All Post-Quantum, PQC Posts
-
Post-Quantum, PQC, Quantum Security
CRQC Readiness Benchmark vs. Quantum Threat Tracker (QTT)
I will try and compare my proposed CRQC Readiness Benchmark with QTT, highlighting fundamental differences in methodology, assumptions, and philosophy, all in an effort to clarify how each approach informs our understanding of the looming “Q-Day.” The goal is to articulate why my benchmark and QTT produce different outlooks (2030s vs. 2050s for RSA-2048), and how both can be used together to guide post-quantum readiness.
Read More » -
Q-Day

The Trouble with Quantum Computing and Q-Day Predictions
The trouble with quantum computing predictions so far has been that too many have been more speculation than science, more influenced by bias than by balanced analysis. We have the tools and knowledge to do better. By embracing a data-driven, scenario-based approach, we can turn timeline forecasting from a source of confusion into a valuable planning aid.
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Tech and Espionage: What Every Researcher Must Know
To the untrained eye, espionage against scientists can be nearly invisible - it blends into everyday academic or business activity. But certain red flags and tactics surface again and again. Below is a consolidated list of common espionage methods (many from my own firsthand cases) used to target quantum tech researchers and organizations:
Read More » -
Post-Quantum, PQC, Quantum Security
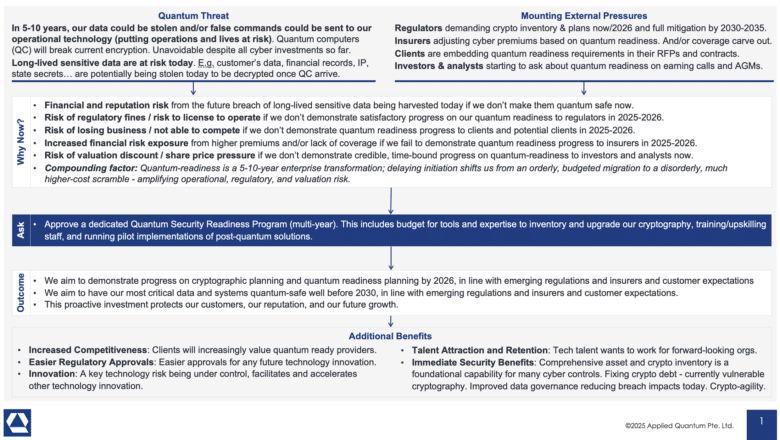
Securing Quantum Readiness Budget Now
From a CISO and business leadership perspective, the ask is clear: we need to secure budget and resources now to begin the multi-year journey of quantum-proofing our organization. This includes funding for risk assessments, cryptographic inventory tools, new encryption software/hardware, staff training or hiring, and pilot projects to start integrating PQC. The investment is justified not only by the avoidance of a potentially catastrophic future…
Read More » -
Post-Quantum, PQC, Quantum Security

Risk-Driven Strategies for Quantum Readiness When Full Crypto Inventory Isn’t Feasible
Given the practical challenges, organizations may need to begin their quantum-readiness journey with a risk-driven approach rather than a theoretically perfect one. The essence of this strategy is to focus limited resources where they matter most – addressing the highest quantum-vulnerability risks first and implementing interim safeguards for the rest. Even the U.S. government’s guidance recognizes the need for prioritization. For example, the federal memo…
Read More » -
Leadership

What is the Quantum Threat? A Guide for C‑Suite Executives and Boards
Boards do not need to dive into the scientific intricacies of qubits and algorithms, but they do need to recognize that this is a strategically important risk – one that can’t be simply delegated away. It requires the same level of governance attention as other enterprise-level risks like financial compliance, geopolitical factors, or pandemic preparedness. The comforting news is that if organizations act early, the…
Read More » -
Post-Quantum, PQC, Quantum Security

How CISOs Can Use Quantum Readiness to Secure Bigger Budgets (and Fix Today’s Problems)
Quantum readiness is not an exercise in science fiction – it’s a very practical program that yields benefits immediately. Regulators are pushing us all in this direction, which means boards are willing to fund it. The journey forces you to finally catalog your cryptographic assets and clean up long-standing weaknesses, improving your security posture right now. It builds agility so you can handle any crypto…
Read More » -
Post-Quantum, PQC, Quantum Security

CRQC Readiness Benchmark – Benchmarking Quantum Computers on the Path to Breaking Cryptography
Benchmarking quantum capabilities for cryptography is both critical and challenging. We can’t rely on any single metric like qubit count to tell us how near we are to breaking RSA-2048. A combination of logical qubit count, error-corrected circuit depth, and operational speed must reach certain thresholds in unison. Existing benchmarks – Quantum Volume, Algorithmic Qubits, etc. – each address parts of this, but a CRQC-specific…
Read More »