Deep Dive Series
Quantum Sovereignty
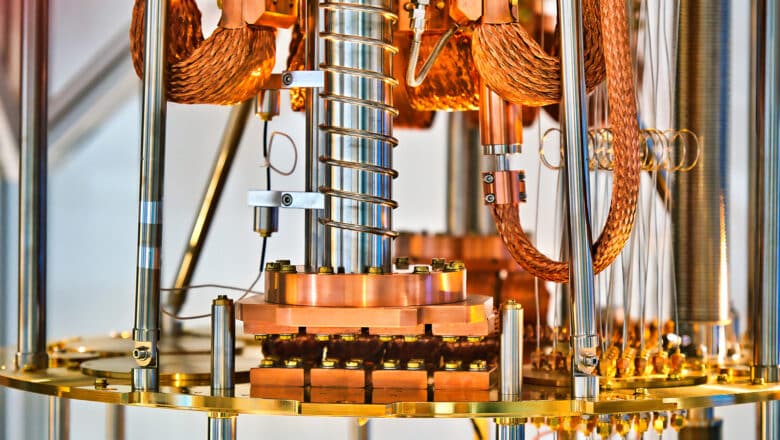
Quantum technology is no longer a laboratory curiosity — it is entering the machinery of national power. The ability to build, operate, trust, and control quantum capabilities under geopolitical stress, without being cut off, is becoming a defining question for governments, defense establishments, and critical infrastructure operators. Export controls now cover quantum computing hardware. PQC standardization is reshaping trust boundaries around cryptographic choices. Supply chains for enabling technologies — from dilution refrigerators to isotopically purified silicon — are geographically concentrated in ways that create leverage and vulnerability simultaneously.
This Deep Dive series treats quantum sovereignty as more than a slogan. Across multiple articles, I trace how deep physics becomes geopolitical leverage, how that leverage reshapes alliances and markets, and how strategy ultimately turns into architecture: procurement rules, vendor dependencies, standards, and cryptographic choices. The series overview provides the structural map and reading order; the individual articles go deeper on each dimension of the sovereignty question.
-
The Quantum Utility Map

Quantum Sovereignty and the Utility Trap
The industries where quantum computing creates the most value are the industries most critical to national security. The hardware serving them is concentrated in a handful of companies and countries. The architectural decisions determining whether access is sovereign or dependent are being made now. This article explains the trap and how to avoid it
Read More » -
China's Quantum Ambition

China’s Quantum Supply Chain: How Export Controls Are Building What They Sought to Prevent
In June 2023, a Zhejiang University graduate named Chen Jie sat for an interview with a Chinese tech columnist. Chen had founded a cryogenics company called CSSC Pengli in Nanjing thirteen years earlier — a subsidiary of China State Shipbuilding Corporation that made cooling systems for MRI machines. Nobody in the West had heard of him. His company had just been placed on the US…
Read More » -
Quantum Sovereignty

Quantum Sovereignty in Practice: When Geopolitics Becomes Architecture
At its core, quantum sovereignty means having full control over the critical layers of quantum technology domestically - the ability to design, manufacture, and operate quantum systems without external dependency. In practice, this implies a country could build a complete full-stack quantum ecosystem entirely within its national borders: from quantum chips and cryogenic hardware to software, algorithms, and encryption protocols. The allure of this vision…
Read More » -
Quantum Sovereignty

Sovereignty Stress Tests: Tabletop Scenarios for States and Enterprises
In an era of quantum and digital sovereignty, governments and companies must ensure they aren’t caught off-guard by geopolitical tech disruptions. Building on my previous analyses of quantum sovereignty and a number of Applied Quantum client engagements, I wanted to offer a practical scenario toolkit to “stress test” sovereignty. Instead of chasing total self-sufficiency, the goal is sovereign optionality - staying integrated in global tech…
Read More » -
Quantum Sovereignty

Investment Screening and M&A: When Capital Becomes a Quantum Sovereignty Vector
Foreign investment screening, acquisition scrutiny, and “strategic capital” policies increasingly shape which quantum technology companies survive - and where their intellectual property (IP) and talent ultimately reside. National security and technological sovereignty narratives are no longer abstract concerns; they influence the day-to-day decisions of quantum startups. The Sovereignty Stakes in Quantum Investment Quantum technologies are widely seen as strategic, dual-use innovations at the nexus of…
Read More » -
Quantum Sovereignty

Quantum Sovereign Optionality: Agility Over Autarky
Technical sovereignty has become a buzzword in geopolitical and tech circles. As global alliances fray and trust in traditional partners wanes, countries are scrambling to assert control over critical technologies. In the quantum arena, this instinct translates into an ambitious goal: build a complete, full-stack quantum ecosystem entirely within national borders. The allure is understandable – quantum computers, sensors, and communications could be as transformational…
Read More » -
Quantum Sovereignty

Sovereign Quantum Clouds and National Control
Quantum computing is rapidly shifting from lab prototypes to cloud-based services. Most organizations will access quantum capabilities “as a service” through cloud platforms, rather than owning a quantum computer on-premise. This shift reframes the sovereignty debate. The question is no longer simply “Who owns the qubits?” but rather “Who controls the access to those qubits?” When quantum processing is delivered via remote services, national and…
Read More » -
Quantum Sovereignty

Chokepoints and Industrial Base Realism: What “Quantum Supply Chain Sovereignty” Actually Means
Talk of quantum sovereignty - a nation’s independent control over quantum technology - means little unless backed by tangible supply chain control. Quantum innovation relies on narrow, specialized supply chains that are globally dispersed and often fragile. Major powers have realized this and are pivoting from pure research funding to securing the physical and human infrastructure for a quantum industry. The objective is to ensure…
Read More » -
Post-Quantum, PQC, Quantum Security

Sovereignty in the PQC Era: Standards, Trust, and Crypto-Agility
Post-Quantum Cryptography (PQC) is entering the standards stage, with the U.S. National Institute of Standards and Technology (NIST) recently selecting the first quantum-resistant algorithms. However, the future of PQC will not be as straightforward as simply adopting NIST’s choices globally. A strong push for digital sovereignty is emerging around the world, driven by eroding trust in foreign (particularly U.S.) technology. Nations are seeking greater control…
Read More » -
Quantum Sovereignty

The Border Around Quantum: Export Controls, Deemed Exports, and “Research as a Controlled Flow”
Export controls have emerged as a main lever to throttle or channel the flow of quantum know-how and equipment, effectively drawing new borders through the global R&D ecosystem. Quantum sovereignty, in other words, isn’t just about spending more on R&D; it’s about enforcing boundaries on that R&D. The U.S. has led the charge by expanding export restrictions on advanced quantum technologies in the name of…
Read More »
- 1
- 2