-
Crypto Security

How KuCoin Survived a Massive Hack of $285M Worth of Crypto Assets
When attacked, some crypto projects and exchanges buckle and fold under pressure; KuCoin set the standard in 2020 for how to react to crypto hacks, even on the largest scale. KuCoin is a Singapore-based crypto exchange that consistently ranks among…
Read More » -
5G Security

The Open RAN Lexicon You Need
The telecoms and digital technologies sectors are notoriously jargonised. Eavesdrop on any conversation at an industry conference (remember those?) and you’d be treated to a parade of acronyms, initialisms and technical terms that would sound like ancient Greek to an…
Read More » -
Quantum Computing
Quantum Supremacy vs. Quantum Advantage
In the ever-accelerating world of quantum computing, two terms have emerged as the darlings of headlines and conference keynotes: quantum supremacy and quantum advantage. If you've followed the news, you might think they're interchangeable buzzwords celebrating the dawn of a…
Read More » -
Post-Quantum, PQC, Quantum Security
CRQC Readiness Index Proposal
This proposal outlines a composite, vendor‑neutral “CRQC Readiness” indicator. It intentionally avoids one‑number vanity metrics (like only counting qubits) and instead triangulates from three ingredients that actually matter for breaking today’s crypto: usable (logical) qubits, error‑tolerant algorithm depth, and sustained…
Read More » -
Post-Quantum, PQC, Quantum Security

Understanding FIPS 140: A Cornerstone of Cryptographic Security
FIPS 140 (Federal Information Processing Standard 140) is a U.S. government computer security standard that specifies security requirements for cryptographic modules - the hardware or software components that perform encryption and other cryptographic functions. In simpler terms, FIPS 140 sets…
Read More » -
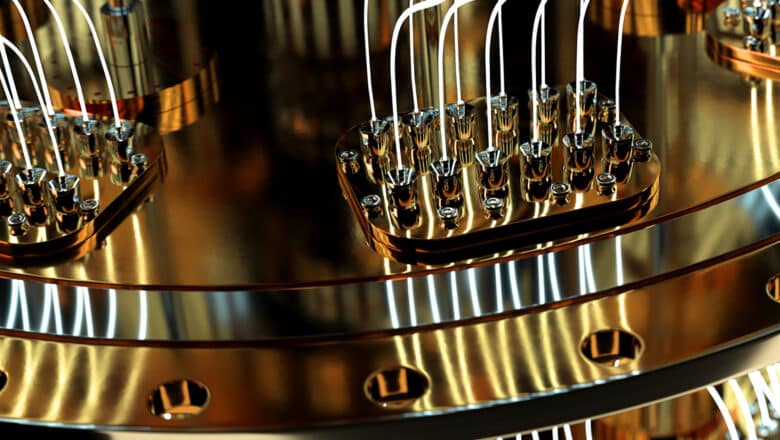
Industry

China’s Jiuzhang Achieves Photonic Quantum Advantage
A team of Chinese scientists has announced a breakthrough in quantum computing with the development of Jiuzhang, a photonic quantum processor that achieved a major computational milestone. In experiments reported on December 3, 2020, Jiuzhang completed in 200 seconds a…
Read More » -
5G Security

Open RAN May Be the Future of 5G, but Can We Keep It Secure?
It’s been a year of contradictions for the telecommunications industry. Like most sectors, it has been heavily impacted by the consequences of the Covid-19 pandemic, with a slowdown in global 5G roll-outs being a notable result. Geopolitical conflicts have continued…
Read More » -
5G Security

5G in Manufacturing – 5G and Time Sensitive Networking (TSN) for Industrial Automation
In the recent report by IHS Markit – “The 5G Economy – How 5G will contribute to the global economy” – researchers claimed that manufacturing will garner almost $4.7 trillion in sales enablement by 2035. Or 36% of the $13.2…
Read More » -
Industry

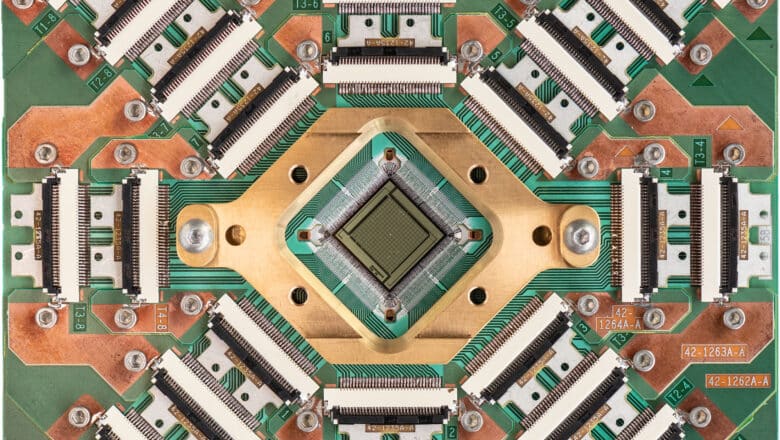
D-Wave’s 5,000+ Qubit Quantum Computer “Advantage”
Vancouver-area company D-Wave Systems - the world’s first commercial quantum computing firm - launched its Advantage quantum annealer, boasting over 5,000 qubits and a radically expanded 15-way qubit connectivity. This machine marked a leap from its previous 2,000-qubit system and…
Read More » -
5G Security

