Table of Contents
Introduction
Ask anyone in quantum computing when Q-Day will arrive — the day a quantum computer first breaks the public-key cryptography that underpins digital trust — and you’ll get an answer. You’ll also get a different answer from the next person you ask. And the person after that.
Expert predictions for Q-Day range from “already happened in a classified lab” to “never, the engineering challenges are insurmountable.” Survey data consistently shows a wide spread, with median estimates clustering somewhere between 2030 and 2040, but with long tails in both directions. The honest truth is that nobody knows — and the reasons nobody knows are structural, not just a matter of insufficient data.
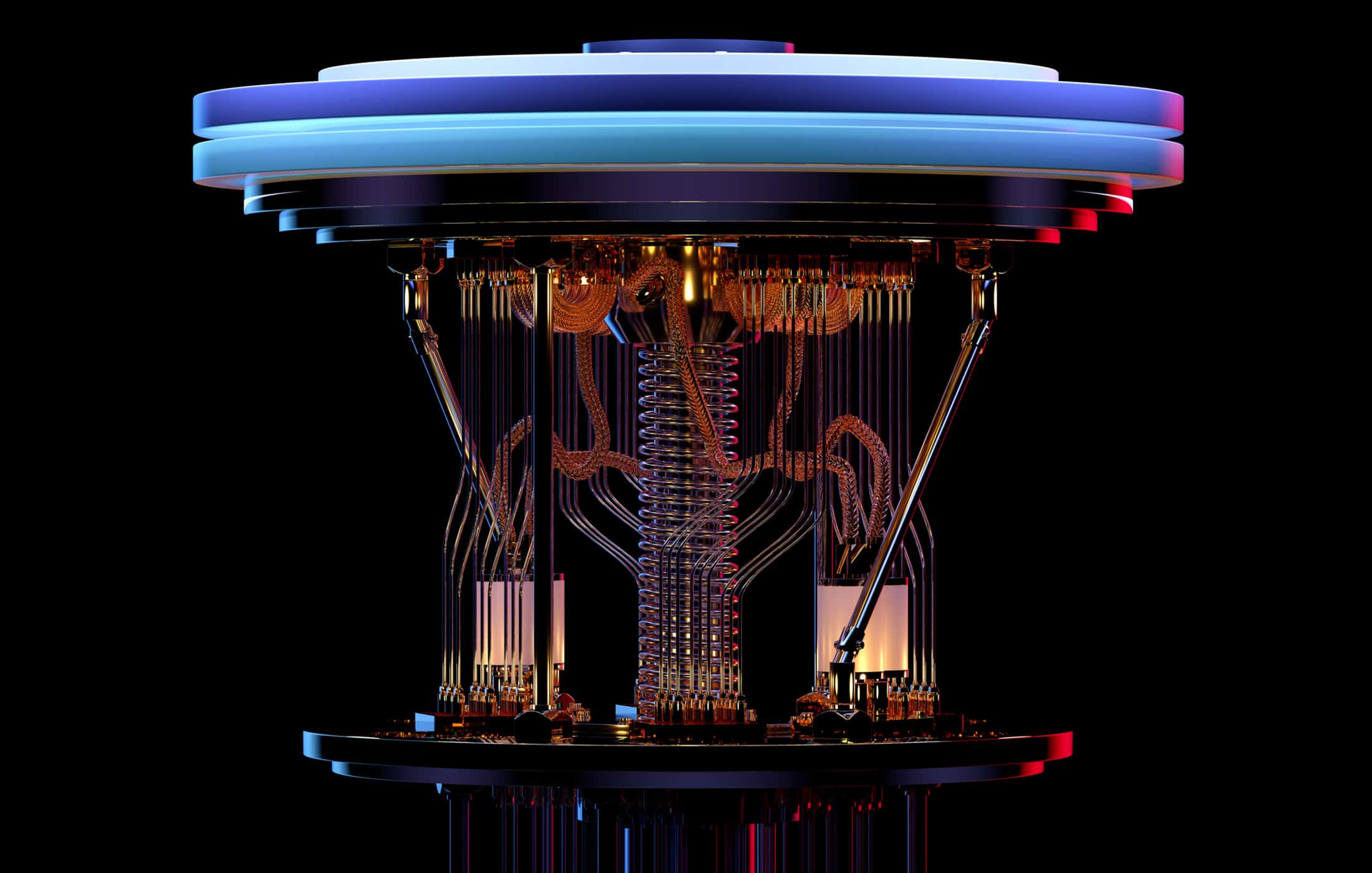
Q-Day prediction is hard because it depends on simultaneous breakthroughs across multiple domains: qubit quality and quantity, error correction overhead, algorithmic efficiency, control systems engineering, and classical computing infrastructure to support real-time decoding. Progress in any one domain can be rapid and surprising — as Google’s Willow chip and recent algorithmic improvements from Gidney have demonstrated — but progress must converge across all of them before a cryptographically relevant quantum computer (CRQC) becomes operational.
