-
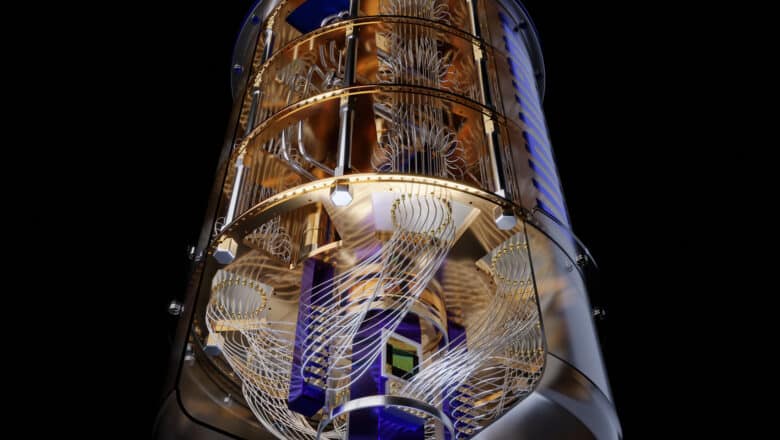
Quantum Computing
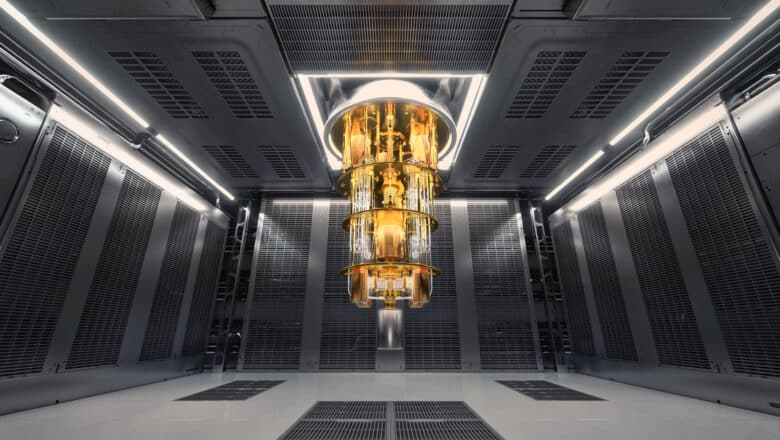
Fidelity in Quantum Computing
Fidelity in quantum computing measures the accuracy of quantum operations, including how effectively a quantum computer can perform calculations without errors. In quantum systems, noise and decoherence can degrade the coherence of quantum states, leading to errors and reduced computational…
Read More » -
Quantum Computing

Quantum Technology Use Cases in Supply Chain & Logistics
Quantum computing is on the cusp of reshaping the supply chain and logistics sector. Its ability to process information in fundamentally new ways holds the promise of solving the longstanding puzzles of logistics – from finding optimal delivery routes and…
Read More » -
Quantum Security & PQC
BIS Project Leap: Quantum‑Proofing Payments With Hybrid PQC Is Feasible – Now Comes the Hard Part
The Bank for International Settlements (BIS) has released a report under Project Leap demonstrating - via a realistic central‑bank payments connectivity experiment - that post‑quantum cryptography (PQC) can be deployed today in a hybrid mode without breaking core operational expectations for secure inter‑site connectivity.…
Read More » -
Post-Quantum, PQC, Quantum Security

Harvest Now, Decrypt Later (HNDL) Risk
"Harvest Now, Decrypt Later" (HNDL), also known as "Store Now, Decrypt Later" (SNDL), is a concerning risk where adversaries collect encrypted data with the intent to decrypt it once quantum computing becomes capable of breaking current encryption methods. This is…
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Cryptography PQC Challenges
The transition to post-quantum cryptography is a complex, multi-faceted process that requires careful planning, significant investment, and a proactive, adaptable approach. By addressing these challenges head-on and preparing for the dynamic cryptographic landscape of the future, organizations can achieve crypto-agility…
Read More » -
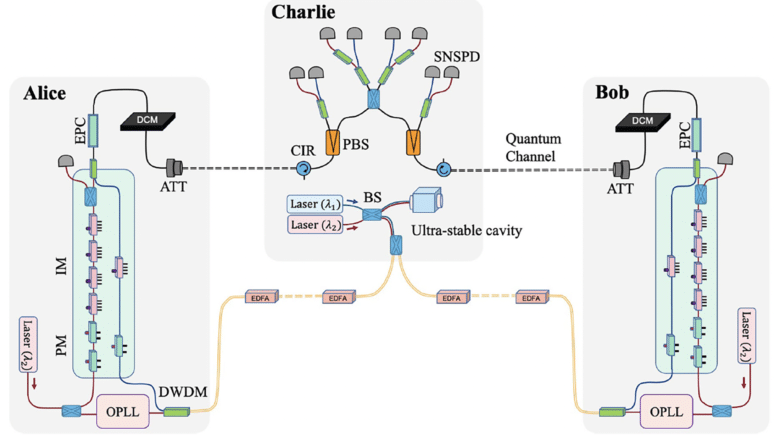
Industry

New World Record: Twin-Field QKD Achieved Over 1,000 km Fiber Link
Chinese scientists have shattered the distance record for quantum key distribution (QKD) by successfully exchanging secure cryptographic keys across 1,002 kilometers of optical fiber – more than double the previous record. In a landmark experiment published in Physical Review Letters, a…
Read More » -
AI Security

