-
Crypto Security

Mapping Dark Web SIM Swapping Economy
In the U.S. alone, SIM-swapping attacks resulted in $72 million worth of losses last year, four-million dollars more than 2021, according to the Federal Bureau of Investigation. In a 2022 public service announcement, the FBI defined SIM swapping as a…
Read More » -
Post-Quantum, PQC, Quantum Security
Cybersecurity Negligence and Personal Liability: What CISOs and Board Members Need to Know
“Could I personally be sued or fined if our company gets breached?” This uneasy question is crossing the minds of many CISOs and board members lately. High-profile cyber incidents and evolving regulations have made it clear that cybersecurity is not…
Read More » -
Quantum Computing

The Skill Stack a CISO Needs for Crypto‑Agility and Quantum Readiness
The path to quantum readiness is navigable with the right combination of skills, planning, and proactive execution. By leveraging existing strengths - the people and processes you already have - an enterprise can evolve its cryptographic foundations without needing a…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Security: Understanding the Terminology and Context
"Quantum security" is a term that is increasingly being used. With everyone having their own definition of the term. It can carry multiple meanings depending on context, but so do other related terms. The whole field is fairly new and…
Read More » -
Post-Quantum, PQC, Quantum Security

Upgrading Operational Technology (OT) Systems to Post‑Quantum Cryptography (PQC): Challenges and Strategies
Operational Technology (OT) environments, such as industrial control systems and critical infrastructure, are especially at risk due to their long-lived devices and infrequent updates. Many OT systems deployed today will still be in use a decade or two from now,…
Read More » -
Policy & Sovereignty

UK NCS Issues Guidance on Preparing for PQC
The UK National Cybersecurity Centre (NCSC) has released a whitepaper titled “Next Steps in Preparing for Post-Quantum Cryptography,” which provides comprehensive guidance to help organisations and providers of Critical National Infrastructure (CNI) prepare for the migration to post-quantum cryptography (PQC).…
Read More » -
Crypto Security

Verified Crypto Account Listings Proliferate on the Dark Web
Verified crypto-exchange accounts have become a hot commodity on the dark web, with login credentials available for as little as $20, according to May data from threat intelligence firm Privacy Affairs. But the price for verified crypto accounts has been…
Read More » -
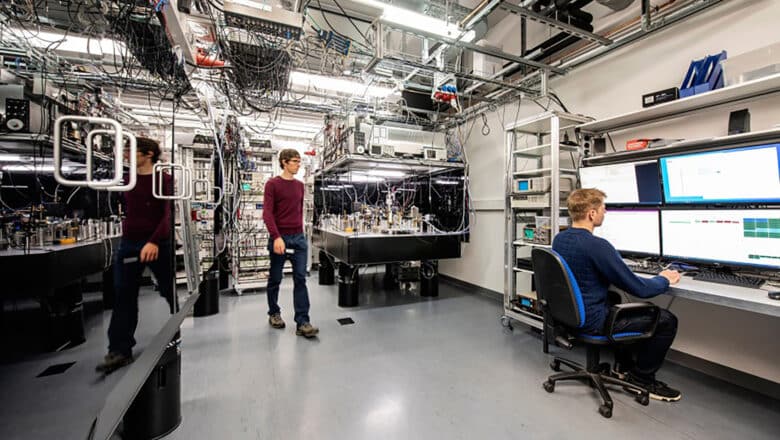
Quantum Computing Modalities

