-
Research
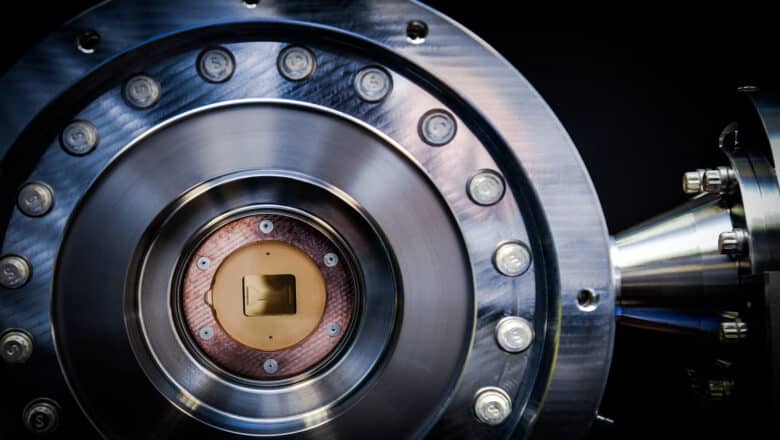
Hole-Spin Qubits Demonstrated in Silicon FinFETs
In a significant quantum computing breakthrough, researchers from the University of Basel and IBM Research–Zurich have achieved a controlled interaction between two quantum bits inside a standard silicon transistor. The team’s new paper “Anisotropic exchange interaction of two hole-spin qubits”…
Read More » -
Quantum Commercialization

From Lab Breakthroughs to Quantum Boom: Why the Time to Commercialize is Now
The current stage of development in quantum isn’t about figuring out if the technology works – it’s about making it work reliably, at scale, and for a purpose. That requires an all-hands-on-deck approach. Universities and research institutes must continue to…
Read More » -
Post-Quantum, PQC, Quantum Security

Cryptographic Bill of Materials (CBOM) Deep-Dive
Cryptographic Bill of Materials (CBOM) represent the next evolution in software transparency and security risk management. As we have explored, a CBOM provides deep visibility into an application’s cryptographic underpinnings – an area that has often been opaque to security…
Read More » -
Research
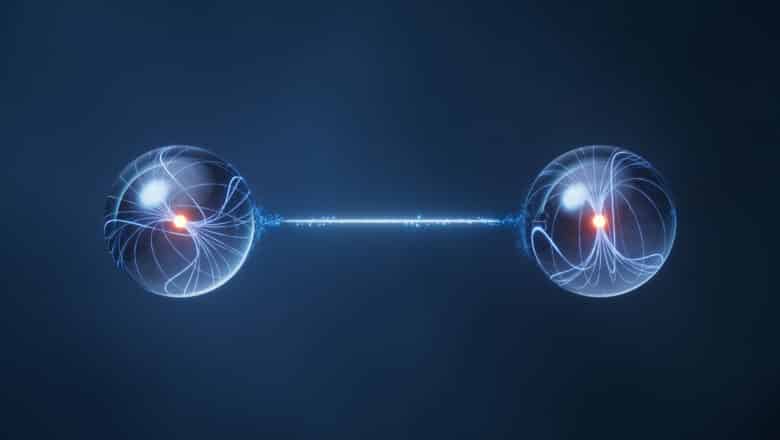
Major Leap for Quantum Internet: First Critical Connection
London, April 2024 – In a groundbreaking advancement for the future of global communication, researchers from Imperial College London and their partners at the Universities of Southampton, Stuttgart, and Würzburg have established a core link necessary for the quantum internet,…
Read More » -
Post-Quantum, PQC, Quantum Security

Capability E.1: Engineering Scale & Manufacturability
Building a cryptography-breaking quantum computer (often dubbed Q-Day) will demand far more than just better algorithms or a few more qubits. It requires a massive scale-up in engineering - reaching hundreds of thousands or even millions of physical qubits -…
Read More » -
Post-Quantum, PQC, Quantum Security

Capability B.4: Qubit Connectivity & Routing Efficiency
Qubit connectivity refers to which qubits can interact directly (perform two-qubit gates) with each other. This is often visualized as a connectivity graph: each node is a qubit, and an edge between two nodes means those qubits can be coupled…
Read More » -
Post-Quantum, PQC, Quantum Security

How to Perform a Comprehensive Quantum Readiness Cryptographic Inventory
A cryptographic inventory is essentially a complete map of all cryptography used in an organization’s systems – and it is vital for understanding quantum-vulnerable assets and planning remediation. In theory it sounds straightforward: “list all your cryptography.” In practice, however,…
Read More » -
Quantum Sovereignty

