-
5G Security
What COVID-19 Taught Us About the Need for 5G
There are many adjectives that could be used to describe the global outbreak of COVID-19, but perhaps the simplest might be: fast. The disease has spread quicker than most people can mentally digest. By nature, humans process linearly. This pandemic…
Read More » -
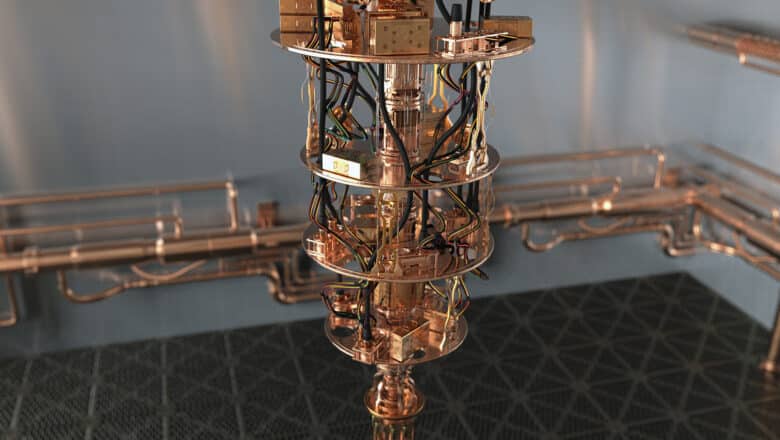
Post-Quantum, PQC, Quantum Security
Entanglement-Based QKD Protocols: E91 and BBM92
While prepare-and-measure QKD currently leads the market due to simplicity and higher key rates, entanglement-based QKD protocols like E91 and BBM92 are at the heart of next-generation quantum communications. Ongoing improvements in photonic technology are steadily closing the gap in…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Key Distribution (QKD) and the BB84 Protocol
Quantum Key Distribution (QKD) represents a radical advancement in secure communication, utilizing principles from quantum mechanics to distribute cryptographic keys with guaranteed security.Unlike classical encryption, whose security often relies on the computational difficulty of certain mathematical problems, QKD's security is…
Read More » -
AI Security
Twitter API for Secure Data Collection in Machine Learning Workflows
While APIs serve as secure data conduits, they are not impervious to cyber threats. Vulnerabilities can range from unauthorized data access and leakage to more severe threats like remote code execution attacks. Therefore, it's crucial to integrate a robust security…
Read More » -
5G Security

Unlocking the Future – Why Virtualization Is the Key to 5G
Depending on who you speak to, 5G is either humankind’s greatest imminent blessing or its greatest imminent curse. Still in its infancy, and not yet commercially standardized, this technology has already been the most polarizing advancement we have ever seen…
Read More » -
Quantum Computing

The Controlled-NOT (CNOT) Gate in Quantum Computing
The CNOT gate is to quantum circuits what the XOR gate is to classical circuits: a basic building block for complex operations. By learning how the CNOT gate works and why it matters, cybersecurity experts can better appreciate how quantum…
Read More » -
5G Security

Will 5G and Society 5.0 Mark a New Era in Human Evolution?
In their outstanding book, Wicked and Wise, Alan Watkins and Ken Wilber look at some of the most pressing ‘wicked problems’ facing the human race. ‘Wicked problems,’ they suggest, are difficult to define, but they are essentially unsolvable in the…
Read More » -
Industry

Switzerland Maps Out a National Quantum Strategy
The Swiss Science Council released a landmark white paper on quantum technologies, outlining a national strategy to capitalize on Switzerland’s strengths in quantum computing, communication, sensing, and cryptography. This roadmap calls for greater coordination and investment across government, academia, and…
Read More » -
5G Security

Opportunity and Cybersecurity in the Age of 5G
The human will to innovate is seemingly relentless. The history of our species is one of continual development, with the last 350 years, in particular, representing staggering technological progress. The first industrial revolution mechanized production using natural elements like water.…
Read More » -
Quantum Computing

Random Circuit Sampling (RCS) Benchmark
At its core, Random Circuit Sampling (RCS) is a way to test how well a quantum computer can generate the output of a complex quantum circuit. Compare the results to what an ideal quantum computer should produce. If the quantum…
Read More » -
5G Security

Collaboration: The Unexpected Key to Success in Canada’s 5G
In 1967, Lynn Margulis, a young biologist, published a paper that challenged more than a hundred years of evolutionary theory. It proposed that millions of years ago, the eukaryotes emerged not from competition, as neo-Darwinism asserts, but from collaboration. Margulis’…
Read More » -
AI Security

The Dark Art of Model Stealing: What You Need to Know
Model stealing, also known as model extraction, is the practice of reverse engineering a machine learning model owned by a third party without explicit authorization. Attackers don't need direct access to the model's parameters or training data to accomplish this.…
Read More » -
Crypto Security

What You Need to Know about the $460M MtGox Hack of 2014
The full story behind the first major crypto hack and how much really was lost. MtGox was one of the very first platforms on which people could buy, sell, and trade bitcoin. Launched in July 2010, by 2014 the Tokyo-based…
Read More » -
Post-Quantum, PQC, Quantum Security

The Quantum Computing Threat
The secret sauce of quantum computing, which even Einstein called "spooky," is the ability to generate and manipulate quantum bits of data or qubits. Certain computational tasks can be executed exponentially faster on a quantum processor using qubits, than on…
Read More » -
Policy & Sovereignty

Inside ITU’s New Quantum Key Standard (Y.3800)
In late 2019, the International Telecommunication Union (ITU) quietly reached a milestone in cybersecurity: it approved a new standard that could redefine how we secure data in the coming quantum era. The standard, known as ITU-T Recommendation Y.3800, is an…
Read More »