-
AI Security
Risks of AI – Meeting the Ghost in the Machine
Because it demands so much manpower, cybersecurity has already benefited from AI and automation to improve threat prevention, detection and response. Preventing spam and identifying malware are already common examples. However, AI is also being used – and will be…
Read More » -
AI Security

Digital Double Helix: Why the Fates of 5G and AI are Intertwined
In 2013, George F. Young and colleagues completed a fascinating study into the science behind starling murmurations. These breathtaking displays of thousands – sometimes hundreds of thousands – of birds in a single flock swooping and diving around each other,…
Read More » -
Quantum Computing

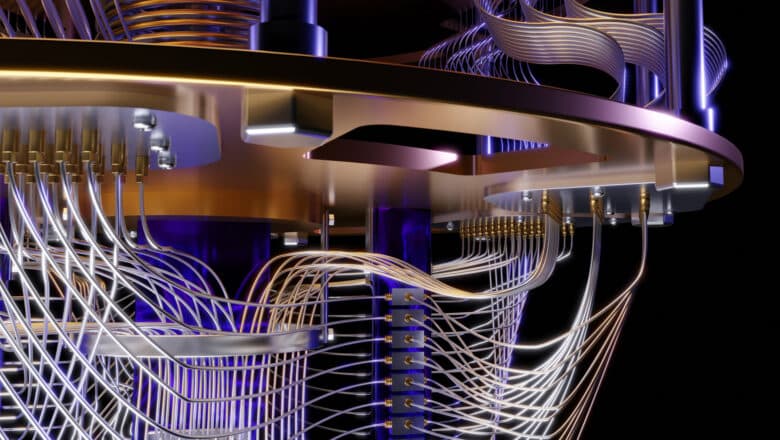
Beyond “Many Paths at Once”: The True Power of Quantum Computers
Quantum computers are often described with a mind-bending metaphor: they explore multiple paths simultaneously to find an answer. You might have heard people excitedly say that a quantum computer can "try all solutions at once" thanks to quantum magic. This…
Read More » -
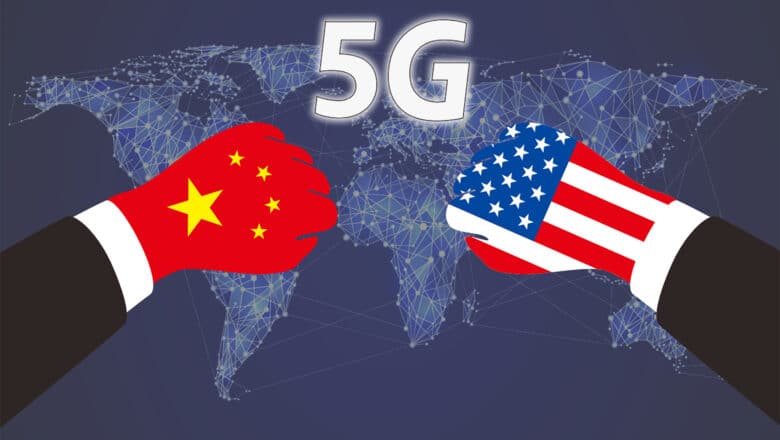
5G Security

5G Critical Infrastructure – the Most Critical of All
Not even 30 years separate us from the end of the Cold War. Yet, we appear to be witnessing the emergence of a new one, a technology Cold War between the United States and China. This time, instead of a…
Read More » -
5G Security

Telcos Should Take Risks to Jumpstart the 5G Ecosystem
5G connectivity burst onto the world stage at last year’s Winter Olympics in Seoul, South Korea and gained pop culture visibility again at the April 2019 NCAA Final Four men’s college basketball games in Minneapolis. Why the rush to 5G…
Read More » -
Q-Day

Q-Day (Y2Q) vs. Y2K
In the late 1990s, organizations worldwide poured time and money into exorcising the “millennium bug.” Y2K remediation was a global scramble. That massive effort succeeded: when January 1, 2000 hit, planes didn’t fall from the sky and power grids stayed…
Read More » -
Quantum Computing

What’s the Deal with Quantum Computing: Simple Introduction
Quantum computing holds the potential to revolutionize fields where classical computers struggle, particularly in areas involving complex quantum systems, large-scale optimization, and cryptography. The power of quantum computing lies in its ability to leverage the principles of quantum mechanics—superposition and…
Read More » -
5G Security

Geopolitics of 5G and 5G-Connected Massive & Critical IoT
Emerging Technology and Geopolitics of 5G There are several reasons emerging technology is a highly competitive industry, notwithstanding the race for intellectual property that can be licensed by burgeoning markets for revenue. A first-mover advantage is often a way to…
Read More » -
5G Security

5G Policy and Regulatory Checklist
Ultra high speed, high quality 5G networks are expected to provide the connectivity required for massive IoT adoption, remote robotic surgery as well as instant movie downloads and 3D mobile gaming. The technology boasts incredible reliability and low latency and…
Read More » -
5G Security

5G Network Slicing Technology: A Primer
Hyped as the technology that will transform the world, 5G is moving past the buzzword stage with first implementations coming to life in 2019. Nations are racing to 5G with such fervor that it now became one of the hottest…
Read More » -
5G Security

5G Security & Privacy Challenges
Don’t let the “5G” in the title confuse you. This post is not only about the telcos’ core networks, but about the 5G security and privacy issues in our (very) near, and very different future that 5G will enable. In…
Read More » -
Cyber-Kinetic Security

Cyber-Kinetic Security and Privacy Threats in Smart Cities
More than half of the world’s population lives in cities. The UN estimates that by 2050 that proportion will be 68% – more than 6 billion people living in high-density conditions. This raises significant challenges. What is the best way…
Read More » -
Society 5.0

How 5G Will Transform Economy and Society
Since the dawn of the 21st Century, the ways in which people and organizations that use the Internet experience, perceive and act in the world is radically changing. We interact with physical objects and systems well beyond our sight and…
Read More » -
AI Security

AI-Exacerbated Disinformation and Cyber Threats to Democracy
Recent events have confirmed that the cyber realm can be used to disrupt democracies as surely as it can destabilize dictatorships. Weaponization of information and malicious dissemination through social media pushes citizens into polarized echo chambers and pull at the…
Read More » -
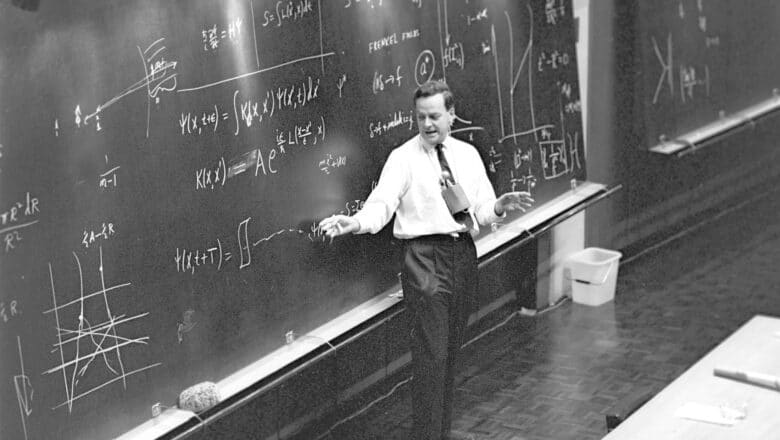
Quantum Computing

Feynman and the Early Promise of Quantum Computing
In the early 1980s, the legendary physicist Richard Feynman imagined a new kind of computer - one that operates on the weird rules of quantum mechanics rather than classical physics. Frustrated by how clumsy ordinary computers were at simulating the…
Read More »