Post-Quantum, PQC, Quantum Security
PostQuantum.com – Industry news and blog on Quantum Computing, Quantum Security, PQC, Post-Quantum, AI Security
-
How ECC Became the Easiest Quantum Target
Elliptic curve cryptography (ECC) will likely fall to quantum computers before RSA does - a cruel irony, since ECC's smaller keys were considered an advantage. Shor's algorithm needs roughly 2,330 logical qubits and 126 billion Toffoli gates to break P-256 ECDSA, versus approximately 1,409 logical qubits but 6.5 billion Toffoli…
Read More » -
Securing Quantum Computers – Threat at the Quantum-Classical Interface
A global race is on to build cryptographically relevant quantum computers (CRQCs) - machines powerful enough to break current encryption. Governments and industry are pouring billions into quantum R&D, and intelligence analysts scrutinize whether a geopolitical rival might secretly be ahead. Yet amid this focus on who builds a quantum…
Read More » -
Q-Day Isn’t an Outage – It’s a Confidence Crisis
Cybersecurity lore often paints Q-Day (the moment a quantum computer cracks RSA/ECC encryption) as an instant "Quantum Apocalypse" where every system gets hacked immediately. Planes falling from the sky, banks drained in seconds, an overnight digital Armageddon - if that nightmare doesn’t happen, some assume Q-Day wasn’t so bad after…
Read More » -
Post-Quantum Negligence: Legal Risks of Failing to Prepare for the Quantum Threat
Quantum computing is no longer a far-off hypothesis - it’s a rapidly emerging reality that could render today’s encryption obsolete. For CISOs and their boards, this means a new kind of cybersecurity crisis is on the horizon. Sensitive data that is safely encrypted now may be sitting like a ticking…
Read More » -
Sovereignty in the PQC Era: Standards, Trust, and Crypto-Agility
Post-Quantum Cryptography (PQC) is entering the standards stage, with the U.S. National Institute of Standards and Technology (NIST) recently selecting the first quantum-resistant algorithms. However, the future of PQC will not be as straightforward as simply adopting NIST’s choices globally. A strong push for digital sovereignty is emerging around the…
Read More » -
Trust Now, Forge Later (TNFL) – The Overlooked Quantum Threat
What is "Trust Now, Forge Later" (TNFL)? Most discussions about quantum computing threats focus on “Harvest Now, Decrypt Later” (HNDL) - the idea that adversaries can collect encrypted data today and store it, hoping a future quantum computer will break the encryption and expose sensitive information. This risk is very…
Read More » -
Quantum Readiness Is Not (Just) a Vendor Problem
In the recent IBM's “Secure the Post-Quantum Future” report 62% of executives admitted that their organization is waiting for vendors to make them quantum‑safe. In other words, they expect cloud providers, network equipment makers and software vendors to embed post‑quantum cryptography (PQC) so that internal teams can simply apply updates.…
Read More » -
Getting Started With Quantum Security and PQC Migration
Your complete roadmap to quantum-proofing your organization — from boardroom mandate to operational crypto-agility. This practitioner-curated Deep Dive series collects the PostQuantum.com articles you need to launch and run a quantum-readiness program, organized along the lifecycle most teams actually follow: securing executive buy-in and budget, performing cryptographic discovery and inventory,…
Read More » -
Quantum-Readiness / PQC Full Program Description (Telecom Example)
Preparing a large telecom (or any enterprise) for the post-quantum cryptography era is a massive, multi-faceted undertaking, but it is achievable with foresight, resources, and commitment. We’ve seen that it involves much more than just installing new algorithms - it’s about transforming an organization’s approach to cryptography across potentially thousands…
Read More » -
Forget Q-Day Predictions – Regulators, Insurers, Investors, Clients Are Your New Quantum Clock
Whether you personally believe Q-Day will come in 5 years or 50, the world around you isn’t taking chances - and neither can you. As a CISO, you’re now being implicitly (and sometimes explicitly) told by every corner of your ecosystem that quantum preparedness is mandatory. Regulators demand it via…
Read More » -
Stop Asking What Number a Quantum Computer Factored. Ask These Five Questions Instead
One of the laziest talking points in quantum security is that quantum computing has “gone nowhere” because people still talk about factoring 15. That confuses an early proof-of-concept with the real engineering path to a cryptographically relevant quantum computer. The 2001 Nature experiment explicitly described factoring 15 as the “simplest…
Read More » -
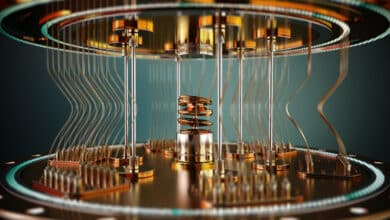
Device-Independent QKD (DI-QKD)
Modern quantum key distribution (QKD) has always carried a slightly uncomfortable subtext: the math may be information-theoretic, but the box on the rack is engineered. And engineered systems fail in messy, non-theoretical ways. That gap - between "provably secure on paper" and "secure in a live network with real detectors,…
Read More » -
Marin’s Law on Crypto-Agility: Adaptability Determines Survivability
Thesis: Migration time to safer cryptography is inversely proportional to an organization’s crypto-agility. Formally: Let A denote an organization’s crypto-agility (0 ≤ A ≤ 1) and Y the wall-clock time required to replace a cryptographic primitive across all in-scope systems. Then Y ≈ K ⁄ A for some complexity constant…
Read More » -
Why “They’ve Only Factored 15” Is the Wrong Way to Judge Quantum Computing
Early Shor demos were proofs of control, not the real scoreboard. The path to a cryptographically relevant quantum computer runs through error correction, logical qubits, and fault tolerance - not through a neat sequence of ever-larger classroom factorizations. One of the most persistent anti-quantum talking points goes like this: “After…
Read More » -
How You, Too, Can Predict Q-Day (Without the Hype)
For three decades, Q-Day has been “just a few years away.” I want to show you how to make your own informed prediction on when Q-Day will arrive. Counting physical qubits by itself is misleading. To break RSA you need error‑corrected logical qubits, long and reliable operation depth, and enough…
Read More »