A (Very) Brief History of AI
As early as the mid-19th century, Charles Babbage and Ada Lovelace created the Analytical Engine, a mechanical general-purpose computer. Lovelace is often credited with the idea of a machine that could manipulate symbols in accordance with rules and that it…
Read More » -
AI Security

Understanding and Addressing Biases in Machine Learning
While ML offers extensive benefits, it also presents significant challenges, among them, one of the most prominent ones is biases in ML models. Bias in ML refers to systematic errors or influences in a model's predictions that lead to unequal…
Read More » -
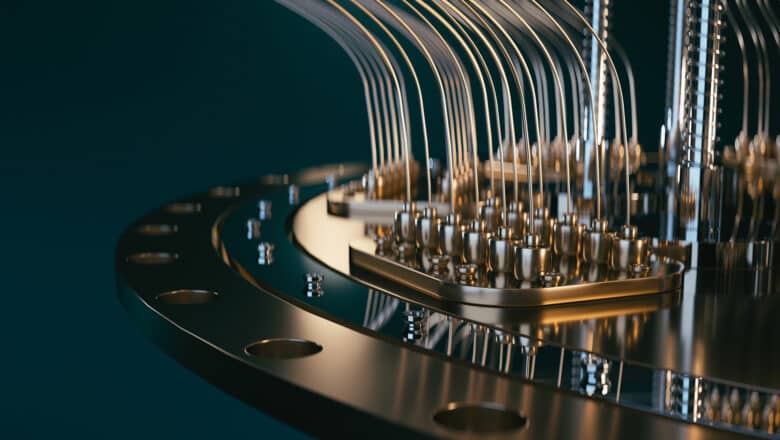
Quantum Computing

Quantum Errors and Quantum Error Correction (QEC) Methods
Quantum error correction (QEC) is therefore critical for enabling large-scale or fault-tolerant quantum computing. Fault tolerance means a quantum computer can continue to operate correctly even when individual operations or qubits error out. Unlike classical error correction – which can…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Era Demands Changes to ALL Enterprise Systems
In my work with various clients, I frequently encounter a significant misunderstanding about the scope of preparations required to become quantum ready. Many assume that the transition to a post-quantum world will be straightforward, involving only minor patches to a…
Read More » -
Post-Quantum, PQC, Quantum Security

Bills of Materials for Quantum Readiness: SBOM, CBOM, and Beyond
Quantum computing threat is forcing organizations to inventory their digital assets like never before. With powerful quantum attacks on the horizon, businesses must identify what they have - software, cryptography, sensitive data, hardware - before they can secure it. Security…
Read More » -
Quantum Security & PQC

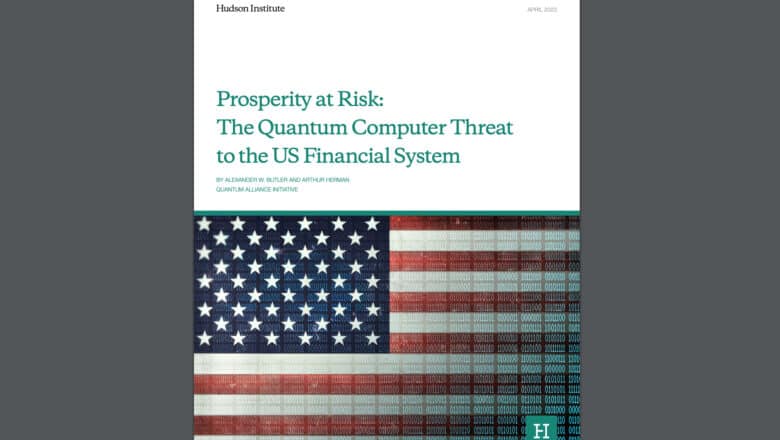
Report “The Quantum Threat to the US Financial System”
A new, interesting, report was just published by the Hudson institute – “Prosperity at Risk: The Quantum Computer Threat to the US Financial System,” authored by Alexander W. Butler and Arthur Herman of the Quantum Alliance Initiative at the Hudson…
Read More » -
Post-Quantum, PQC, Quantum Security

Inside NIST’s PQC: Kyber, Dilithium, and SPHINCS+
In 2022, after a multi-year evaluation, NIST selected CRYSTALS-Kyber, CRYSTALS-Dilithium, and SPHINCS+ as the first algorithms for standardization in public-key encryption (key encapsulation) and digital signatures. Kyber is an encryption/key-establishment scheme (a Key Encapsulation Mechanism, KEM) based on lattice problems,…
Read More » -
Quantum Networks

Quantum Networks 101: An Intro for Cyber Professionals
Quantum networks are on the cusp of transitioning from theory to practice, following a trajectory not unlike the early development of the classical internet. They hold the promise of fundamentally secure communications and new quantum information capabilities. While challenges remain,…
Read More » -
AI Security

Adversarial Attacks: The Hidden Risk in AI Security
Adversarial attacks specifically target the vulnerabilities in AI and ML systems. At a high level, these attacks involve inputting carefully crafted data into an AI system to trick it into making an incorrect decision or classification. For instance, an adversarial…
Read More »