What Is Q-Day?

Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
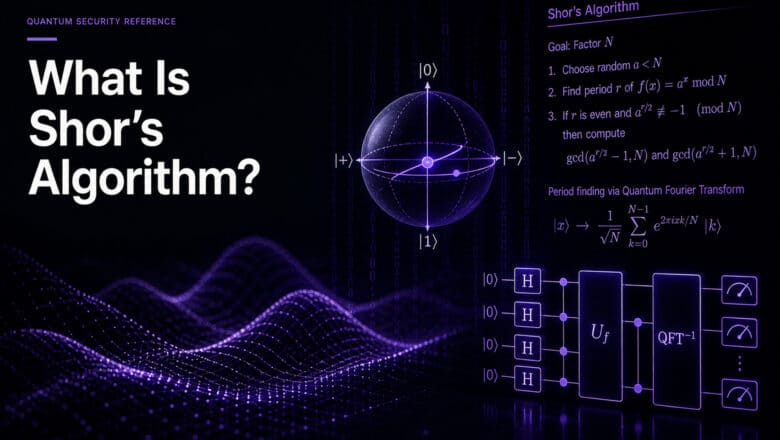
Q-Day (sometimes called Y2Q) is the hypothetical future date when a quantum computer becomes capable of breaking the public-key cryptographic systems that protect digital communications worldwide. On Q-Day, RSA, Elliptic Curve Cryptography, and Diffie-Hellman key exchange would all become vulnerable to Shor’s algorithm, and the encryption protecting everything from banking transactions to government secrets would no longer hold.
What Would Actually Happen
Q-Day is sometimes imagined as a sudden, dramatic collapse, a digital Pearl Harbor where systems fail simultaneously. The reality would be different and in some ways worse. I explore this in detail in my analysis of what will really happen when Q-Day arrives.
The most likely scenario is a gradual erosion of trust rather than a single catastrophic event. A CRQC powerful enough to break cryptography would initially be a closely guarded national security asset, not a publicly announced capability. The first organizations to realize their encryption has been compromised may not know it for months or years. Adversaries with quantum decryption capability would have every incentive to use it quietly, extracting intelligence without revealing the capability itself.
The second-order effects are where the damage compounds. Once the existence of a CRQC becomes public knowledge (or widely suspected), confidence in digital infrastructure collapses. Certificate authorities, digital signatures, software update mechanisms, and identity systems all depend on public-key cryptography. The question shifts from “has my data been compromised?” to “can I trust anything that was signed or encrypted before the transition?” That crisis of trust may prove more disruptive than any specific data breach.
The Timeline Debate
Q-Day predictions span a wide range. Expert and institutional estimates cluster between 2030 and 2045, with outliers in both directions. My own detailed analysis points toward RSA-2048 being broken by 2030, though I hold that estimate with appropriate uncertainty and have written extensively about the trouble with Q-Day predictions in general.
The prediction challenge is structural. Quantum computing progress depends on engineering breakthroughs that are inherently difficult to forecast. A single advance in quantum error correction or qubit architecture could compress the timeline by years. Conversely, an unforeseen physical barrier could extend it by decades. Anyone claiming precision about Q-Day is selling certainty they do not possess. I cover the methodology for making honest estimates in my guide on how to predict Q-Day.
Why the Debate Is Becoming Irrelevant
This is the argument I consider most important for security leaders, and one I have made at length: the exact arrival date of Q-Day matters less with each passing year, because the ecosystem has imposed its own deadlines.
NIST’s draft IR 8547 deprecates RSA and ECC for federal systems by 2030 and disallows them by 2035. NSA’s CNSA 2.0 requires quantum-resistant algorithms for new National Security System acquisitions by January 2027. Google and Cloudflare have both committed to PQC migration by 2029. The EU’s NIS2 and DORA frameworks create cryptographic risk obligations that increasingly encompass quantum preparedness.
These are not predictions. They are compliance deadlines, procurement requirements, and contractual obligations. An organization that fails to migrate by 2030 faces regulatory consequences regardless of whether a CRQC exists by then.
The Harvest Now, Decrypt Later (HNDL) threat adds another dimension: data captured today is already at risk of future decryption, so the effective deadline for protecting long-lived data is not Q-Day itself but Q-Day minus the data’s remaining confidentiality requirement. For many organizations, that calculation puts the effective deadline in the past.
Q-Day vs. Y2K
The comparison to Y2K is tempting but imperfect. Y2K had a fixed, known date. Q-Day does not. Y2K affected a specific class of date-handling code. Q-Day affects all public-key cryptography. Y2K was largely solved before the deadline through a massive coordinated effort. Q-Day migration is still in its early stages for most organizations.
The useful parallel is the lead time. Y2K preparation took the better part of a decade for large enterprises, and organizations that started late paid a steep premium. PQC migration is expected to take three to eight years for complex organizations. The clock is running.
What to Do Now
Stop debating Q-Day and start migrating. The Applied Quantum PQC Migration Framework provides the methodology. My practical steps guide covers the first concrete actions. The PQC Readiness Self-Assessment Scorecard tells you where you stand today.
For a comprehensive treatment of the Q-Day question, my Q-Day Knowledge Center collects every analysis I have published on the topic.
Go Deeper
Q-Day Confidence Crisis — why trust collapse may be worse than the breach
What Is Q-Day (Y2Q)? — full Q-Day explainer
What Will Really Happen When Q-Day Arrives? — scenario analysis
Q-Day Deadlines Are Set — why ecosystem deadlines matter more than predictions
Q-Day vs. Y2K — the comparison and its limits
Q-Day Predictions — the trouble with forecasting
Q-Day Revisited: RSA-2048 Broken by 2030 — my own detailed timeline analysis
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.