-
5G Security

IIoT and Trust and Convenience: A Potentially Deadly Combination
When microwave ovens first arrived on the market in 1967 they were met with public skepticism. Perhaps it was because, not long before, the same technology now promising to safely cook consumers’ evening meals was the backbone of a military…
Read More » -
Post-Quantum, PQC, Quantum Security

Challenges of Upgrading to Post-Quantum Cryptography (PQC)
The shift to post-quantum cryptography is not a distant problem but an imminent challenge that requires immediate attention. The quantum threat affects all forms of computing—whether it’s enterprise IT, IoT devices, or personal electronics. Transitioning to quantum-resistant algorithms is a…
Read More » -
5G Security

5G Network: A Quantum Leap in Connectivity – and Cyber Threats
The timeline of human history is marked by inflection points of major technological advancement. The plow, the printing press, the telegraph, the steam engine, electricity, the telephone, the internet: each of these breakthroughs precipitated tectonic shifts in how people lived…
Read More » -
Society 5.0

5G Innovation Zones in Canada for Launching AI and 5G in Tandem
In my previous post I argued that if Canada wants to succeed with its AI-focused innovation agenda, it should also be at the forefront of 5G innovation and development. Canada could get ahead in the global 5G race not by…
Read More » -
5G Security

5G Health Risks – Health, Wealth and Tin Foil Hats
The rollout of 5G is one of the most anticipated events in humanity’s technological history. But what about the 5G health concerns? It’s the night before Halloween in 1938 and, as the tale goes, radio audiences tuning into Orson Welles’…
Read More » -
5G Security

5G and AI – Getting Smart About 5G and AI in Canada
Canada has been investing in machine learning and artificial intelligence (AI) for longer than most of the industrialized world. Dr. Geoff Hinton of Google helped ignite the field of graphics processing unit (GPU) deep learning at the University of Toronto.…
Read More » -
Quantum Computing

Schrödinger’s Wave Equation
Schrödinger’s equation is essentially the master instruction set for quantum systems – the quantum-world analogue of Newton’s famous F=ma in classical physics. In short, Schrödinger’s equation is to quantum mechanics what Newton’s second law is to classical mechanics: a fundamental…
Read More » -
5G Security

NFC Security 101 (Non-5G IoT Connectivity Options)
NFC is a short range two-way wireless communication technology that enables simple and secure communication between electronic devices embedded with NFC microchip. NFC technology operates in 13.56 megahertz and supports 106, 212, or 424 Kbps throughput. There are three available…
Read More » -
5G Security

RFID Security 101 (Non-5G IoT Connectivity Options)
Radio-Frequency Identification (RFID) is a technology commonly used for identification, status administration and management of different objects. It is important for people identification, as it is commonly deployed in the latest biometric passports. It operates in several frequency bands like Low…
Read More » -
AI Security

AI and 5G: AI at the 5G Core – A Double-Edged Sword
If you’ve ever been to an expensive restaurant and ordered a familiar dish like, say, lasagna, but received a plate with five different elements arranged in a way that does not at all resemble what you know as lasagna, then…
Read More » -
5G Security

Wi-Fi Security 101 (Non-5G IoT Connectivity Options)
The Wi-Fi represents wireless technology that includes the IEEE 802.11 family of standards (IEEE 802.11a, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, IEEE 802.11ac, etc.). Within 50m range, it operates in 2.4 GHz and 5GHz frequency bands,. This technology was developed…
Read More » -
5G Security

Bluetooth Security 101 (Non-5G IoT Connectivity Options)
Bluetooth is short-range wireless communications technology based on the IEEE 802.15.1 protocol. It works in a crowded license free 2.4 GHz frequency band and shares this resource with many other technologies. Bluetooth is the optimal solution for establishing small wireless…
Read More » -
5G Security

Zigbee Security 101 (Non-5G IoT Connectivity Options)
Zigbee technology introduction Zigbee is wireless PAN (Personal Area Network) technology developed to support automation, machine-to-machine communication, remote control and monitoring of IoT devices. It evolved from IEEE 802.15.4 wireless standard and supported by the ZigBee Alliance. IEEE 802.15.4 standard…
Read More » -
5G Security

LoRaWAN Security 101 (Non-5G IoT Connectivity Options)
I get accused of focusing too much on 5G as the only future IoT connectivity option. I do write a lot about how 5G will revolutionize our society, become the most critical of critical infrastructures and about security threats with…
Read More » -
Post-Quantum, PQC, Quantum Security

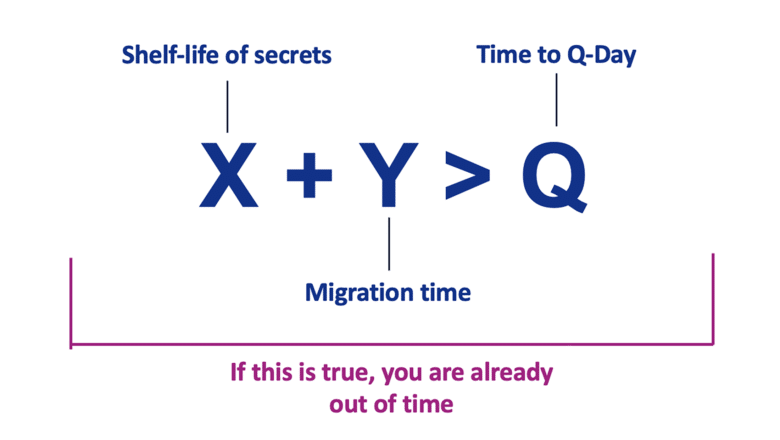
Mosca’s Theorem and Post‑Quantum Readiness: A Guide for CISOs
Mosca’s Theorem is a risk framework formulated to help organizations gauge how urgent their post-quantum preparations should be. It is often summarized by the inequality X + Y > Q, where: X = the length of time your data must…
Read More »