-
Cyber-Kinetic Security
Cybercrime in China – a Growing Threat for the Chinese Economy
Western publications often picture the People’s Democratic Republic of China (hereafter China) as the world’s chief propagator of cyberattacks. But the picture is much more complex than such broad-brush claims suggest. Few Westerners realize that China and its neighbours in…
Read More » -
Crypto Security

Why Financial Crime and Cybersecurity Need to Team up
The worlds of financial crime and cybercrime are colliding, converging into one. The biggest threat to businesses globally is the new cyber-enabled financial crime. Yet businesses and even financial institutions tasked with protecting our money continue to fight this combined…
Read More » -
Crypto Security

Financial Institutions: Key in Fighting Weapons of Mass Destruction
How would you picture those who work to prevent weapons of mass destruction (WMD) from falling into the wrong hands? Would you picture them heavily armed and with a military bearing? Then you might be surprised. Although such individuals sometimes…
Read More » -
Crypto Security

Combatting Money Laundering & Terrorist Financing
Terrorist funding detection has been practiced the same way as money laundering detection ever since Counter Terrorism Funding (CTF) initiatives were added to Anti–Money Laundering (AML) efforts after 9/11. Although the two have similarities on the surface, a deeper look…
Read More » -
Quantum Computing

Understanding “Polynomial Time” – Why Faster Algorithms Matter
Quantum computing has emerged as a new frontier of great-power competition in the 21st century. Nations around the world view advanced quantum technologies as strategic assets—keys to future economic prowess, military strength, and technological sovereignty. Governments have already poured over…
Read More » -
Crypto Security

Financial Crime, Money Laundering and Terrorism Financing
In what ways has financial crime hurt you? Most people would respond with a yawn. We might think it is limited to a few fraudulent schemes that deprive a small number of people of a few hundred or a few…
Read More » -
Leadership

Enterprise Resilience – A Model to Thrive in a World of Change
Modern theories of the firm remain focused on transaction costs, operational efficiency, employee motivation, leadership, strategy and other related factors. While any of these may support our success at various times, none of them alone will facilitate it in the…
Read More » -
Cyber-Kinetic Security

When Hackers Threaten your Life – Cyber-Kinetic Risks
The attacker stepped out from behind a hedge in the upper-class suburban neighborhood, being careful to stay in the shadows. Across the street, the last lights shining through the windows of the house had just flickered out. She tugged the…
Read More » -
Quantum Computing

Key Principles and Theorems in Quantum Computing and Networks
The landscape of quantum computing and quantum networks is an exciting frontier where physics and cybersecurity intersect. We’re witnessing the early days of this quantum revolution. As quantum hardware scales and quantum protocols move from labs to real-world deployment, security…
Read More » -
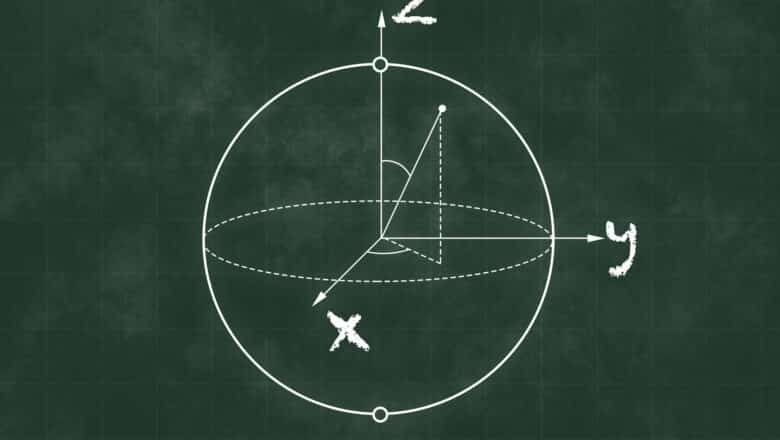
Quantum Computing

Qubits: A Brief Introduction for Cybersecurity Professionals
A qubit is the quantum analog of a classical bit – it’s the basic unit of quantum information. However, unlike a classical bit that can only be 0 or 1 at any given time, a qubit can exist in a…
Read More » -
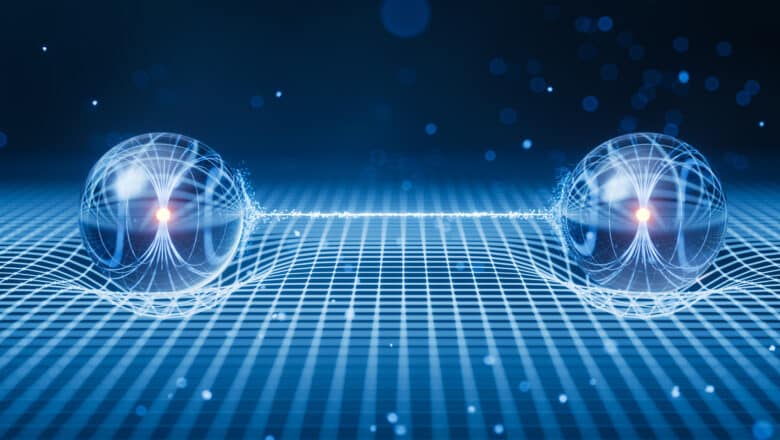
Quantum Computing

Bell States: An Introduction for Cybersecurity Professionals
Bell states are a set of four specific quantum states of two qubits (quantum bits) that are entangled. In simple terms, an entangled pair of qubits behaves as one system, no matter how far apart they are. Bell states are…
Read More » -
Cyber-Kinetic Security

Human Zombification as an Information Security Threat
China and Russia share an information security doctrine, one that is significantly different from Euro-Atlantic doctrines. In the Chino-Russian model of information space a discussion about population zombification does happen and it fits squarely within the domain of information security.…
Read More » -
Cyber-Kinetic Security

Non-Executive Directors as Cyber Champions
As a non-executive director (NED) who often represents cybersecurity and emerging technology interests on boards, I’ve learned that even without being a deep technical expert, I must challenge management and ensure our company’s security posture is sound. In today’s high-risk…
Read More » -
Leadership

Can we Rescue Diversity from its own Failings?
Don’t expect this to be either of the typical articles about diversity. I’m here not to fawn over its benefits nor to rant about who does or doesn’t get hired. I’m here, instead, to ask why we react to it…
Read More » -
Leadership

Innovative Businesses Have Curious Employees
Several comments in response to my recent competency-focused post led me to also consider the importance of curiosity in the workplace. Interestingly enough, recent experiences have given me a chance to see firsthand the benefits of nurturing curiosity and how to do…
Read More »