Cybersecurity and Safety in the 5G-Enabled Smart-Everything World
Neil Harbisson calls himself a cyborg. Without the antenna implanted in his skull, he would not be able to see colour of any kind. Born with achromatopsia, a condition of total colourblindness that affects 1 in every 30 000 people,…
Read More » -
5G Security

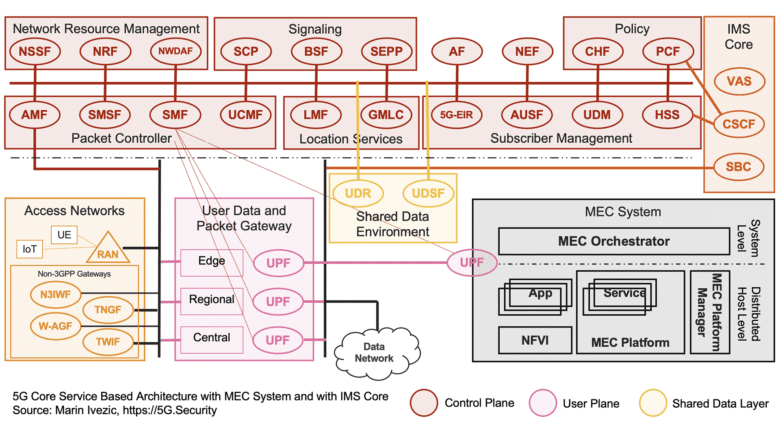
Introduction to 5G Core Service-Based Architecture (SBA) Components
The interest in 5G and mIoT is exploding. It’s exciting to see so many IT and cybersecurity professionals in my network trying to learn more about 5G and related technologies. In addition to my usual articles about the societal impacts…
Read More » -
AI Security

Targeted Disinformation
Targeted disinformation poses a significant threat to societal trust, democratic processes, and individual well-being. The use of AI in these disinformation campaigns enhances their precision, persuasiveness, and impact, making them more dangerous than ever before. By understanding the mechanisms of…
Read More » -
5G Security

Smart Home / Smart Building Connectivity Options and Their Cybersecurity
In a recent session on smart building cybersecurity, a student cheekily asked me “How did we ever connect anything before 5G?” At that moment I realized I might have been overdoing my 5G cheerleading recently. To atone, here are the…
Read More » -
5G Security

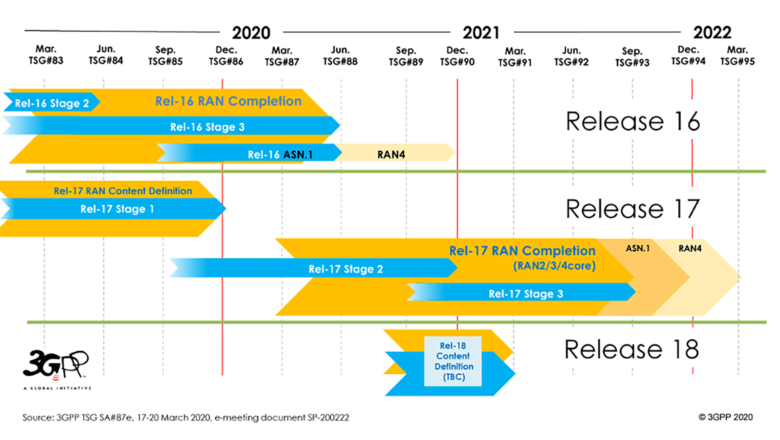
Introduction to 3GPP and 3GPP 5G Releases 15, 16 and 17
In a major milestone for 5G, 3GPP finalized the Release 16 in July – its second set of specifications for 5G New Radio (NR) technology. As a second article in my series of 5G 101 articles, this is a good…
Read More » -
Quantum Computing

Early History of Quantum Computing
Since the early 2000s, the field of quantum computing has seen significant advancements, both in technological development and in commercialization efforts. The experimental demonstration of Shor's algorithm in 2001 proved to be one of the key catalyzing events, spurring increased…
Read More »