-
Quantum Computing Modalities

Quantum Computing Modalities: Gate-Based / Universal QC
Quantum computing in the gate-based or circuit model is the most widely pursued paradigm for realizing a universal quantum computer. In this model, computations are carried out by applying sequences of quantum logic gates to qubits (quantum bits), analogous to…
Read More » -
AI Security
Model Fragmentation and What it Means for Security
Model fragmentation is the phenomenon where a single machine-learning model is not used uniformly across all instances, platforms, or applications. Instead, different versions, configurations, or subsets of the model are deployed based on specific needs, constraints, or local optimizations. This…
Read More » -
Quantum Computing Modalities
Quantum Computing Modalities: Quantum Annealing (QA) & Adiabatic QC (AQC)
Quantum annealing (QA) and adiabatic quantum computing (AQC) are closely related paradigms that use gradual quantum evolution to solve problems. In both approaches, a problem is encoded into a landscape of energy states (a quantum Hamiltonian), and the system is…
Read More » -
Quantum Computing Modalities
Quantum Computing Modalities: Quantum Cellular Automata (QCA) in Living Cells
Trapped-ion quantum computing uses individual ions (charged atoms) as qubits. Each ion’s internal quantum state (usually two hyperfine levels of the atom’s electron configuration) serves as |0⟩ and |1⟩. Ions are held in place (suspended in free space) using electromagnetic…
Read More » -
AI Security

Outsmarting AI with Model Evasion
Model Evasion in the context of machine learning for cybersecurity refers to the tactical manipulation of input data, algorithmic processes, or outputs to mislead or subvert the intended operations of a machine learning model. In mathematical terms, evasion can be…
Read More » -
Leadership

Canada’s Quiet Blockchain Revolution: A Tech Legacy Forged in the North
Canada might not be the first country that comes to mind when you think of blockchain and cryptocurrency. Yet, from community meetups in Toronto pubs to world-leading enterprise deployments, Canadians have played a pivotal role in shaping blockchain’s global story.…
Read More » -
Quantum Sensing

Ethical and Privacy Implications of Quantum Sensing
Quantum sensing sits at a crossroads of promise and peril. On one hand, it embodies the awe-inspiring potential of quantum technology – offering us new eyes and ears to perceive the world in richer detail than ever before. It could…
Read More » -
Research

New Hybrid Quantum Monte Carlo Algorithm
Researchers Xiaosi Xu and Ying Li have developed a “quantum-assisted” Monte Carlo method that uses a small quantum processor to boost the accuracy of classical simulations. The breakthrough, published in Quantum in 2023, addresses the notorious sign problem in quantum…
Read More » -
Policy & Sovereignty

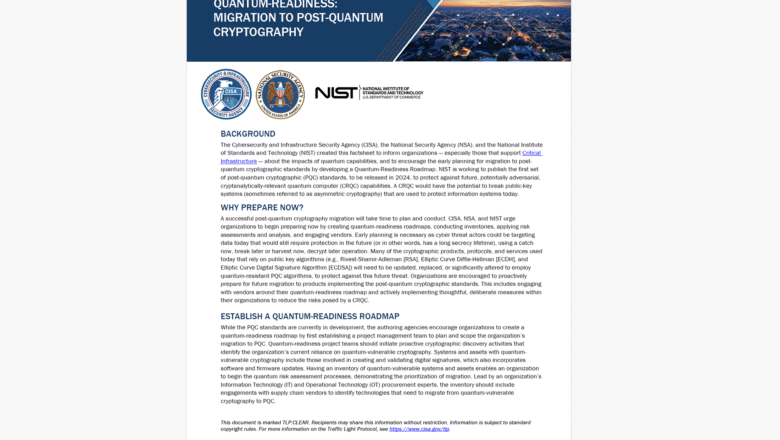
CISA’s “Quantum-Readiness” Fact Sheet: A Call to Prepare for Post-Quantum Cryptography
The Cybersecurity and Infrastructure Security Agency (CISA) together with the NSA and NIST released a joint cybersecurity factsheet titled “Quantum-Readiness: Migration to Post-Quantum Cryptography.” This document was created to inform organizations - “especially those that support Critical Infrastructure” - about…
Read More » -
Q-Day

Q-Day Predictions: Anticipating the Arrival of CRQC
While CRQCs capable of breaking current public key encryption algorithms have not yet materialized, technological advancements are pushing us towards what is ominously dubbed 'Q-Day'—the day a CRQC becomes operational. Many experts believe that Q-Day, or Y2Q as it's sometimes…
Read More » -
AI Security

AI and Canada: Pioneering Innovation, Searching for Homegrown Success
It’s easy to forget, amid the hype around Silicon Valley’s AI giants, that many of the foundational breakthroughs of modern AI were born in Canada. In fact, two of the three “godfathers of AI” - Yoshua Bengio and Geoffrey Hinton…
Read More » -
AI Security

Securing Machine Learning Workflows through Homomorphic Encryption
Homomorphic Encryption has transitioned from being a mathematical curiosity to a linchpin in fortifying machine learning workflows against data vulnerabilities. Its complex nature notwithstanding, the unparalleled privacy and security benefits it offers are compelling enough to warrant its growing ubiquity.…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Readiness for Mission-Critical Communications (MCC)
Mission-critical communications (MCC) networks are the specialized communication systems used by “blue light” emergency and disaster response services (police, fire, EMS), military units, utilities, and other critical operators to relay vital information when lives or infrastructure are at stake. These…
Read More » -
AI Security

Understanding Data Poisoning: How It Compromises Machine Learning Models
Data poisoning is a targeted form of attack wherein an adversary deliberately manipulates the training data to compromise the efficacy of machine learning models. The training phase of a machine learning model is particularly vulnerable to this type of attack…
Read More » -
AI Security

Semantic Adversarial Attacks: When Meaning Gets Twisted
Semantic adversarial attacks represent a specialized form of adversarial manipulation where the attacker focuses not on random or arbitrary alterations to the data but specifically on twisting the semantic meaning or context behind it. Unlike traditional adversarial attacks that often…
Read More »