Quantum Security & PQC
Post-quantum cryptography, PQC migration, crypto-agility, cryptographic inventory, CBOM, and practical quantum readiness — from executive mandate to operational deployment.
-
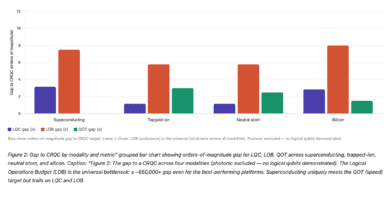
The CRQC Scorecard: How Close Is Each Quantum Modality to Breaking Your Encryption?
Yesterday, two papers landed that set social media on fire. Google Quantum AI published a landmark resource estimate showing that fewer than 500,000 superconducting qubits could break Bitcoin's elliptic curve cryptography in under nine minutes. Hours later, a team from…
Read More » -
No One Has Secretly Broken RSA-2048 or RSA-4096 — Here’s the Science
If someone tells you RSA-2048 or even RSA-4096 has been secretly cracked, they are either lying to you or have been lied to. There is no third option that is consistent with physics, engineering, the observable behavior of governments and…
Read More » -
Bitcoin’s Quantum Timeline Is Not RSA’s Quantum Timeline
Most quantum-risk-to-Bitcoin analyses rehash RSA-2048 timelines. They're missing the point. Bitcoin doesn't use RSA. It uses 256-bit ECC - and Shor's algorithm will break that first. Scan the quantum computing coverage of Bitcoin and you will find a remarkable pattern.…
Read More » -
Q-FUD: The Quantum Panic Industry
Cybersecurity has always had a FUD problem. “FUD” (fear, uncertainty, and doubt) is the oldest trick in enterprise security marketing: paint a worst-case scenario, imply you’re already compromised, sprinkle in enough jargon to make the buyer feel outgunned, and then…
Read More » -
Pinnacle Architecture: 100,000 Qubits to Break RSA-2048, but at What Cost?
Iceberg Quantum's Pinnacle Architecture paper claims RSA-2048 can be factored with fewer than 100,000 physical qubits - a genuine 10× reduction over the previous state of the art - by replacing surface codes with quantum LDPC codes. The result is…
Read More » -
Payments and the Race to Quantum Safety / Post-Quantum Cryptography (PQC)
The payments industry has navigated big cryptographic transitions before. The migration from magnetic stripes to EMV chips took the better part of two decades and cost billions. The shift from SHA-1 to SHA-256 certificates was painful but bounded - it…
Read More » -
120,000 Tasks: Why Post‑Quantum (PQC) Migration Is Enormous
When I tell fellow CISOs, board members, or even seasoned program managers that the integrated program plan for a comprehensive quantum security / post-quantum cryptography (PQC) migration I recently worked on contained over 120,000 discrete tasks, the reaction is almost…
Read More » -
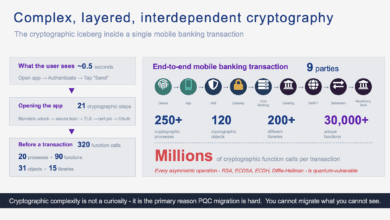
The Cryptographic Iceberg Inside a Mobile Banking Transaction
A single mobile banking payment triggers millions of cryptographic function calls across nine parties. Here's what actually happens - from silicon to settlement - and why it matters for quantum readiness. The Cryptographic Iceberg Inside a Mobile Banking Transaction 320…
Read More » -
NIS2, DORA, and the EU Post-Quantum Roadmap
If you are a CISO under NIS2 or DORA, you are already expected to run a risk-management system that tracks material, evolving threats - and to implement “state‑of‑the‑art” controls appropriate to the risk. The EU’s PQC roadmap is effectively saying: quantum…
Read More » -
The Complete US Post-Quantum Cryptography (PQC) Regulatory Framework in 2026
Three pillars anchor the US PQC framework: the Quantum Computing Cybersecurity Preparedness Act (federal law that no executive order can undo), NSM-10's 2035 migration target (still in force), and NIST's finalized FIPS standards (published August 2024). The Trump administration's June…
Read More » -
No Single Law, No Single Excuse: How Canada Regulates PQC Without Saying “Quantum”
Canada's visible PQC guidance - three documents published mid-2025 - is just the tip. Beneath it sits a layered enforcement framework spanning financial regulation, critical infrastructure law, privacy obligations, and securities disclosure that collectively creates binding pressure for quantum readiness.…
Read More » -
Telecom Quantum Readiness: Why the Urgency and Where to Start
An increasing number of telecom leaders have been pinging me lately about quantum readiness. And frankly, that’s exactly what they should be doing. New regulations and mandates are emerging left and right (in various jurisdictions and across the industry) requiring…
Read More » -
Quantum Key Distribution (QKD): Why Countries Differ on Its Future
Quantum Key Distribution (QKD) - a method of securing communications using quantum physics - has become a flashpoint of debate worldwide. Recent news (like Google’s announcement favoring post-quantum algorithms over QKD) highlights how divided opinions are. Some nations are investing…
Read More » -
Rethinking CBOM
The simplest way to explain CBOM is still the best. If SBOM is the ingredients list for software, CBOM is the ingredients list for the security assumptions that software depends on. Where SBOM tracks components and dependencies, CBOM tracks cryptographic…
Read More » -
Why We Need a Quantum Security ISAC
Quantum computing promises revolutionary capabilities, but it also poses unprecedented threats to cybersecurity. Experts warn of a looming “Quantum Apocalypse” scenario - the day when a sufficiently advanced quantum computer can crack encryption like RSA or ECC, exposing sensitive data…
Read More »