Q-Day
PostQuantum.com – Industry news and blog on Quantum Computing, Quantum Security, PQC, Post-Quantum, Q-Day, Y2Q
-
Q-FUD: The Quantum Panic Industry
Cybersecurity has always had a FUD problem. “FUD” (fear, uncertainty, and doubt) is the oldest trick in enterprise security marketing: paint a worst-case scenario, imply you’re already compromised, sprinkle in enough jargon to make the buyer feel outgunned, and then offer the “only” solution - conveniently available this quarter. Q‑FUD…
Read More » -
Q-Day Isn’t an Outage – It’s a Confidence Crisis
Cybersecurity lore often paints Q-Day (the moment a quantum computer cracks RSA/ECC encryption) as an instant "Quantum Apocalypse" where every system gets hacked immediately. Planes falling from the sky, banks drained in seconds, an overnight digital Armageddon - if that nightmare doesn’t happen, some assume Q-Day wasn’t so bad after…
Read More » -
Forget Q-Day Predictions – Regulators, Insurers, Investors, Clients Are Your New Quantum Clock
Whether you personally believe Q-Day will come in 5 years or 50, the world around you isn’t taking chances - and neither can you. As a CISO, you’re now being implicitly (and sometimes explicitly) told by every corner of your ecosystem that quantum preparedness is mandatory. Regulators demand it via…
Read More » -
How You, Too, Can Predict Q-Day (Without the Hype)
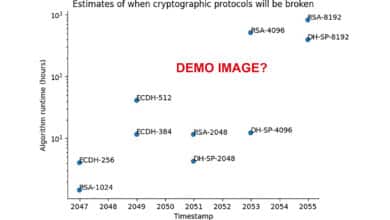
For three decades, Q-Day has been “just a few years away.” I want to show you how to make your own informed prediction on when Q-Day will arrive. Counting physical qubits by itself is misleading. To break RSA you need error‑corrected logical qubits, long and reliable operation depth, and enough…
Read More » -
CRQC Readiness Benchmark vs. Quantum Threat Tracker (QTT)
I will try and compare my proposed CRQC Readiness Benchmark with QTT, highlighting fundamental differences in methodology, assumptions, and philosophy, all in an effort to clarify how each approach informs our understanding of the looming “Q-Day.” The goal is to articulate why my benchmark and QTT produce different outlooks (2030s…
Read More » -
The Trouble with Quantum Computing and Q-Day Predictions
The trouble with quantum computing predictions so far has been that too many have been more speculation than science, more influenced by bias than by balanced analysis. We have the tools and knowledge to do better. By embracing a data-driven, scenario-based approach, we can turn timeline forecasting from a source…
Read More » -
Quantum Threat Tracker (QTT) Review Praising the Tool Questioning the Demo
The Quantum Threat Tracker (QTT) is a newly released open-source tool by Cambridge Consultants and the University of Edinburgh that aims to forecast when quantum computers will break today’s encryption. It combines quantum resource estimation (using optimized variants of Shor’s algorithm) with hardware development roadmaps to predict when cryptographic protocols…
Read More » -
CRQC Readiness Benchmark – Benchmarking Quantum Computers on the Path to Breaking Cryptography
Benchmarking quantum capabilities for cryptography is both critical and challenging. We can’t rely on any single metric like qubit count to tell us how near we are to breaking RSA-2048. A combination of logical qubit count, error-corrected circuit depth, and operational speed must reach certain thresholds in unison. Existing benchmarks…
Read More » -
Q-Day Revisited – RSA-2048 Broken by 2030: Detailed Analysis
It’s time to mark a controversial date on the calendar: 2030 is the year RSA-2048 will be broken by a quantum computer. That’s my bold prediction, and I don’t make it lightly. In cybersecurity circles, the countdown to “Q-Day” or Y2Q (the day a cryptographically relevant quantum computer cracks our…
Read More » -
What Is Q-Day (Y2Q)?
Q-Day, sometimes called “Y2Q” or the “Quantum Apocalypse”, refers to the future moment when a quantum computer becomes powerful enough to break modern encryption algorithms. In other words, it’s the day a cryptographically relevant quantum computer (CRQC) can crack the public-key cryptography (like RSA or ECC) that underpins our digital…
Read More » -
The Enormous Energy Cost of Breaking RSA‑2048 with Quantum Computers
The energy requirements for breaking RSA-2048 with a quantum computer underscore how different the post-quantum threat is from conventional hacking. It’s not just about qubits and math; it’s about megawatts, cooling systems, and power grids. Today, that reality means only the most potent actors would even contemplate such attacks, and…
Read More » -
Breaking RSA Encryption: Quantum Hype Meets Reality (2022-2025)
To put it plainly, if you encrypted a message with an RSA-2048 public key today, no one on Earth knows how to factor it with currently available technology, even if they threw every quantum computer and supercomputer we have at the task. That may change in the future – perhaps…
Read More » -
Post-Quantum Cryptography (PQC) Standardization – 2025 Update
Post-quantum cryptography (PQC) is here - not in theory, but in practice. We have concrete algorithms, with standards guiding their implementation. They will replace our decades-old cryptographic infrastructure piece by piece over the next decade. For tech professionals, now is the time to get comfortable with lattices and new key…
Read More » -
NIST PQC Security Strength Categories (1–5) Explained
As part of its post-quantum cryptography (PQC) standardization, NIST introduced five security strength categories (often labeled Levels 1-5) to classify the robustness of candidate algorithms. Each category represents a minimum security level that a PQC algorithm’s cryptanalysis should require, defined by comparison to a well-understood "reference" problem in classical cryptography.…
Read More » -
Capability E.1: Engineering Scale & Manufacturability
Building a cryptography-breaking quantum computer (often dubbed Q-Day) will demand far more than just better algorithms or a few more qubits. It requires a massive scale-up in engineering - reaching hundreds of thousands or even millions of physical qubits - and doing so in a practical, manufacturable way. Engineering Scale…
Read More »