What Is a CRQC (Cryptographically Relevant Quantum Computer)?
Table of Contents
This is part of the Quantum Security Reference Deep Dive series. For the full landscape overview, see the capstone article on quantum security.
Introduction
A Cryptographically Relevant Quantum Computer (CRQC) is a quantum computer powerful and reliable enough to run Shor’s algorithm against real-world cryptographic systems, breaking RSA, ECC, and Diffie-Hellman at the key sizes used in production. No CRQC exists today. Building one requires simultaneous advances across at least ten distinct engineering capabilities. The question is when one will be built, not whether.
How a CRQC Differs from Today’s Machines
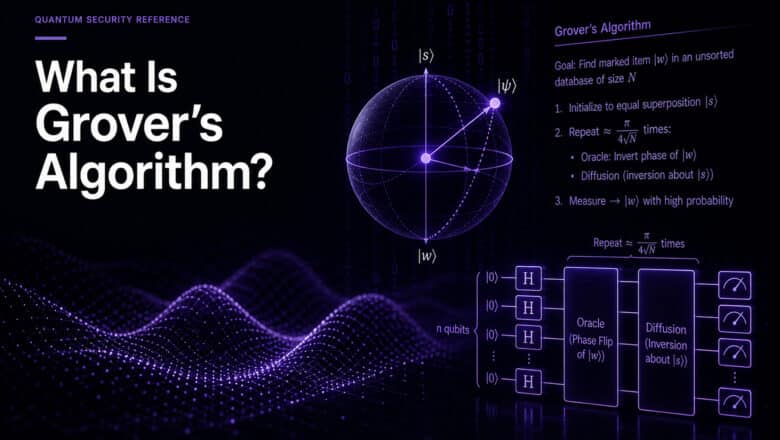
Today’s quantum computers are often described as NISQ devices: Noisy Intermediate-Scale Quantum machines. They operate with hundreds to a few thousand physical qubits, error rates that accumulate rapidly over sequential operations, and coherence times measured in microseconds to milliseconds. They are useful for certain research and optimization problems but cannot sustain the long, deep computations that Shor’s algorithm requires.
A CRQC must operate in a fundamentally different regime. Breaking RSA-2048 requires maintaining roughly 1,400 error-corrected logical qubits through millions of sequential gate operations over hours or days without accumulating fatal errors. Each logical qubit is itself constructed from hundreds or thousands of physical qubits through quantum error correction, meaning the total physical qubit count runs into the hundreds of thousands or millions.
The gap between a NISQ machine and a CRQC is not a matter of adding more qubits to an existing design. It requires qualitative engineering breakthroughs in error correction, control systems, fabrication, and sustained operation. I cover the progression from NISQ through fault-tolerant quantum computing in my analysis of the NISQ to FTQC to FASQ trajectory.
The Ten Capabilities a CRQC Requires
My CRQC Quantum Capability Framework identifies ten engineering capabilities that must converge before a quantum computer can threaten cryptography. The framework exists because single metrics (qubit count, gate fidelity, quantum volume) fail to capture the full picture. A machine with a million physical qubits but inadequate error correction cannot run Shor’s. A machine with perfect error correction but insufficient qubit connectivity cannot execute the algorithm efficiently.
The ten capabilities span four layers. The foundation layer covers quantum error correction, syndrome extraction, below-threshold operation, and qubit connectivity. The computation layer addresses high-fidelity logical gates and magic state production. The integration layer requires full algorithm integration, real-time decoder performance, and continuous long-duration operation. The engineering layer demands manufacturing at scale.
No quantum computing platform has demonstrated all ten simultaneously. Several have made significant progress on individual capabilities. The CRQC Scorecard assesses how close each quantum computing modality (superconducting, trapped ion, neutral atom, photonic, silicon) is to meeting the full set.
Tracking Progress
Two tools on PostQuantum.com are designed to help security leaders track CRQC progress without needing to evaluate individual research papers.
The CRQC Quantum Capability Framework provides the analytical structure. When a new result is published (a new error correction threshold demonstrated, a new qubit connectivity record, a new logical gate fidelity), the framework shows where that result fits in the overall picture and whether it moves the needle toward a CRQC.
The CRQC Readiness Benchmark translates capability progress into timeline estimates. It allows readers to adjust assumptions (error rates, algorithmic improvements, engineering pace) and see how those assumptions affect the estimated arrival date. The methodology behind it is documented in the benchmark methodology paper.
The Resource Estimates
The most concrete way to think about CRQC proximity is through published resource estimates for specific cryptographic attacks.
For RSA-2048, the current best estimate (Gidney, 2025) requires fewer than one million physical qubits and under one week of runtime, assuming surface code error correction with physical error rates of 10⁻³. The Pinnacle architecture using qLDPC codes pushes the theoretical floor below 100,000 physical qubits under optimistic assumptions that have not been validated at scale.
For ECC, the estimates are lower. The Chevignard et al. EUROCRYPT 2026 paper places the P-256 ECDLP at 1,193 logical qubits. Google’s March 2026 analysis estimates fewer than 500,000 superconducting physical qubits could break ECC-256.
These numbers should be interpreted carefully. They assume physical error rates and hardware parameters that no current machine achieves. They also represent a trajectory: five years ago, the RSA-2048 estimate was 20 million physical qubits. The direction is consistent even if the destination date is uncertain.
Why “When” Matters Less Than You Think
My detailed prediction points toward RSA-2048 falling by 2030. Other credible estimates range from the early 2030s to the 2040s. The uncertainty is real and irreducible at this stage of the technology’s development.
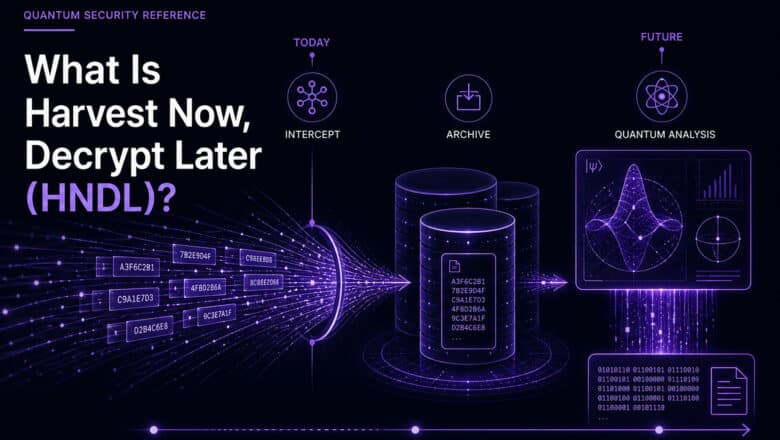
For security planning, however, the exact date is secondary. As I have argued at length, the deadlines for PQC migration are already set by regulators and industry. CNSA 2.0, NIST IR 8547, Google, Cloudflare, and the EU have all established quantum security timelines independent of CRQC predictions. The HNDL threat means that data captured today is already at risk regardless of when a CRQC arrives.
A CRQC will be built. The engineering challenges are immense but finite. The appropriate response is to prepare on the timelines that are certain rather than gamble on the one that is not.
Go Deeper
What Is Q-Day? — the day a CRQC arrives
Cryptographically Relevant Quantum Computers (CRQCs) — full explainer
CRQC Quantum Capability Framework — the ten capabilities a CRQC requires
CRQC Readiness Benchmark — methodology and interactive timeline estimator
CRQC Scorecard by Modality — how close each quantum platform is
From NISQ to FTQC to FASQ — the technology progression
Quantum Breakthrough for RSA-2048 (Gidney 2025) — the latest resource estimate
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.