Taxonomy of Quantum Computing: Modalities & Architectures
A comprehensive field guide to every way humanity is trying to build a quantum computer — and why it matters that there isn't just one. This Deep Dive series surveys the full landscape of quantum computing modalities and architectures: from…
Read More » -
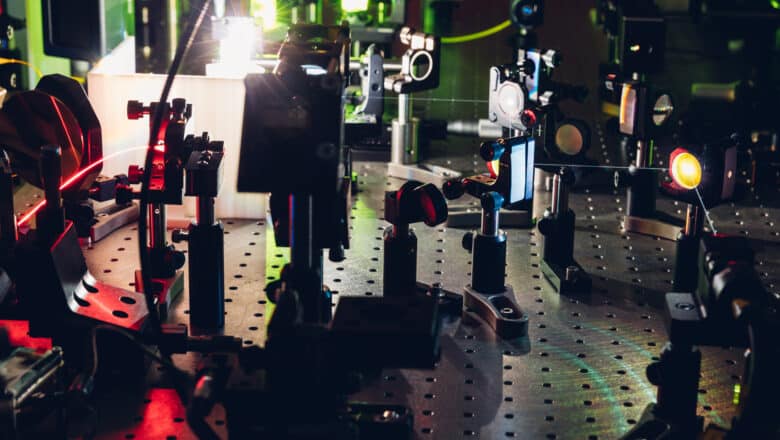
Research

99.5% Fidelity in Neutral-Atom Qubits Achieved
A team of researchers from Harvard University, MIT, and QuEra have achieved two-qubit entangling gates with 99.5% fidelity on 60 neutral atom qubits operating simultaneously. This milestone represents a crucial step towards the practical application of quantum computing in commercial…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Photonic Cluster-State
Photonic Cluster-State Computing is a form of quantum computing in which information is processed using photons (particles of light) that have been prepared in a highly entangled state known as a cluster state. It falls under the paradigm of measurement-based…
Read More » -
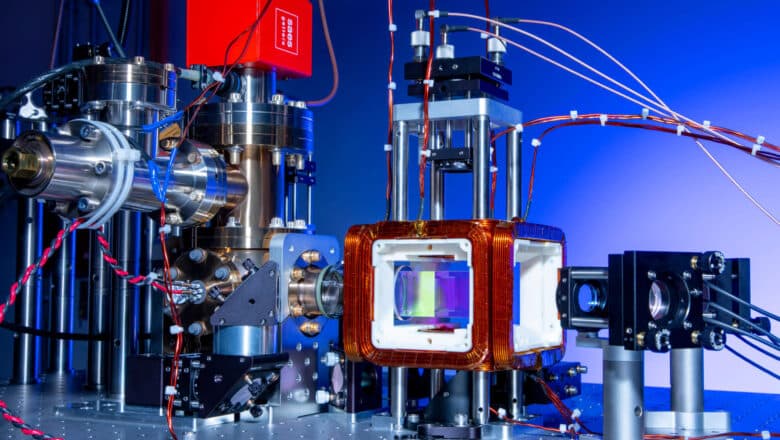
Research

Over 1,000 Controllable Atomic Qubits Achieved
In a research article just published on the arXiv preprint server the research team from TU Darmstadt in Germany reports on the world’s first successful experiment to realise a quantum-processing architecture that contains more than 1,000 atomic qubits in one single plane.…
Read More » -
Post-Quantum, PQC, Quantum Security

Quantum Risk: The Coming Cryptography Reckoning
In a secure data center somewhere, an adversary is quietly stockpiling encrypted emails, financial transactions, and state secrets - betting that within a decade a new kind of machine will decrypt them in minutes. This scenario underpins what cybersecurity experts…
Read More » -
Quantum Computing

Quantum Memories in Quantum Networking and Computing
Quantum memories are devices capable of storing quantum states (qubits) in a stable form without collapsing their quantum properties. In essence, a quantum memory is the quantum-mechanical analog of classical computer memory or RAM.
Read More » -
Quantum Sensing

Quantum LiDAR vs. Quantum Radar
Quantum radar and quantum LiDAR are no longer science fiction – they are emerging reality, albeit in early stages. They differ in technology and likely timelines: expect to hear more about quantum LiDAR in commercial products soon, while quantum radar…
Read More » -
Quantum Computing Modalities

Quantum Computing Modalities: Ion Trap and Neutral Atom MBQC
Ion Trap and Neutral Atom implementations of MBQC leverage two leading “matter-qubit” platforms – trapped ions and ultracold neutral atoms – to realize this model. In a trapped-ion MBQC, a string of ions (charged atoms) is confined and entangled via…
Read More »