA’s security rests on the difficulty of factoring large integers. ECC relies on the discrete logarithm problem over elliptic curves. Diffie-Hellman key exchange depends on a related structure. Shor’s algorithm handles all three.
The practical consequence: once a Cryptographically Relevant Quantum Computer (CRQC) exists, an attacker could decrypt TLS sessions, forge digital signatures, compromise VPN tunnels, and undermine PKI hierarchies. The scope of impact is hard to overstate because public-key cryptography is woven into nearly every protocol and system that enterprises rely on.
Grover’s algorithm poses a separate, less severe threat to symmetric cryptography. It effectively halves the security level of algorithms like AES: AES-256 drops to roughly AES-128 equivalent strength, and AES-128 drops to AES-64 (no longer secure). The mitigation is straightforward: use AES-256 and you retain adequate security margins. I cover the nuances in my analysis of why “just ignore Grover’s” is almost right.
Hash functions fare better still. SHA-256 and SHA-3 lose some security margin under Grover’s, but remain practically secure. This is why SLH-DSA, the hash-based PQC signature standard, offers such strong long-term assurance.
What They Cannot Break (Yet)
Understanding the limits of quantum attack is as important as understanding the threats, particularly for cutting through quantum fear-mongering and Q-FUD.
No quantum computer has factored a cryptographically meaningful number. As I detail in my analysis of what quantum computers have actually factored, the largest integers factored by Shor’s algorithm on real quantum hardware are trivially small. The gap between factoring these toy numbers and breaking RSA-2048 remains enormous.
Current quantum machines operate with a few thousand noisy physical qubits. Breaking RSA-2048 requires, by the most optimistic published estimate, under one million physical qubits running for under a week with error rates far below what any current hardware achieves. A CRQC capable of this must simultaneously demonstrate mastery of quantum error correction, below-threshold operation, real-time decoding, and sustained continuous operation over the full computation.
None of these capabilities exist at the required scale today. All of them are advancing.
The Timeline Question
My CRQC Quantum Capability Framework tracks ten distinct capabilities that must converge before a quantum computer can threaten real-world cryptography. The framework provides a more granular assessment than single-number predictions because it shows which capabilities are progressing rapidly and which remain stubborn engineering challenges.
The resource estimates have been trending in one direction. In 2021, the best estimate for breaking RSA-2048 was 20 million physical qubits. By 2025, Gidney’s updated analysis reduced that to under one million. The Pinnacle architecture pushed the theoretical floor below 100,000. ECC is potentially more vulnerable than RSA, with Google’s March 2026 research suggesting fewer than 500,000 superconducting qubits could break ECC-256.
My own detailed analysis points toward RSA-2048 being broken by 2030, though I hold that estimate with appropriate uncertainty. More importantly, as I have argued at length, the timeline debate is increasingly beside the point. Regulatory and commercial deadlines for PQC migration are already fixed, and those are the timelines security leaders should plan against.
Securing Quantum Computers Themselves
The second dimension of quantum computing security receives less attention but will grow in importance as quantum computers become operational infrastructure.
Quantum computers are hybrid systems. The quantum processor operates at millikelvin temperatures inside a dilution refrigerator, but it is controlled by classical electronics: FPGAs, microwave generators, readout circuitry, and conventional networking. The quantum-classical interface is where security vulnerabilities emerge. Attacks against the classical control stack can manipulate quantum computations without ever touching the quantum hardware. Calibration data injection, firmware tampering on control electronics, and side-channel leakage from readout signals are all active research areas in quantum hacking.
As quantum-as-a-service platforms expand and enterprises begin using quantum processors through cloud APIs, the attack surface will resemble classical cloud security in some ways and diverge in others. The controls, monitoring, and access management frameworks for quantum computing infrastructure are still being developed. For security teams, the immediate action is awareness; the operational requirements will crystallize as the technology matures.
The Defense: Post-Quantum Cryptography
The primary defense against the quantum computing threat to classical systems is post-quantum cryptography (PQC). NIST finalized three PQC standards in August 2024 (ML-KEM, ML-DSA, SLH-DSA), with two more in progress. The migration to these standards is the operational translation of everything described above into a concrete security program.
For organizations wondering where to start, the Applied Quantum PQC Migration Framework and my practical steps guide provide the entry point.
Go Deeper
Q-FUD: The Quantum Panic Industry — how to separate signal from hype
The Quantum Computing Threat — full analysis of how quantum computers threaten cybersecurity
Are Quantum Computers a Real Threat? — evidence-based assessment for skeptics
CRQC Quantum Capability Framework — ten capabilities on the path to a CRQC
Quantum Breakthrough for RSA-2048 (Gidney 2025) — the latest resource estimate
Securing Quantum Computers — threats at the quantum-classical interface
Quantum Hacking — cybersecurity of quantum systems
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.