-
Post-Quantum, PQC, Quantum Security

Next-Generation QKD Protocols: A Cybersecurity Perspective
Traditional QKD implementations have demonstrated provably secure key exchange, but they come with practical limitations. To address these limitations, researchers have developed next-generation QKD protocols. These advanced protocols improve security by reducing trust assumptions and mitigating device vulnerabilities, and they…
Read More » -
AI Security
Batch Exploration Attacks on Streamed Data Models
Batch exploration attacks are a class of cyber attacks where adversaries systematically query or probe streamed machine learning models to expose vulnerabilities, glean sensitive information, or decipher the underlying structure and parameters of the models. The motivation behind such attacks…
Read More » -
Industry
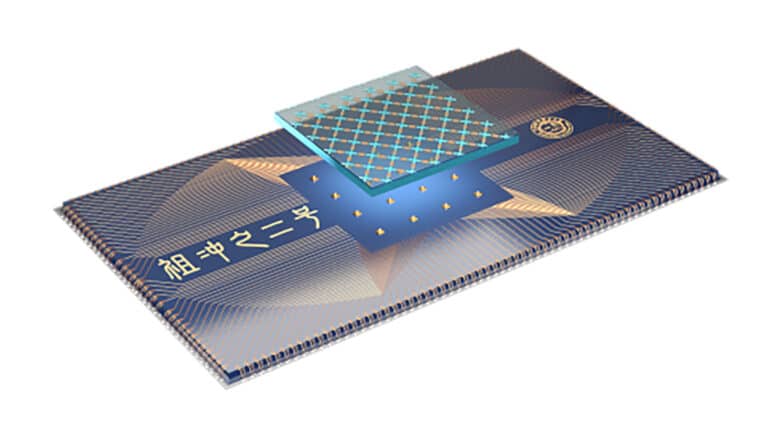
Zuchongzhi 1.0: China’s New Superconducting Processor
In May 2021, scientists at the Chinese Academy of Sciences (CAS) unveiled Zuchongzhi 1.0, a 62-qubit programmable superconducting quantum computer that set a new benchmark in the quantum computing race. Named after a 5th-century Chinese mathematician, Zuchongzhi 1.0 contains the…
Read More » -
Society 5.0

Securing Society 5.0
A term first coined by the Japanese government, “Society 5.0” describes “A human-centered society that balances economic advancement with the resolution of social problems by a system that highly integrates cyberspace and physical space.” The fifth evolution of the society,…
Read More » -
Policy & Sovereignty

ENISA Publishes “Post-Quantum Cryptography” Report
The European Union Agency for Cybersecurity (ENISA) has recently published a report titled “Post-Quantum Cryptography: Current State and Quantum Mitigation.” This study offers a detailed overview of the current progress in the standardization process of Post-Quantum Cryptography (PQC), crucial for…
Read More » -
Industry

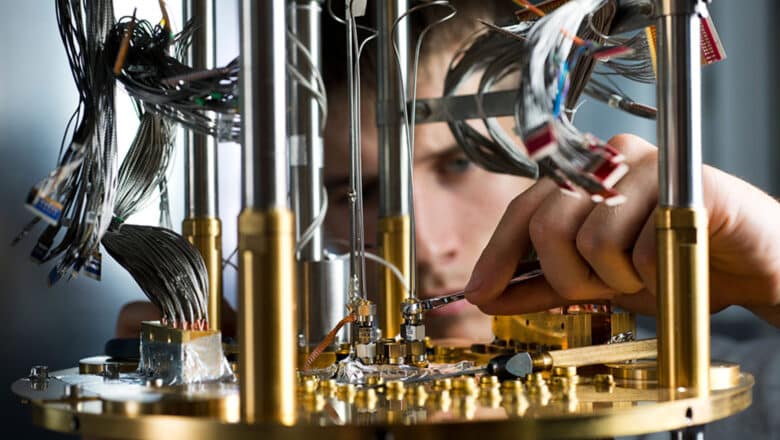
ETH Zurich and PSI Launch Joint Quantum Computing Hub
May 2021 - ETH Zurich and the Paul Scherrer Institute (PSI) opened a new joint Quantum Computing Hub dedicated to developing next-generation quantum computers. Backed by CHF 32 million from ETH, the center in canton Aargau brings together about 30…
Read More » -
Post-Quantum, PQC, Quantum Security

