Meta Publishes Its PQC Migration Playbook. And It’s the Most Detailed Hyperscaler Account Yet

April 18, 2026 – Meta has published what may be the most comprehensive post-quantum cryptography migration playbook released by any hyperscaler to date. The detailed framework, shared on the company’s engineering blog, reveals that Meta has already deployed quantum-resistant encryption across significant portions of its internal infrastructure while introducing a structured “PQC Migration Levels” model that other organizations can adopt.
The playbook arrives as major technology companies race to implement quantum-resistant cryptography ahead of industry deadlines. Google and Cloudflare have both committed to completing their PQC migrations by 2029, while Meta’s publication provides the first detailed look at how a company managing billions of users approaches the transition.
The framework introduces five distinct migration levels, ranging from “PQ-Unaware” to “PQ-Enabled,” with Meta reporting it has already reached the highest level for portions of its internal traffic. The company emphasizes that organizations can achieve meaningful security improvements at intermediate levels while working toward full quantum resistance.
Meta’s prioritization methodology divides applications into three risk categories based on their vulnerability to quantum attacks. High-priority applications include those susceptible to “store now, decrypt later” attacks, where adversaries collect encrypted data today for future decryption. Medium-priority applications face online quantum attacks that require an actual quantum computer to execute. Low-priority applications remain relatively secure against quantum threats due to their reliance on symmetric cryptography.
The playbook identifies three critical external dependencies that organizations must address: community-vetted standards from bodies like NIST, hardware support from HSM and CPU vendors, and production-ready implementations from the cryptography engineering community. Meta notes its active involvement in developing NIST PQC standards, including co-authorship of the HQC algorithm recently selected for standardization.
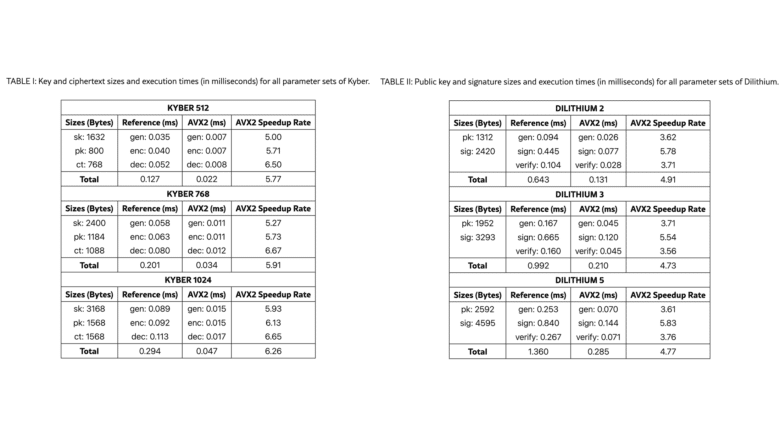
Rafael Misoczki, Isaac Elbaz, and Forrest Mertens, the Meta engineers who authored the playbook, recommend organizations adopt ML-KEM (formerly CRYSTALS-Kyber) for key exchange and ML-DSA (formerly CRYSTALS-Dilithium) for digital signatures. They advocate for a hybrid approach that layers quantum-resistant algorithms on top of classical cryptography rather than wholesale replacement.
The framework also addresses implementation guardrails, including updated internal cryptography guidelines, warnings against creating new quantum-vulnerable keys, and API usage restrictions. Meta acknowledges that full migration will take years of phased work across protocols, products, and infrastructure.
My Analysis
I’ve been tracking enterprise PQC migration strategies for years, and Meta’s playbook represents a watershed moment. Not because of technical breakthroughs, but because it transforms PQC migration from abstract threat modeling into operational reality. When a company managing infrastructure for three billion users says “we’re already doing this,” it changes the conversation entirely.
The PQC Migration Levels model deserves particular attention. I’ve seen dozens of maturity models over my career, and most suffer from academic abstraction. Meta’s approach cuts through that. Five levels. Clear criteria. Measurable progress. The genius lies in making “PQ-Ready” an acceptable intermediate goal, acknowledging that perfect security tomorrow often loses to good-enough security today.
Compare this to the PQC Migration Framework I’ve been analyzing. Both frameworks recognize that migration happens in stages, but Meta’s model focuses on organizational readiness while the PQC Migration Framework emphasizes technical implementation phases. CISOs need both perspectives. Use Meta’s levels to assess where you stand. Use the PQC Migration Framework to plan how you’ll advance.
What strikes me most about Meta’s prioritization methodology is its brutal honesty about resource constraints. High-priority doesn’t mean “migrate immediately.” It means “migrate as soon as external dependencies allow.” This acknowledges a reality that vendor pitches often obscure: you can’t migrate to algorithms that don’t exist in your hardware or implement protocols that haven’t been standardized.
The Scale Problem
Meta’s scale creates unique challenges. When you’re processing billions of encrypted connections daily, even tiny performance penalties multiply into massive costs. Their preference for ML-KEM768 (NIST Security Level 3) with exceptions for ML-KEM512 reveals this tension. The playbook acknowledges what academic papers often miss: sometimes good-enough cryptography deployed universally beats perfect cryptography deployed partially.
But scale also brings advantages. Meta can dedicate entire teams to PQC migration. They can influence hardware vendors. They can contribute to standards development. Smaller organizations lack these luxuries, which makes Meta’s decision to share this playbook significant. They’re essentially open-sourcing years of internal planning.
