What Is Quantum Cryptography?
Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
Quantum cryptography is the use of quantum physics to perform cryptographic tasks. Its primary application is distributing encryption keys in a way that makes eavesdropping physically detectable. Its best-known application is quantum key distribution (QKD), which allows two parties to share a secret key with security guaranteed by the laws of physics rather than by the difficulty of a mathematical problem.
The term causes widespread confusion because it sounds like it should mean the same thing as post-quantum cryptography (PQC). It does not. PQC refers to new mathematical algorithms designed to resist quantum attack, running on classical hardware. Quantum cryptography uses quantum hardware (photon sources, detectors, quantum channels) to perform the cryptography itself. The two fields address the same underlying threat, the eventual arrival of a CRQC, but they solve it in entirely different ways.
How Quantum Cryptography Works
The core principle is elegant. Quantum mechanics dictates that measuring a quantum state disturbs it. If two parties exchange information encoded in quantum states (typically single photons), any third party who intercepts and measures those photons will introduce detectable errors. The sender and receiver can then check for these disturbances and know whether their key exchange was compromised.
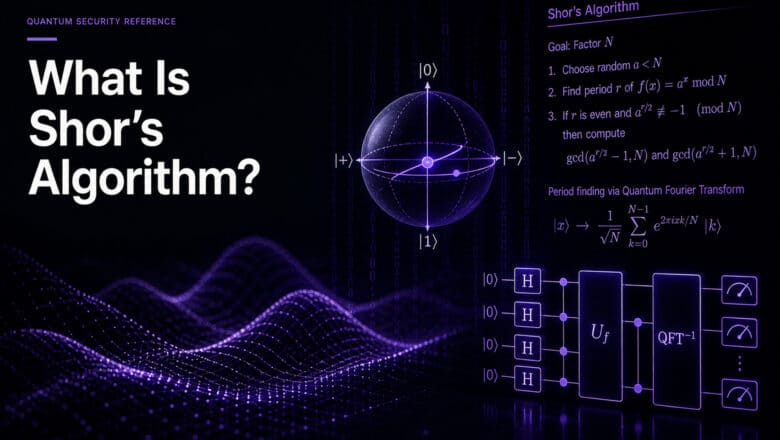
The BB84 protocol, proposed by Charles Bennett and Gilles Brassard in 1984, was the first practical QKD scheme and remains the most widely implemented. It encodes key bits in the polarization states of individual photons, using two randomly chosen measurement bases. An eavesdropper who measures the photons must guess which basis was used; guessing wrong corrupts the data in a statistically detectable way. After the quantum transmission, the two parties compare a subset of their results over a classical channel. If the error rate is below a threshold, they can be confident no one intercepted the exchange.
Since BB84, the field has expanded considerably. Entanglement-based protocols like E91 and BBM92 use correlated photon pairs to distribute keys, offering different security assumptions. Device-independent QKD goes further, providing security guarantees that hold even if the hardware itself is untrusted. I cover the full range of emerging approaches in my analysis of next-generation QKD protocols.
The Security Guarantee and Its Limits
The theoretical security of QKD is grounded in physics, not computational hardness. No future mathematical breakthrough or increase in computing power (classical or quantum) can break a properly implemented QKD system, because the security follows from the laws of quantum mechanics themselves. This is called information-theoretic security, and no classical or post-quantum algorithm can offer the same guarantee.
The operative phrase, though, is “properly implemented.” QKD’s information-theoretic guarantees apply to the protocol as a mathematical abstraction. The hardware that implements the protocol (photon sources, detectors, modulators, fiber-optic channels) is classical equipment subject to classical engineering vulnerabilities. Side-channel attacks against QKD implementations have been demonstrated repeatedly in the research literature. Imperfect single-photon sources, detector blinding attacks, and timing correlations have all been exploited to extract key material without triggering the protocol’s eavesdropping detection.
This distinction between theoretical perfection and implementation reality is central to the ongoing debate about QKD’s role in national security strategies.
The Geopolitical Split
Countries disagree sharply on whether QKD should be a priority investment for quantum security. The disagreement is not primarily technical; it reflects different strategic calculations about infrastructure, sovereignty, and threat models.
China has invested more heavily in operational QKD infrastructure than any other country. The Beijing-Shanghai quantum communication backbone spans over 2,000 kilometers of dedicated fiber, and the Micius satellite has demonstrated intercontinental quantum key distribution from orbit. China’s approach treats QKD as critical national infrastructure, tightly integrated with its broader quantum ambition.
The United States and United Kingdom have taken a more skeptical position. NSA’s CNSA 2.0 guidance explicitly declines to endorse QKD for National Security Systems, pointing to the practical limitations: dedicated fiber requirements, distance constraints, point-to-point topology, and the gap between theoretical and implementation security. The UK’s National Cyber Security Centre has issued similar caution. Both countries direct their quantum security mandates toward PQC migration instead.
Europe sits somewhere between these positions. Several EU member states are building QKD pilot networks through the EuroQCI initiative, while the ENISA guidance and NIS2/DORA frameworks focus compliance requirements on PQC.
Where Quantum Cryptography Fits in Practice
For most organizations, PQC is the primary quantum security defense. The regulatory mandates, the compliance deadlines, and the migration urgency all center on PQC. Organizations that do nothing else should migrate to PQC.
QKD occupies a narrower but genuine role. High-security point-to-point links between data centers, government facilities, or financial institutions can benefit from the physics-based guarantee that QKD provides, especially for data with extremely long confidentiality requirements where even the possibility of a future PQC algorithm compromise is unacceptable. Some organizations are deploying QKD alongside PQC in a layered defense.
Quantum random number generation (QRNG) is another quantum cryptographic technology with broader near-term applicability. QRNG devices use quantum processes to generate truly random numbers, addressing a longstanding weakness in classical random number generators. QRNG is already commercially available and can be integrated into existing cryptographic systems without the infrastructure requirements of QKD.
As quantum networks mature and quantum repeaters extend QKD’s range, the practical applicability of quantum cryptography will expand. But that horizon is measured in years to decades, not months. The PQC migration, by contrast, is happening now.
Go Deeper
- QKD 101: A Guide for Cybersecurity Professionals — comprehensive QKD overview for security practitioners
- QKD and the BB84 Protocol — detailed protocol walkthrough
- Why Countries Differ on QKD’s Future — the geopolitical and technical debate
- Next-Generation QKD Protocols — emerging protocols beyond BB84
- Device-Independent QKD — security without trusting the hardware
- Quantum Networks 101 — the infrastructure connecting quantum devices
- What Is Post-Quantum Cryptography? — the complementary approach using mathematical algorithms
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.