Evaluating Tokenization in the Context of Quantum Readiness
As the quantum era approaches, organizations face the daunting task of protecting their sensitive data from the looming threat of quantum computers. These powerful machines have the potential to render traditional cryptographic methods obsolete, making it imperative to explore innovative…
Read More » -
Research

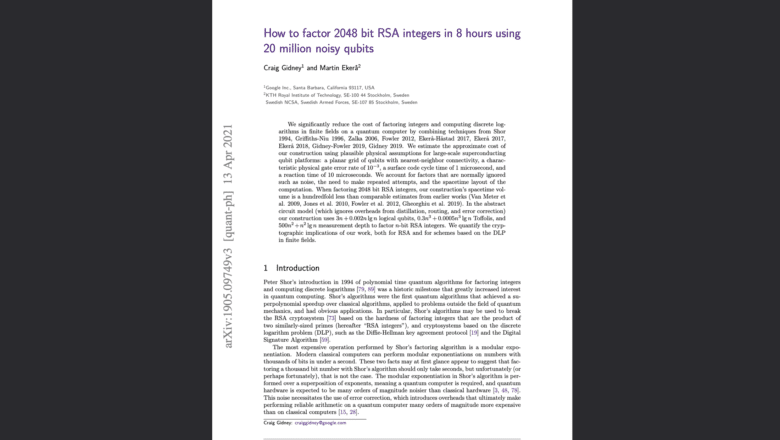
Breaking RSA-2048 With 20M Noisy Qubit
An interesting paper was published on arXiv, the preprint server. Titled “How to factor 2048 bit RSA integers in 8 hours using 20 million noisy qubits,” the paper by Craig Gidney and Martin Ekerå combines previous techniques from Shor (1994),…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Computing – Looming Threat to Telecom Security
Since the early 2000s, the field of quantum computing has seen significant advancements, both in technological development and in commercialization efforts. The experimental demonstration of Shor's algorithm in 2001 proved to be one of the key catalyzing events, spurring increased…
Read More » -
Post-Quantum, PQC, Quantum Security

Adiabatic Quantum Computing (AQC) and Impact on Cyber
Adiabatic Quantum Computing (AQC), and its variant Quantum Annealing, are another model for quantum computation. It's a specialized subset of quantum computing focused on solving optimization problems by finding the minimum (or maximum) of a given function over a set…
Read More » -
Quantum Computing

Routing Quantum Information: SWAP, iSWAP, and Moving Qubit States
Quantum computers face a unique challenge in moving quantum information between qubits. Unlike classical bits that can be shuttled freely along wires, qubits cannot be arbitrarily copied or moved due to the no-cloning theorem. To route a qubit’s state from…
Read More » -
Quantum Computing

Surface Code Quantum Error Correction
Quantum error correction (QEC) is indispensable for building large-scale fault-tolerant quantum computers. Even today’s best qubits suffer error rates that would quickly corrupt any long calculation if left uncorrected. The principle of QEC is to encode a single logical qubit…
Read More » -
5G Security

A Comparison of 5G Core Network Architectures
The 5G Core network is a Service Based Architecture. It evolves the traditional appliance based 4G Core Network to support services. It offers more agility and flexibility. The major building blocks of this architecture include Service-Based Interface: The Service Based…
Read More » -
AI Security

How Model Inversion Attacks Compromise AI Systems
A model inversion attack aims to reverse-engineer a target machine learning model to infer sensitive information about its training data. Specifically, these attacks are designed to exploit the model's internal representations and decision boundaries to reverse-engineer and subsequently reveal sensitive…
Read More » -
AI Security

When AI Trusts False Data: Exploring Data Spoofing’s Impact on Security
Data spoofing is the intentional manipulation, fabrication, or misrepresentation of data with the aim of deceiving systems into making incorrect decisions or assessments. While it is often associated with IP address spoofing in network security, the concept extends into various…
Read More »