What Is Grover’s Algorithm?
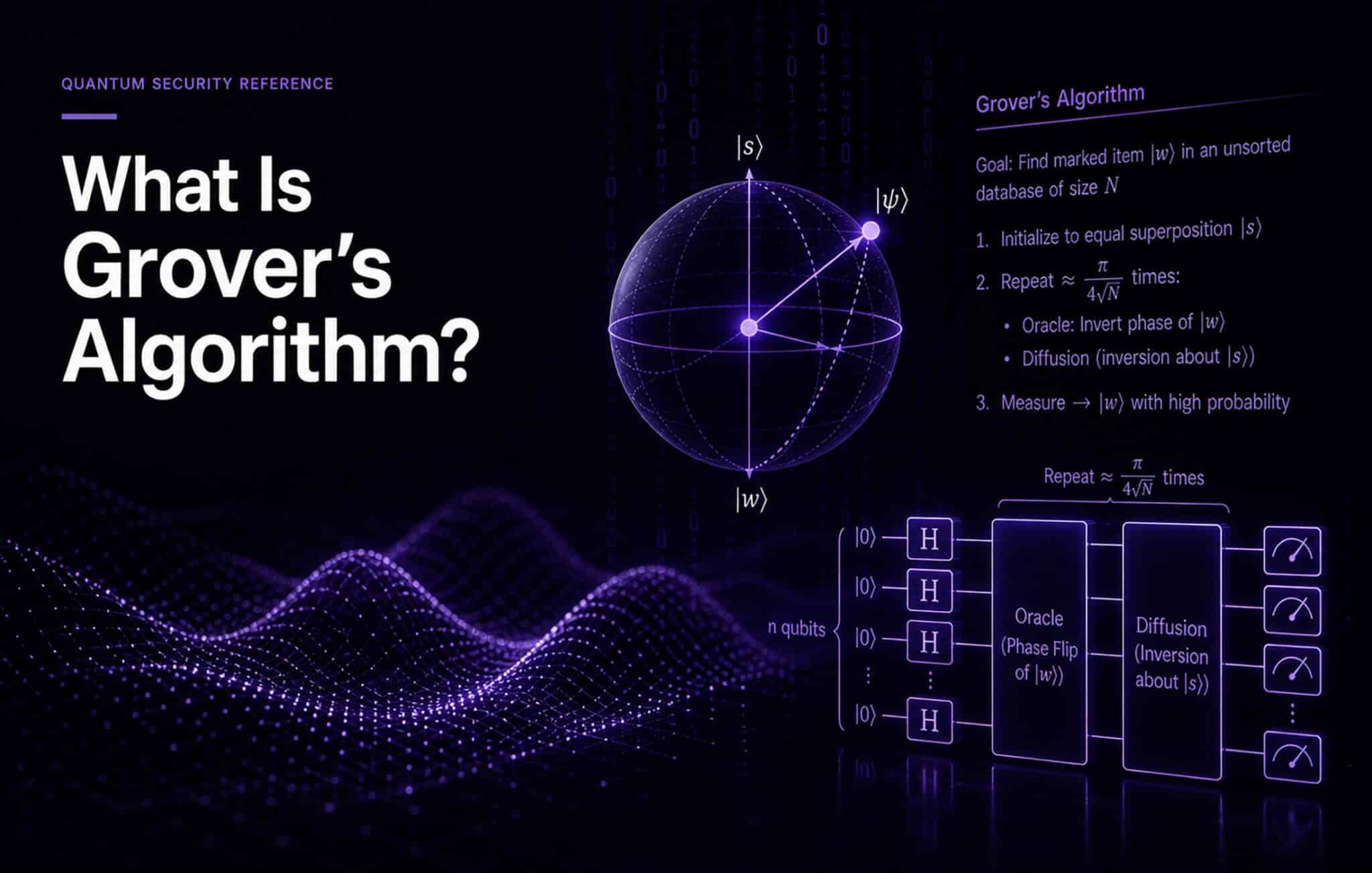
Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
Grover’s algorithm is a quantum algorithm that searches an unstructured database quadratically faster than any classical algorithm. In cryptographic terms, this means it can find a symmetric encryption key in roughly the square root of the number of attempts a classical brute-force attack would require. The practical effect: it halves the effective security of symmetric ciphers and hash functions. AES-256 drops to roughly 128-bit equivalent security. AES-128 drops to 64-bit equivalent, which is no longer considered secure.
