All Post-Quantum, PQC Posts
-
Post-Quantum, PQC, Quantum Security
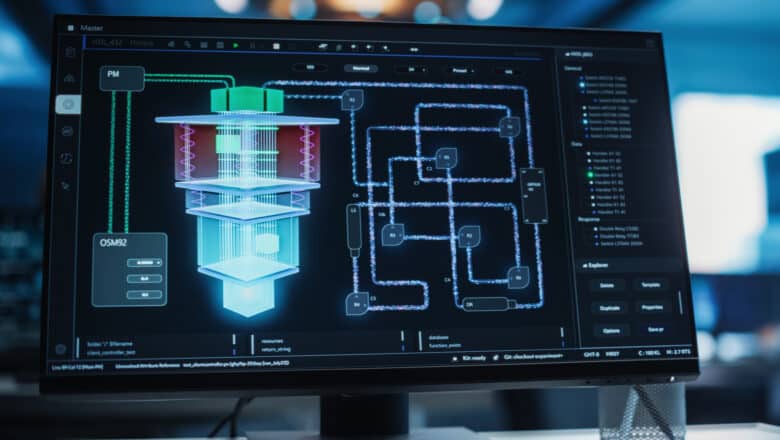
Securing Quantum Computers – Threat at the Quantum-Classical Interface
A global race is on to build cryptographically relevant quantum computers (CRQCs) - machines powerful enough to break current encryption. Governments and industry are pouring billions into quantum R&D, and intelligence analysts scrutinize whether a geopolitical rival might secretly be ahead. Yet amid this focus on who builds a quantum codebreaker first, an alternative threat vector is often overlooked: an adversary might not need to…
Read More » -
Post-Quantum, PQC, Quantum Security

Q-Day Isn’t an Outage – It’s a Confidence Crisis
Cybersecurity lore often paints Q-Day (the moment a quantum computer cracks RSA/ECC encryption) as an instant "Quantum Apocalypse" where every system gets hacked immediately. Planes falling from the sky, banks drained in seconds, an overnight digital Armageddon - if that nightmare doesn’t happen, some assume Q-Day wasn’t so bad after all. But this view misses a crucial point. The real catastrophe of Q-Day isn’t that…
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Negligence: Legal Risks of Failing to Prepare for the Quantum Threat
Quantum computing is no longer a far-off hypothesis - it’s a rapidly emerging reality that could render today’s encryption obsolete. For CISOs and their boards, this means a new kind of cybersecurity crisis is on the horizon. Sensitive data that is safely encrypted now may be sitting like a ticking time bomb, waiting to be cracked by tomorrow’s quantum machines. The message is clear: security…
Read More » -
Post-Quantum, PQC, Quantum Security

PQC First but Not Last for Quantum Resilience
Because of PQC upgrade challenges, an exclusive focus on “big‑bang” PQC migration can leave critical assets unprotected for years. Complementary mitigations such as hybrid key exchanges, tokenisation, crypto‑gateways, isolation tiers, confidential‑computing enclaves, PFED‑style dual‑layer encryptors, and even niche options like QKD, provide defence‑in‑depth while the PQC rollout matures.
Read More » -
Post-Quantum, PQC, Quantum Security

Sovereignty in the PQC Era: Standards, Trust, and Crypto-Agility
Post-Quantum Cryptography (PQC) is entering the standards stage, with the U.S. National Institute of Standards and Technology (NIST) recently selecting the first quantum-resistant algorithms. However, the future of PQC will not be as straightforward as simply adopting NIST’s choices globally. A strong push for digital sovereignty is emerging around the world, driven by eroding trust in foreign (particularly U.S.) technology. Nations are seeking greater control…
Read More » -
Post-Quantum, PQC, Quantum Security

Trust Now, Forge Later (TNFL) – The Overlooked Quantum Threat
What is "Trust Now, Forge Later" (TNFL)? Most discussions about quantum computing threats focus on “Harvest Now, Decrypt Later” (HNDL) - the idea that adversaries can collect encrypted data today and store it, hoping a future quantum computer will break the encryption and expose sensitive information. This risk is very real, especially for data that needs to remain confidential for decades (think government secrets, health…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Readiness Is Not (Just) a Vendor Problem
In the recent IBM's “Secure the Post-Quantum Future” report 62% of executives admitted that their organization is waiting for vendors to make them quantum‑safe. In other words, they expect cloud providers, network equipment makers and software vendors to embed post‑quantum cryptography (PQC) so that internal teams can simply apply updates. This mindset is understandable - modern enterprises depend on vast supply chains - but it…
Read More » -
Post-Quantum, PQC, Quantum Security

Getting Started With Quantum Security and PQC Migration
Your complete roadmap to quantum-proofing your organization — from boardroom mandate to operational crypto-agility. This practitioner-curated Deep Dive series collects the PostQuantum.com articles you need to launch and run a quantum-readiness program, organized along the lifecycle most teams actually follow: securing executive buy-in and budget, performing cryptographic discovery and inventory, building a Cryptographic Bill of Materials (CBOM), scoring and prioritizing risk, standing up governance and…
Read More »