-
Post-Quantum, PQC, Quantum Security
Cryptographic Stack in Modern Interbank Payment Systems
International interbank payments rely on multiple layers of classical cryptography to ensure security from end to end. When a user initiates a cross-border transfer at their local bank, cryptographic mechanisms protect the transaction at every stage - from the customer’s…
Read More » -
Quantum Computing Modalities
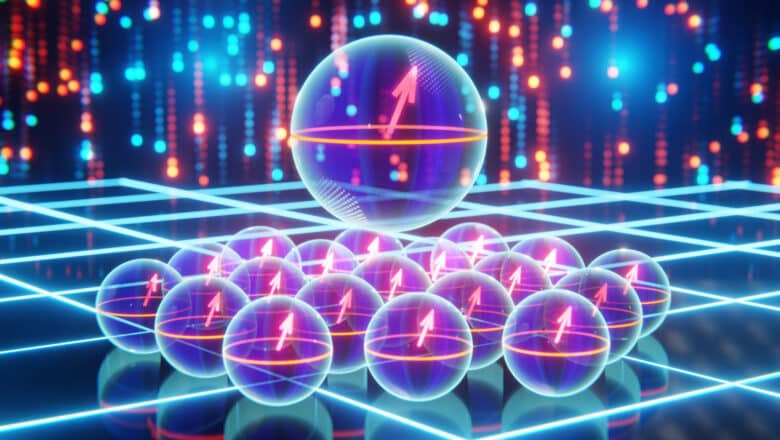
Quantum Computing Modalities: Spin Qubits in Other Semiconductors & Defects
In addition to silicon, spin qubits can be realized in other solid-state systems. One well-known example is the nitrogen-vacancy (NV) center in diamond, which is a point defect where a nitrogen atom next to a vacancy in the carbon lattice…
Read More » -
Quantum Computing Modalities
Quantum Computing Modalities: Silicon-Based Qubits
Silicon-based quantum computing refers to qubits implemented using silicon semiconductor technology, leveraging the existing CMOS fabrication infrastructure. The most common silicon qubit implementations are spin qubits – using the spin of an electron or the spin of an atomic nucleus…
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Cryptography (PQC) and Network Connectivity: Challenges and Impacts
PQC brings new dependencies between cryptography and network connectivity. Unlike the relatively small and efficient crypto of the past, post-quantum algorithms force us to consider link capacity, latency, and device limitations as first-class concerns in security design. Some network environments…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Measurement-Based Quantum Computing (MBQC)
Measurement-Based Quantum Computing (MBQC), also known as the one-way quantum computer, is a paradigm where quantum computation is driven entirely by measurements on an entangled resource state. Instead of applying a sequence of unitary gates to a register of qubits,…
Read More » -
Quantum Security & PQC

New Coalition Launched to Tackle Post-Quantum Cryptography
The MITRE Corporation has announced the formation of the Post-Quantum Cryptography Coalition, a collaborative effort to address the imminent threats posed by quantum computing to current cryptographic systems. The coalition aims to accelerate the development and adoption of quantum-resistant cryptographic…
Read More » -
Quantum Computing Modalities

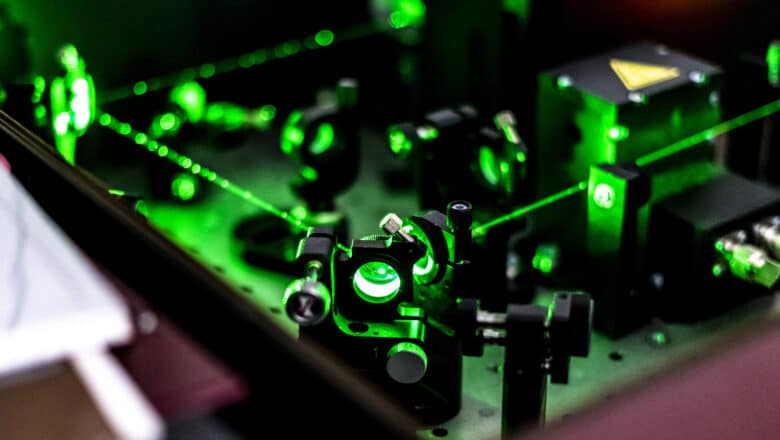
Quantum Computing Modalities: Neutral Atom (Rydberg)
Neutral atom quantum computing uses uncharged atoms (as opposed to ions) trapped by light in an array, with qubits encoded typically in atomic states. A popular approach is to use optical tweezers (focused laser beams) to trap arrays of neutral…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Quantum Annealing (QA)
Quantum annealing (QA) is a special-purpose quantum computing paradigm designed to solve optimization problems by exploiting quantum tunneling and the adiabatic principle. It's a special case of Adiabatic Quantum Computing (AQC). The idea is to encode a problem (typically an…
Read More » -
Society 5.0