How It Works (Without the Math)
Classical brute-force key search is straightforward: try every possible key until one works. For a 256-bit key, that means trying up to 2²⁵⁶ combinations, a number so large that no classical computer could exhaust it before the heat death of the universe.
Grover’s algorithm exploits quantum superposition and interference to search this space more efficiently. Instead of checking keys one at a time, it evaluates many possibilities in parallel through quantum superposition, then uses a technique called amplitude amplification to progressively increase the probability of measuring the correct key. After roughly √N operations (where N is the total number of possibilities), the correct key emerges with high probability.
For AES-256, this means roughly 2¹²⁸ quantum operations instead of 2²⁵⁶ classical ones. For AES-128, it means 2⁶⁴ quantum operations instead of 2¹²⁸ classical ones. That distinction matters enormously. 2¹²⁸ operations remains computationally infeasible even on a quantum computer. 2⁶⁴ operations is within reach.
Why It Is Less Urgent Than Shor’s
Shor’s algorithm breaks public-key cryptography entirely. A quantum computer running Shor’s does not merely weaken RSA or ECC; it renders them worthless. The security drops from computationally infeasible to trivially solvable.
Grover’s effect is gentler. It degrades symmetric security by a factor of two in the exponent, which means the mitigation is correspondingly simple: use longer keys. AES-256 already provides a sufficient security margin against Grover’s. This is why NIST’s PQC security categories use AES-128 (Category 1) and AES-256 (Category 5) as reference benchmarks for post-quantum security levels.
The organizational implication is clear. If your symmetric encryption already uses AES-256, the quantum threat from Grover’s is managed. If you are still running AES-128 in any critical system, that should be upgraded regardless of quantum timelines, since 64-bit effective security is inadequate against well-resourced adversaries even without a quantum computer.
Why “Just Double Your Key Lengths” Is Almost Right
The advice to double symmetric key lengths as a quantum countermeasure is accurate in principle and insufficient in practice, for reasons I explore in my analysis of why “just ignore Grover’s” is almost right.
The first complication is that Grover’s algorithm requires a fault-tolerant quantum computer with enough qubits to implement the cipher as a reversible quantum circuit. For AES-256, this means constructing the entire AES block cipher inside a quantum computer, which demands substantial qubit resources and long coherence times. The practical overhead makes a Grover’s attack on AES-256 far more expensive than the simple 2¹²⁸ operation count suggests. Some researchers have estimated that a Grover’s search against AES-256 would require a quantum computer so large and running for so long that it may never be economically rational.
The second complication involves hash functions. Grover’s algorithm also applies to finding preimages and collisions in hash functions, though the impact differs. Preimage resistance of SHA-256 drops from 256 bits to 128 bits (still secure). Collision resistance is affected by a related quantum algorithm, the Brassard-Høyer-Tapp (BHT) algorithm, which provides a cube-root speedup for collision finding. SHA-256’s collision resistance drops from 128 bits (by the birthday bound) to roughly 85 bits under BHT, which is marginal. For applications requiring long-term collision resistance, SHA-384 or SHA-512 provides additional margin.
The third complication is that the “double your key length” advice focuses on the algorithm in isolation, ignoring the protocol and implementation. A protocol that uses AES-256 for data encryption but relies on ECDH for key agreement is not quantum safe: Shor’s breaks the key agreement, and the strength of the symmetric cipher becomes irrelevant. Grover’s is only the secondary threat; fixing it without fixing the Shor’s vulnerability accomplishes nothing.
What Security Leaders Should Take Away
Grover’s algorithm is real and relevant, but it does not demand the same urgency as Shor’s. The migration priority for any organization is post-quantum cryptography for public-key systems. The symmetric side requires verification (confirm AES-256 is deployed everywhere it matters, upgrade AES-128 where it persists) rather than wholesale replacement.
NIST’s PQC standards address the Shor’s threat. AES-256 addresses the Grover’s threat. Together, they constitute a quantum-safe posture for symmetric and asymmetric cryptography.
Go Deeper
What Is Shor’s Algorithm? — the more urgent quantum cryptographic threat
Grover’s Algorithm and Its Impact on Cybersecurity — full technical deep dive
Grover’s Algorithm vs AES: Why “Ignore It” Is Almost Right — detailed analysis of the practical threat
Brassard-Høyer-Tapp (BHT) Quantum Collision Algorithm — the quantum threat to hash functions
NIST PQC Security Strength Categories (1–5) — how NIST benchmarks post-quantum security
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.