Quantum Sovereignty Primer: Inside the New Tech Arms Race
The term quantum sovereignty has entered the geopolitical lexicon, capturing the idea that nations must control their own quantum technologies – from ultra-powerful quantum computers to unhackable quantum communications – or risk dependence on others. “The rapid advancement of quantum…
Read More » -
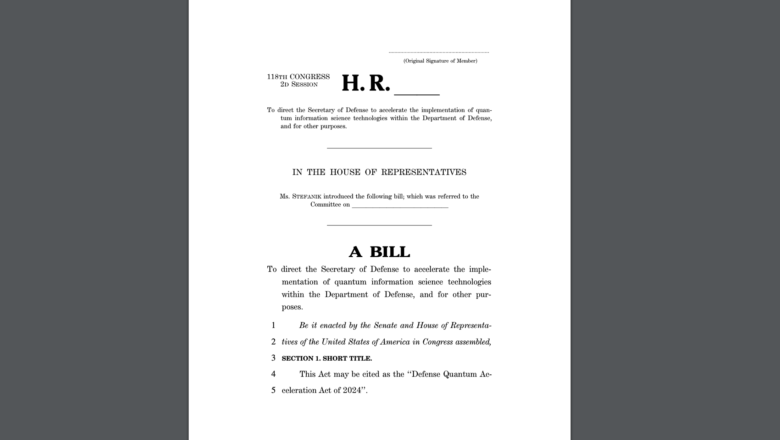
Policy & Sovereignty

New Legislation to Boost U.S. DoD Quantum Capabilities
A recent bill introduced by United States’ Republican lawmakers aims to accelerate the Defense Department’s development and integration of quantum technologies, enhancing capabilities in areas like navigation, sensing, and artificial intelligence. The Defense Quantum Acceleration Act, championed by Rep. Elise…
Read More » -
Policy & Sovereignty

EU Publishes a Recommendation on Post-Quantum Cryptography
In another sign of Q-Day concerns and preparations heating up recently, the European Commission has published a key recommendation urging EU member states to adopt a harmonized approach to post-quantum cryptography. This guidance, “Recommendation on a Coordinated Implementation Roadmap for…
Read More » -
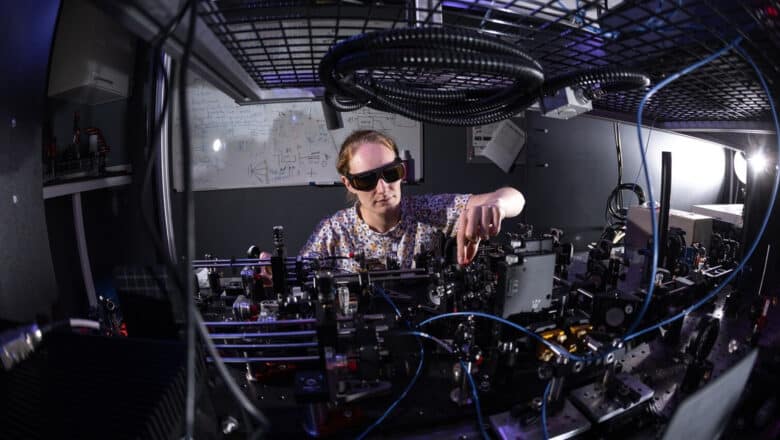
Quantum Computing

The Quantum Computer That Breaks Your Encryption Won’t Be a Single Chip
There's a question that has quietly bothered me for years, one the quantum computing industry has mostly avoided asking out loud: why are we trying to build a quantum computer the way we stopped building classical computers fifty years ago?…
Read More » -
AI Security

The Dual Risks of AI Autonomous Robots: Uncontrollable AI Meets Cyber-Kinetic Risks
The automotive industry has revolutionized manufacturing twice. The first time was in 1913 when Henry Ford introduced a moving assembly line at his Highland Park plant in Michigan. The innovation changed the production process forever, dramatically increasing efficiency, reducing the…
Read More » -
Leadership

The Board’s Evolving Cybersecurity Mandate: From Oversight to Accountability
Cybersecurity has swiftly moved from an IT issue to a core boardroom concern. Regulators around the world are increasingly holding boards of directors directly responsible for overseeing cyber risk - and even personally accountable when things go wrong. As someone…
Read More » -
Industry

Microsoft Announces Record Breaking Logical Qubit Results
Microsoft and Quantinuum have announced a major quantum computing breakthrough: the creation of the most reliable logical qubits on record, with error rates 800 times lower than those of physical qubits. In an achievement unveiled on April 3, 2024, the…
Read More » -
Post-Quantum, PQC, Quantum Security

Infrastructure Challenges of “Dropping In” Post-Quantum Cryptography (PQC)
Post-quantum cryptography (PQC) is moving from theory to practice. NIST has now standardized several PQC algorithms - such as CRYSTALS-Kyber for key exchange (now known as ML-KEM) and CRYSTALS-Dilithium and SPHINCS+ for digital signatures - and major tech companies like…
Read More »