-
Post-Quantum, PQC, Quantum Security
Mitigating Quantum Threats Beyond PQC
The article explores limitations of PQC and explores alternative and complementary approaches to mitigate quantum risks. It provides technical analysis of each strategy, real-world examples of their deployment, and strategic recommendations for decision-makers. The goal is to illuminate why a…
Read More » -
Post-Quantum, PQC, Quantum Security
Introduction to Crypto-Agility
As we edge closer to the Q-Day—the anticipated moment when quantum computers will be capable of breaking traditional cryptographic systems—the need for crypto-agility becomes increasingly critical. Crypto-agility is the capability of an organization to swiftly and efficiently transition between different…
Read More » -
Research
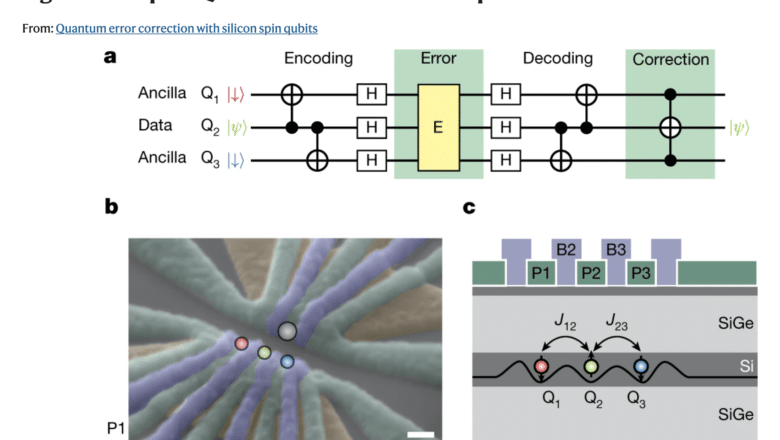
Silicon’s First Attempts at Self-Repair: Phase-Flip Error Correction Demonstrated in Semiconductor Spin Qubits
25 Aug 2022 - Seven months ago, three teams simultaneously proved that silicon spin qubits could operate above the fault-tolerance threshold — the quality of individual gates good enough, in principle, for error correction to work. That was the prerequisite.…
Read More » -
AI Security

Perturbation Attacks in Text Classification Models
Text Classification Models are critical in a number of cybersecurity controls, particularly in mitigating risks associated with phishing emails and spam. However, the emergence of sophisticated perturbation attacks poses substantial threats, manipulating models into erroneous classifications and exposing inherent vulnerabilities.…
Read More » -
Industry

CHIPS and Science Act of 2022 Signed: A Quantum Leap for U.S. Tech
President Joe Biden signed the CHIPS and Science Act (H.R. 4346, Public Law 117-167) into law on August 9, 2022 - a historic $280 billion package aimed at boosting U.S. high-tech manufacturing and research. While best known for providing $52 billion to…
Read More » -
Crypto Security

Trying to Solve the Mysterious $200M BitMart Hack
A missing pile of Safemoon and other cryptocurrencies, accusations of broken promises, and then nothing. When a high-profile cyber attack takes place and hundreds of millions of dollars are lost, usually a healthy balance is struck between safeguarding information to…
Read More » -
Industry

D-Wave Goes Public on the NYSE
D-Wave achieved a significant corporate milestone by listing on the New York Stock Exchange under the ticker “QBTS”. The public debut came via a merger with a SPAC (special-purpose acquisition company) and made D-Wave one of only three quantum computing…
Read More » -
AI Security

How Multimodal Attacks Exploit Models Trained on Multiple Data Types
In simplest terms, a multimodal model is a type of machine learning algorithm designed to process more than one type of data, be it text, images, audio, or even video. Traditional models often specialize in one form of data; for…
Read More » -
Crypto Security

Why DevSecOps is Essential for the Blockchain Ecosystem
In recent years, many organizations have adopted more modern development practices, including Agile, Scrum, and DevOps. The goal of these new processes is to improve the pace and efficiency of development by streamlining the development process and using automation whenever…
Read More » -
Crypto Security

What the $534M Coincheck Hack Taught Us All About Safe Storage of Digital Assets
The biggest crypto heist in history at the time it occurred in 2018 was an eye-opener for many reasons, not least of which for the way the stolen assets were being stored. Seasoned crypto enthusiasts and early adopters of the…
Read More » -
Crypto Security

Security Threats to Blockchain Networks – 6 – Wallet Attacks
Wallet Attacks: A Deep-dive Wallets are a logical target for cyber-attacks, along with the emerging institutions that hold custody of them on users’ behalf. While secured with technically unbreakable code, hackers have found numerous ways to gain illicit access to…
Read More » -
Crypto Security

What the Biggest Blockchain Game’s Hack Reveals about the Future of Crypto Adoption
Axie Infinity’s Ronin Bridge Hack for $551M worth of crypto assets could paradoxically lead to higher rates of blockchain adoption by showing that it’s a lot easier to track stolen cryptocurrency than people think. The popular misconception that cryptocurrencies are…
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Cryptography (PQC) Introduction
Post-Quantum Cryptography (PQC) refers to cryptographic algorithms (primarily public-key algorithms) designed to be secure against an attack by a future quantum computer. The motivation for PQC is the threat that large-scale quantum computers pose to current cryptographic systems. Today’s widely…
Read More » -
Crypto Security

Security Threats to Blockchain Networks – 5 – Consensus Attacks
Consensus Attacks: A Deep-dive Where centralized systems operate on the basis of centralized permission, blockchain protocols proceed on the basis of decentralized consensus. While this is more secure in theory, the system is not flawless. All blockchains are susceptible to…
Read More » -
Quantum Networks

Quantum Teleportation
Quantum teleportation is a process by which the state of a quantum system (a qubit) can be transmitted from one location to another without physically sending the particle itself. Quantum teleportation has become a foundational method in quantum communication, envisioned…
Read More »