Saudi Arabia Vision 2030: Cybersecurity at the Core of Transformation
Last week, the Saudi Data and Artificial Intelligence Authority (SDAIA) launched a nationwide awareness campaign called “Ask Before”, intended to educate the public about the significance of personal data ahead of the implementation of a new national personal data protection system. Emphasizing…
Read More » -
AI Security

AI Security 101
Artificial Intelligence (AI) is no longer just a buzzword; it’s an integral part of our daily lives, powering everything from our search for a perfect meme to critical infrastructure. But as Spider-Man’s Uncle Ben wisely said, “With great power comes…
Read More » -
Leadership

Why We Seriously Need a Chief AI Security Officer (CAISO)
With AI’s breakneck expansion, the distinctions between ‘cybersecurity’ and ‘AI security’ are becoming increasingly pronounced. While both disciplines aim to safeguard digital assets, their focus and the challenges they address diverge in significant ways. Traditional cybersecurity is primarily about defending…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Quantum Walk QC
Quantum walks are the quantum-mechanical counterparts of classical random walks. In a classical random walk, a "walker" (such as a particle or an agent) moves step by step in a certain space (like a line or a graph) with some…
Read More » -
AI Security

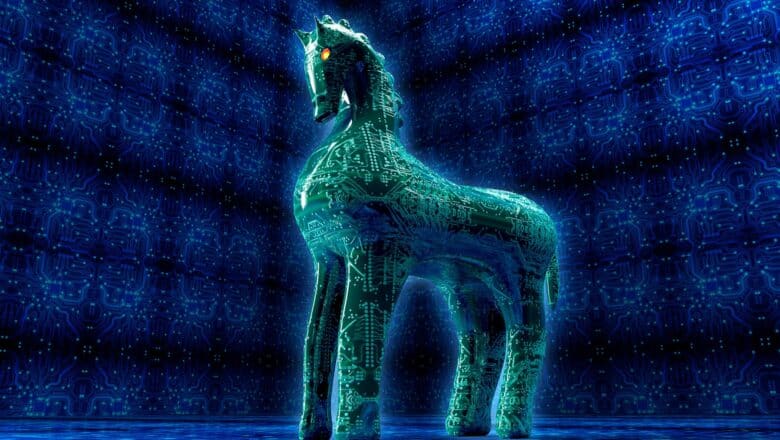
How to Defend Neural Networks from Trojan Attacks
Neural networks learn from data. They are trained on large datasets to recognize patterns or make decisions. A Trojan attack in a neural network typically involves injecting malicious data into this training dataset. This 'poisoned' data is crafted in such…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Fibonacci Anyons
Fibonacci anyons are a type of non-Abelian anyon – exotic quasiparticles that can exist in two-dimensional systems and have exchange statistics beyond bosons or fermions. When two non-Abelian anyons like Fibonacci anyons are exchanged (braided) in space, the quantum state…
Read More » -
Q-Day

What Will Really Happen Once Q-Day Arrives – When Our Current Cryptography Is Broken?
As the world edges closer to the era of powerful quantum computers, experts warn of an approaching “Q-Day” (sometimes called Y2Q or the Quantum Apocalypse): the day a cryptographically relevant quantum computer can break our current encryption. Unlike the Y2K…
Read More »