This makes Q-Day prediction fundamentally different from, say, predicting when a chip will reach a certain transistor count. It is more like predicting when multiple independent technologies will simultaneously mature enough to enable a system-level capability that none of them can deliver alone. History suggests we are bad at this kind of prediction — and that surprises tend to come faster than the consensus expects.
Yet the question matters enormously. Whether Q-Day arrives in 2030, 2035, or 2045 determines how much runway organizations have to complete their post-quantum cryptography (PQC) migrations — multi-year, multi-hundred-million-dollar programs that cannot be compressed into a panic sprint. And the question is already shaping policy: governments have set hard regulatory deadlines, insurers are adjusting underwriting criteria, and sophisticated adversaries are harvesting encrypted data today in anticipation of future decryption.
This Deep Dive series is my attempt to bring rigor, structure, and intellectual honesty to a topic that generates more heat than light. It covers three layers: what Q-Day actually is and why it matters, how to think about predicting it (and why most predictions fail), and why — paradoxically — the exact date may matter less than you think.
Part I — What is Q-Day and why does it matter?
Foundations: defining the event, sizing the impact, and separating signal from noise.
What Is Q-Day (Y2Q)?
This foundational article defines Q-Day (also known as Y2Q) — the point at which a quantum computer can break the RSA and ECC cryptographic algorithms that currently protect virtually all digital communications, transactions, and identity systems. It explains the underlying threat in plain language: what Shor’s algorithm does, why public-key cryptography is uniquely vulnerable, what “cryptographically relevant” actually means in practice, and why Q-Day is not a single dramatic event but a threshold that, once crossed, changes the security assumptions for everything built on top of classical cryptography.
Q-Day (Y2Q) vs. Y2K
The Y2K parallel is tempting — and misleading. This article dissects the comparison: where it holds (both require massive, coordinated infrastructure upgrades under time pressure), where it breaks down (Y2K had a fixed, known deadline; Q-Day does not), and what lessons from the Y2K experience actually apply to quantum readiness. The key insight is that Y2K’s relative success was the result of years of unglamorous preparation, not proof that the threat was overhyped — a distinction that matters enormously for how organizations should think about PQC migration timelines.
Q-Day Isn’t an Outage — It’s a Confidence Crisis
The Hollywood version of Q-Day imagines an instant “quantum apocalypse” — planes falling from the sky, banks drained overnight. This article argues that the real impact will be very different and in some ways more dangerous: an overnight collapse of confidence in digital trust systems. The first credible RSA/ECC break will trigger panic, emergency audits, regulatory pressure, frantic repricing of digital risk, and a flight to “quantum-safe” brands — even if the initial quantum capability is expensive, slow, and limited to crown-jewel targets. Q-Day is a confidence crisis, not an outage, and preparing for it requires understanding the second-order effects as much as the technical threat.
What Will Really Happen Once Q-Day Arrives — When Our Current Cryptography Is Broken?
Where the confidence crisis article frames the dynamics, this piece provides the scenario analysis: a detailed walk-through of what Q-Day looks like across sectors — finance, government, critical infrastructure, communications, and consumer technology. It examines the cascade of consequences: which systems are most immediately exposed, how adversaries will exploit the window between first break and widespread migration, what governments will likely do (and fail to do) in the initial response, and how long the transition to quantum-safe operations will actually take once the trigger is pulled.
Q-FUD: The Quantum Panic Industry
Not everyone talking about Q-Day is acting in good faith. This article examines the “quantum panic industry” — vendors, consultants, and commentators who inflate the quantum threat to sell products, generate clicks, or secure funding. It distinguishes legitimate urgency (the threat is real; the timeline is uncertain; preparation takes years) from Q-FUD: exaggerated claims, misleading timelines, and scare tactics that ultimately undermine the credibility of the quantum security field and make it harder for CISOs to build rational, funded programs. It’s a call for intellectual honesty in a space that badly needs it.
