What Is PQC Migration?

Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
PQC migration is the process of replacing the classical public-key cryptographic algorithms (RSA, ECC, Diffie-Hellman) embedded throughout an organization’s infrastructure with the post-quantum cryptographic (PQC) standards finalized by NIST. It touches every system, protocol, certificate, key, and vendor relationship that relies on public-key cryptography. I have described it as the largest, most complex cryptographic overhaul in IT history, and the experience of organizations that have begun confirms that assessment.
Why It Takes Years
PQC migration is not a software patch. Replacing a cryptographic algorithm changes key sizes, signature sizes, handshake latencies, certificate chain structures, and protocol behaviors. These changes ripple through every layer of the technology stack.
A large enterprise program spans upwards of 120,000 discrete tasks across network infrastructure (TLS termination, VPN gateways, load balancers), application code (cryptographic library calls, key handling, signature verification), PKI hierarchies (root certificates, intermediates, leaf certificates, certificate revocation), key management systems, hardware security modules, embedded devices and IoT, operational technology, and vendor-supplied systems where you depend on someone else’s migration timeline.
The SHA-1 to SHA-2 migration offers a useful precedent. That transition involved replacing a single hash algorithm across the PKI ecosystem, and it took the industry over a decade to complete. PQC migration is broader in scope (multiple algorithm families, larger parameter changes, more severe performance impacts) and operates under harder deadlines.
NIST estimates that a large federal agency migration takes three to five years once fully resourced. Enterprise estates with legacy complexity, global operations, and diverse vendor dependencies should plan for the upper end of that range.
The Phases
Migration follows a structured progression. The Applied Quantum PQC Migration Framework formalizes this into a methodology; here is the essential sequence.
Discovery comes first. A cryptographic inventory identifies every instance of quantum-vulnerable cryptography across the organization. The output should be a Cryptographic Bill of Materials (CBOM) that maps algorithms to systems, protocols, vendors, and data flows. Without this inventory, prioritization is guesswork. If a comprehensive inventory is not immediately feasible, risk-driven strategies allow you to begin with the highest-exposure systems.
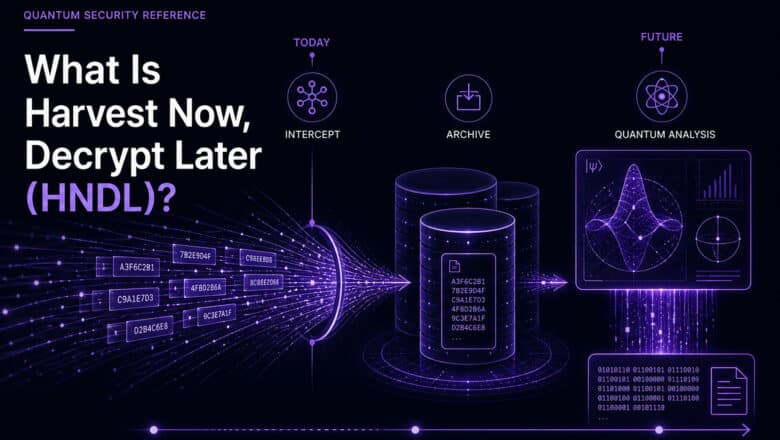
Risk assessment follows. Not all systems carry equal urgency. The HNDL threat makes systems handling long-lived confidential data the highest priority. The TNFL threat makes signature infrastructure (code signing, certificate issuance, legal document signing) a close second. Mosca’s inequality provides the mathematical framework for determining which systems are already past their safe migration window.
Planning translates the inventory and risk assessment into a sequenced migration roadmap. My first-year planning guide covers how to scope, resource, and govern the program. Key decisions at this stage include whether to deploy hybrid cryptography (running classical and PQC algorithms in parallel) or migrate directly to PQC-only configurations.
Execution is the longest phase. It involves deploying NIST-standardized algorithms across each system in the prioritized sequence, testing for performance impacts (PQC algorithms use larger keys and signatures that affect network protocols and bandwidth-constrained systems), updating vendor-supplied systems as PQC-ready versions become available, and validating that migrated systems interoperate correctly.
Ongoing management is permanent. Crypto-agility ensures you can adapt as PQC standards evolve, new algorithms are standardized, and potential vulnerabilities emerge. Migration is not a one-time event; it is the beginning of continuous cryptographic lifecycle management.
The Deadlines
The migration timeline is not optional for organizations in regulated sectors. NIST’s draft IR 8547 deprecates RSA, ECDSA, and Diffie-Hellman for federal systems by 2030 and disallows them by 2035. NSA’s CNSA 2.0 requires quantum-resistant algorithms for new National Security System acquisitions by January 2027. In Europe, NIS2 and DORA create parallel obligations.
As I have argued throughout PostQuantum.com, these deadlines are already set. Organizations starting in 2026 are on schedule. Organizations starting in 2028 will be compressed. Waiting until 2030 means missing the first hard deadlines entirely.
Where to Start
The Applied Quantum PQC Migration Framework provides the structured, open-source methodology. My practical steps guide maps the first concrete actions for cybersecurity teams. The PQC Readiness Self-Assessment Scorecard tells you where you stand today. And for a comprehensive treatment of organizational readiness strategy, my forthcoming book Quantum Ready covers the full picture.
Go Deeper
Infrastructure Challenges of PQC — what larger keys mean for real systems
Quantum Readiness / PQC Migration — why this is the largest cryptographic overhaul ever
120,000 Tasks: Why PQC Migration Is Enormous — full program plan breakdown
Planning the First Year — scoping and governance
Practical Steps to Quantum Readiness — where to start
Cryptographic Inventory — the foundation of migration
PQC Challenges — what makes migration difficult
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.