Q-Day & CRQC
Predicting when quantum computers will break cryptography: Q-Day timelines, the CRQC Readiness Benchmark, the CRQC Capability Framework, expert forecasts, and the regulatory deadlines that may matter more than the quantum timeline itself.
-
Post-Quantum Cryptography (PQC) Standardization – 2025 Update
Post-quantum cryptography (PQC) is here - not in theory, but in practice. We have concrete algorithms, with standards guiding their implementation. They will replace our decades-old cryptographic infrastructure piece by piece over the next decade. For tech professionals, now is…
Read More » -
NIST PQC Security Strength Categories (1–5) Explained
As part of its post-quantum cryptography (PQC) standardization, NIST introduced five security strength categories (often labeled Levels 1-5) to classify the robustness of candidate algorithms. Each category represents a minimum security level that a PQC algorithm’s cryptanalysis should require, defined…
Read More » -
Capability E.1: Engineering Scale & Manufacturability
Building a cryptography-breaking quantum computer (often dubbed Q-Day) will demand far more than just better algorithms or a few more qubits. It requires a massive scale-up in engineering - reaching hundreds of thousands or even millions of physical qubits -…
Read More » -
Capability B.4: Qubit Connectivity & Routing Efficiency
Qubit connectivity refers to which qubits can interact directly (perform two-qubit gates) with each other. This is often visualized as a connectivity graph: each node is a qubit, and an edge between two nodes means those qubits can be coupled…
Read More » -
4,099 Qubits: The Myth and Reality of Breaking RSA-2048 with Quantum Computers
4,099 is the widely cited number of quantum bits one would need to factor a 2048-bit RSA key using Shor’s algorithm – in other words, the notional threshold at which a quantum computer could crack one of today’s most common…
Read More » -
What Will Really Happen Once Q-Day Arrives – When Our Current Cryptography Is Broken?
As the world edges closer to the era of powerful quantum computers, experts warn of an approaching “Q-Day” (sometimes called Y2Q or the Quantum Apocalypse): the day a cryptographically relevant quantum computer can break our current encryption. Unlike the Y2K…
Read More » -
Q-Day Predictions: Anticipating the Arrival of CRQC
While CRQCs capable of breaking current public key encryption algorithms have not yet materialized, technological advancements are pushing us towards what is ominously dubbed 'Q-Day'—the day a CRQC becomes operational. Many experts believe that Q-Day, or Y2Q as it's sometimes…
Read More » -
Harvest Now, Decrypt Later (HNDL) Risk
"Harvest Now, Decrypt Later" (HNDL), also known as "Store Now, Decrypt Later" (SNDL), is a concerning risk where adversaries collect encrypted data with the intent to decrypt it once quantum computing becomes capable of breaking current encryption methods. This is…
Read More » -
Cryptographically Relevant Quantum Computers (CRQCs)
Cryptographically Relevant Quantum Computers (CRQCs) represent a seismic shift on the horizon of cybersecurity. In this article, we’ve seen that CRQCs are defined by their ability to execute quantum algorithms (like Shor’s and Grover’s) at a scale that breaks the…
Read More » -
Neven’s Law: The Doubly Exponential Surge of Quantum Computing
In 2019, Google’s Quantum AI director Hartmut Neven noticed something remarkable: within a matter of months, the computing muscle of Google’s best quantum processors leapt so quickly that classical machines struggled to keep up. This observation gave birth to “Neven’s…
Read More » -
CRQC Readiness Index Proposal
This proposal outlines a composite, vendor‑neutral “CRQC Readiness” indicator. It intentionally avoids one‑number vanity metrics (like only counting qubits) and instead triangulates from three ingredients that actually matter for breaking today’s crypto: usable (logical) qubits, error‑tolerant algorithm depth, and sustained…
Read More » -
Understanding FIPS 140: A Cornerstone of Cryptographic Security
FIPS 140 (Federal Information Processing Standard 140) is a U.S. government computer security standard that specifies security requirements for cryptographic modules - the hardware or software components that perform encryption and other cryptographic functions. In simpler terms, FIPS 140 sets…
Read More » -
Q-Day (Y2Q) vs. Y2K
In the late 1990s, organizations worldwide poured time and money into exorcising the “millennium bug.” Y2K remediation was a global scramble. That massive effort succeeded: when January 1, 2000 hit, planes didn’t fall from the sky and power grids stayed…
Read More » -
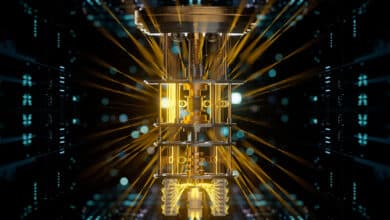
What’s the Deal with Quantum Computing: Simple Introduction
Quantum computing holds the potential to revolutionize fields where classical computers struggle, particularly in areas involving complex quantum systems, large-scale optimization, and cryptography. The power of quantum computing lies in its ability to leverage the principles of quantum mechanics—superposition and…
Read More » -
The CRQC Quantum Capability Framework
This guide is a detailed, end‑to‑end map for understanding what it will actually take to reach a cryptographically relevant quantum computer (CRQC), i.e. break RSA-2048 - not just headline qubit counts. A CRQC must meet two conditions: the algorithmic requirements…
Read More »