Part II — Predicting Q-Day: frameworks and forecasts
The methodology: why most predictions fail, how to think about it rigorously, and what the data actually says.
How You, Too, Can Predict Q-Day (Without the Hype)
This article is a methodology guide: it breaks down the key variables that determine when a CRQC becomes feasible — logical qubit requirements, error correction overhead, algorithmic improvements, hardware roadmaps, and engineering integration — and shows how to reason about their interaction without resorting to either blind optimism or dismissive skepticism. It’s designed to give CISOs, policymakers, and technology leaders the intellectual framework to evaluate Q-Day claims for themselves rather than relying on vendor predictions or expert surveys.
CRQC Readiness Benchmark — Benchmarking Quantum Computers on the Path to Breaking Cryptography
This is the core methodological contribution: a purpose-built benchmark for tracking how close quantum computers are to breaking cryptography, based on three metrics that together capture the key requirements for a CRQC. Logical Qubit Capacity (LQC) measures how many error-corrected logical qubits a system can sustain. Logical Operations Budget (LOB) measures how many sequential logical operations can be performed before errors accumulate beyond correction. Quantum Operations Throughput (QOT) measures the speed at which logical operations execute, determining whether a computation that is theoretically possible can complete in a practical timeframe. The article explains why existing benchmarks (quantum volume, algorithmic qubits, random circuit sampling) are inadequate for assessing CRQC readiness, derives the three metrics from first principles, and applies them to current hardware to estimate where we stand today.
The Trouble with Quantum Computing and Q-Day Predictions
This article examines why Q-Day predictions are systematically unreliable: the incentive structures that bias expert surveys (optimism for funding, pessimism for caution), the difficulty of predicting convergent multi-domain breakthroughs, the role of classified research in creating asymmetric information, and the historical track record of technology predictions in analogous domains. It’s not an argument that prediction is impossible — it’s an argument that consumers of predictions need to understand the structural biases and use frameworks (like the CRQC Readiness Benchmark) rather than point estimates.
Q-Day Predictions: Anticipating the Arrival of CRQC
This companion article provides a comprehensive, regularly updated survey of Q-Day predictions from across the industry, government, and research community — including timelines from NIST, NSA, European agencies, major quantum computing companies, independent researchers, and expert polls. It catalogues the predictions, notes their methodological basis (or lack thereof), and maps them against the CRQC Readiness Benchmark framework to assess how credible each estimate is given current hardware trajectories and algorithmic progress.
Q-Day Revisited — RSA-2048 Broken by 2030: Detailed Analysis
This long-form analysis takes the most aggressive credible timeline — RSA-2048 broken by 2030 — and stress-tests it against the current state of quantum hardware, error correction research, and algorithmic developments (including Gidney’s 2025 resource estimates). It examines what would need to go right simultaneously across multiple fronts for this timeline to hold, assesses the probability of each required breakthrough, and arrives at a calibrated view of whether 2030 is plausible, possible-but-unlikely, or effectively ruled out by current physics and engineering constraints.
Part III — The clock is already ticking
Why the exact date may matter less than you think — and what’s already forcing your hand.
Forget Q-Day Predictions — Regulators, Insurers, Investors, Clients Are Your New Quantum Clock
This is the pivot article — the piece that reframes the entire Q-Day conversation. It argues that debating whether Q-Day arrives in 2030 or 2040 is increasingly beside the point, because external pressures have already set hard deadlines that are closer and more certain than any quantum timeline: 2030–2035 regulatory deadlines for PQC migration, procurement and contract requirements from major clients and government agencies, cyber-insurance underwriting criteria that penalize quantum unpreparedness, and investor and board expectations driven by fiduciary duty. The real clock is not quantum — it’s regulatory, commercial, and legal. And it’s already ticking.
Where this series connects to other Deep Dives
The Q-Day question does not exist in isolation. It connects directly to several other Deep Dive series on PostQuantum.com:
- CRQC Quantum Capability Framework — The CRQC Readiness Benchmark used in this series distills three key metrics from the broader CRQC Capability Framework, which maps the full spectrum of capabilities — across hardware, software, systems integration, and operational readiness — required to actually build a cryptographically relevant quantum computer. That framework has its own Deep Dive.
- Getting Started With Quantum Security & PQC Migration — If Q-Day tells you why to act, the Getting Started series tells you how: a practitioner’s roadmap for launching and running a quantum-readiness program, end to end.
This series examines technology and risk dynamics. It does not constitute financial, legal, or investment advice.
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.