External Dependencies: The Hidden Timeline
I appreciate Meta’s frank discussion of external dependencies. Too many PQC roadmaps pretend organizations control their own destiny. Meta identifies three blockers that actually determine migration timelines:
First, standards completion. While NIST has published ML-KEM and ML-DSA, the protocol-level standards remain works in progress. Meta specifically calls out missing TLS specifications and PQC PKI standards. Until these arrive, full migration stays theoretical.
Second, hardware support. If your cryptography runs in HSMs or leverages CPU acceleration, you’re waiting on vendors. Meta’s diplomatic phrase “working closely with hardware vendors” translates to “we’re pushing them hard but can’t make them move faster.”
Third, production implementations. Meta’s endorsement of LibOQS and contribution to fixing bugs demonstrates mature thinking. They understand that algorithm security means nothing if the implementation leaks keys through timing attacks.
The Hybrid Hedge
Meta’s strong preference for hybrid approaches (combining classical and post-quantum algorithms) reveals institutional memory. They reference SIKE’s dramatic failure during NIST standardization. For those who missed it, SIKE was a finalist that got completely broken by improved cryptanalysis. Years of implementation work, vanished overnight.
This conservatism makes sense. When you’re protecting billions of users, “move fast and break things” doesn’t apply to cryptography. The hybrid approach ensures that even if ML-KEM suffers SIKE’s fate, the classical layer maintains security. Yes, it doubles bandwidth costs. Yes, it complicates implementations. But it also lets security teams sleep at night.
Reading Between the Lines
Several unstated insights emerge from careful reading. Meta has “already begun deploying post-quantum encryption across internal infrastructure” but remains vague about external-facing services. This suggests internal systems got priority, probably because they’re easier to control and modify.
The extensive acknowledgments section reveals another truth: PQC migration touches everything. Transport security, messaging, payments, hardware, infrastructure, Reality Labs (Meta’s VR division). Every team that handles cryptography needs involvement. In my experience, this coordination challenge dwarfs the technical complexity.
The playbook’s emphasis on preventing new quantum-vulnerable deployments deserves highlighting. Meta suggests updating internal guidelines, warning against vulnerable key generation, and restricting API usage. This defensive approach acknowledges a painful reality: migration takes so long that you’ll create new technical debt while paying off the old unless you actively prevent it.
What CISOs Should Take Away
If you’re a CISO reading this, here’s what matters for your Monday morning:
Start with the levels assessment. Where does your organization sit on Meta’s five-level scale? Be honest. If you’re PQ-Unaware, acknowledge it and start climbing. If you’re PQ-Aware but not PQ-Ready, focus on building implementation capabilities before worrying about deployment.
Adopt Meta’s prioritization framework wholesale. High-priority means encryption and key exchange. Medium-priority means signatures. Low-priority means symmetric crypto with adequate key sizes. This simple categorization beats complex risk matrices for initial planning.
Accept external dependencies as timeline drivers, not excuses. You can’t accelerate NIST’s standardization process, but you can prepare for when standards arrive. Build crypto-agility into new systems. Create cryptographic inventories. Establish vendor relationships focused on PQC readiness.
Embrace hybrid approaches for initial deployments. Meta’s conservatism here reflects operational wisdom. The performance penalty beats the reputation penalty of being the company that bet everything on a broken algorithm.
Most importantly, start preventing new quantum-vulnerable deployments today. Every RSA key generated now becomes tomorrow’s migration task. Update your standards. Train your developers. Make quantum resistance the default for new projects, even if full migration remains years away.
The Normalization Effect
Meta’s public disclosure shifts PQC migration from future concern to present reality. When a company of this scale publishes detailed migration strategies, it signals that Q-Day deadlines have moved from theoretical to operational. The era of treating quantum threats as science fiction has ended.
I predict this publication will trigger similar disclosures from other hyperscalers. Amazon, Microsoft, and Apple face identical challenges. They’ve surely developed comparable frameworks internally. Meta’s openness creates pressure to share, accelerating industry-wide learning.
This matters because hyperscaler practices become de facto standards. When Meta recommends ML-KEM768 as the default choice, vendors listen. When they emphasize hybrid approaches, implementations follow. Their choices shape the ecosystem that smaller organizations inherit.
Beyond the Playbook
Meta’s framework provides scaffolding, but each organization must build their own structure. Your migration won’t look like Meta’s. You lack their resources but also their complexity. Use their levels for assessment, their priorities for planning, their dependencies for timeline reality checks. But adapt everything to your context.
I’ve spent years arguing against both quantum hype and quantum denialism. Meta’s playbook supports that balanced position perfectly. They acknowledge the threat without panic. They commit resources without hysteria. They share progress without declaring victory.
The playbook’s closing admission rings especially true: “Hardening Meta’s systems… takes years of phased work.” This honesty about timelines counters vendors promising turnkey quantum protection. Real PQC migration resembles enterprise Y2K remediation more than routine patching. It touches everything, takes forever, and requires sustained executive commitment.
As I’ve explored in my analysis of practical steps to quantum readiness, the journey matters as much as the destination. Meta’s willingness to share their journey accelerates everyone else’s. They’ve shown that PQC migration has evolved from research project to engineering challenge. The question for every organization has shifted from “if” to “how fast.”
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.