Post-Quantum, PQC, Quantum Security
PostQuantum.com – Industry news and blog on Quantum Computing, Quantum Security, PQC, Post-Quantum, AI Security
-
Stop the Quantum Fear-Mongering – It Helps No One
Fear sells - or so some vendors seem to think. For decades, a steady drumbeat of ominous warnings has proclaimed that a cryptography-breaking quantum computer is just around the corner. At security conferences and in sales pitches, I’ve had vendors lean in and whisper dramatic claims: “A friend at Fort…
Read More » -
Entanglement-Based QKD Protocols: E91 and BBM92
While prepare-and-measure QKD currently leads the market due to simplicity and higher key rates, entanglement-based QKD protocols like E91 and BBM92 are at the heart of next-generation quantum communications. Ongoing improvements in photonic technology are steadily closing the gap in performance. The additional security guarantees (e.g., tolerance of untrusted devices)…
Read More » -
Quantum Key Distribution (QKD) and the BB84 Protocol
Quantum Key Distribution (QKD) represents a radical advancement in secure communication, utilizing principles from quantum mechanics to distribute cryptographic keys with guaranteed security.Unlike classical encryption, whose security often relies on the computational difficulty of certain mathematical problems, QKD's security is based on the laws of physics, which are, as far…
Read More » -
The Quantum Computing Threat
The secret sauce of quantum computing, which even Einstein called "spooky," is the ability to generate and manipulate quantum bits of data or qubits. Certain computational tasks can be executed exponentially faster on a quantum processor using qubits, than on a classical computer with 1s and 0s. A qubit can…
Read More » -
Inside ITU’s New Quantum Key Standard (Y.3800)
In late 2019, the International Telecommunication Union (ITU) quietly reached a milestone in cybersecurity: it approved a new standard that could redefine how we secure data in the coming quantum era. The standard, known as ITU-T Recommendation Y.3800, is an “Overview on networks supporting Quantum Key Distribution” - essentially a…
Read More » -
Challenges of Upgrading to Post-Quantum Cryptography (PQC)
The shift to post-quantum cryptography is not a distant problem but an imminent challenge that requires immediate attention. The quantum threat affects all forms of computing—whether it’s enterprise IT, IoT devices, or personal electronics. Transitioning to quantum-resistant algorithms is a complex, resource-intensive task that demands coordination across the supply chain,…
Read More » -
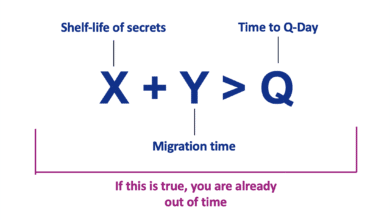
Mosca’s Theorem and Post‑Quantum Readiness: A Guide for CISOs
Mosca’s Theorem is a risk framework formulated to help organizations gauge how urgent their post-quantum preparations should be. It is often summarized by the inequality X + Y > Q, where: X = the length of time your data must remain secure (the required confidentiality lifespan of the information). Y…
Read More » -
Q-Day (Y2Q) vs. Y2K
In the late 1990s, organizations worldwide poured time and money into exorcising the “millennium bug.” Y2K remediation was a global scramble. That massive effort succeeded: when January 1, 2000 hit, planes didn’t fall from the sky and power grids stayed lit. Ever since, Y2K has been held up as both…
Read More » -
What’s the Deal with Quantum Computing: Simple Introduction
Quantum computing holds the potential to revolutionize fields where classical computers struggle, particularly in areas involving complex quantum systems, large-scale optimization, and cryptography. The power of quantum computing lies in its ability to leverage the principles of quantum mechanics—superposition and entanglement—to perform certain types of calculations much more efficiently than…
Read More » -
Introduction to Quantum Random Number Generation (QRNG)
Cryptographic systems rely on the unpredictability and randomness of numbers to secure data. In cryptography, the strength of encryption keys depends on their unpredictability. Unpredictable and truly random numbers—those that remain secure even against extensive computational resources and are completely unknown to adversaries—are among the most essential elements in cryptography…
Read More » -
Sign Today, Forge Tomorrow (STFT) or Trust Now, Forge Later (TNFL) Risk
Sign Today, Forge Tomorrow (STFT) or Trust Now, Forge Later (TNFL) is the digital‑signature equivalent of HNDL. Digital signatures underpin everything from software updates and firmware integrity to identity verification and supply‑chain provenance. Today’s signatures are based on RSA or ECDSA, which quantum computers will also break. When that happens,…
Read More » -
The CRQC Quantum Capability Framework
This guide is a detailed, end‑to‑end map for understanding what it will actually take to reach a cryptographically relevant quantum computer (CRQC), i.e. break RSA-2048 - not just headline qubit counts. A CRQC must meet two conditions: the algorithmic requirements of the target attack and the hardware capabilities needed to…
Read More » -
The Challenge of IT and OT Asset Discovery
Every CISO understands the simple truth: you can’t protect what you don’t know you have. A comprehensive inventory of IT and OT assets - from servers and laptops to industrial controllers and IoT sensors - is the foundation of effective cybersecurity. In theory, building this asset inventory sounds straightforward. In…
Read More » -
Brassard–Høyer–Tapp (BHT) Quantum Collision Algorithm and Post-Quantum Security
The Brassard–Høyer–Tapp (BHT) algorithm is a quantum algorithm discovered in 1997 that finds collisions in hash functions faster than classical methods. In cryptography, a collision means finding two different inputs that produce the same hash output, undermining the hash’s collision resistance. The BHT algorithm theoretically reduces the time complexity of…
Read More » -
Capability D.3: Continuous Operation (Long-Duration Stability)
One of the most critical requirements for a cryptographically relevant quantum computer (CRQC) is continuous operation - the ability to run a complex quantum algorithm non-stop for an extended period (on the order of days) without losing quantum coherence or needing a reset. In practical terms, the entire quantum computing…
Read More »