All Post-Quantum, PQC Posts
-
Post-Quantum, PQC, Quantum Security
Quantum Readiness: What Crypto Exchanges Should Do Today
Preparing for quantum computing is a grand challenge, but it’s one that crypto exchanges can tackle step by step. By addressing off-chain vulnerabilities, fortifying custodial key management, and staying vigilant on-chain, exchanges can dramatically reduce the risk of being caught off-guard by a quantum breakthrough. The goal is not to panic, but to plan pragmatically. As one strategy guide noted, even if you can’t fix…
Read More » -
Post-Quantum, PQC, Quantum Security
Physics at the Heart of the New Cold War
In the 21st century, cutting-edge physics has moved from the laboratory into the realm of high geopolitics. Breakthroughs in quantum computing, advanced materials, and energy aren’t just academic - they are strategic assets coveted by nations. The situation echoes the mid-20th century, when projects like the Manhattan Project turned abstract physics into world-altering power. Today, governments are pouring billions into quantum technology and other physics-driven…
Read More » -
Post-Quantum, PQC, Quantum Security
Hybrid Cryptography for the Post-Quantum Era
By combining classical and post-quantum cryptographic primitives in tandem, hybrid schemes provide defense-in-depth during this transition period. In practice, a hybrid approach might mean performing both a traditional elliptic-curve key exchange and a post-quantum key exchange inside the same protocol, or signing a document with both an ECDSA signature and a Dilithium (post-quantum) signature. The result is that an attacker would need to break all…
Read More » -
Post-Quantum, PQC, Quantum Security
Quantum Key Distribution (QKD) 101: A Guide for Cybersecurity Professionals
Quantum Key Distribution (QKD) is a cutting-edge security technology that leverages quantum physics to enable two parties to share secret encryption keys with unprecedented security guarantees. Unlike classical key exchange methods whose security rests on computational assumptions, QKD’s security is rooted in the laws of physics – any eavesdropping attempt will unavoidably disturb the quantum signals and reveal itself. With large-scale quantum computers on the…
Read More » -
Quantum Computing
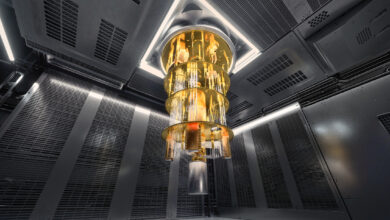
From NISQ to FTQC to FASQ
The dream of quantum computing is inching closer to reality, but between our current noisy prototypes and tomorrow’s transformative machines lies a daunting gulf. In the language of the field, we are transitioning from the NISQ era into the realm of FTQC, with an eye on the ultimate prize dubbed FASQ. These acronyms - Noisy Intermediate-Scale Quantum, Fault-Tolerant Quantum Computing, and Fault-Tolerant Application-Scale Quantum -…
Read More » -
Quantum Computing
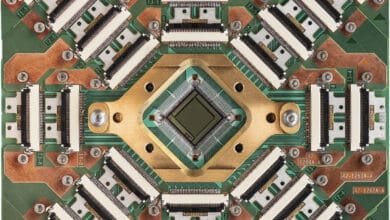
Adiabatic Quantum (AQC) and Cyber (2024 Update)
Adiabatic Quantum Computing (AQC) is an alternative paradigm that uses an analog process based on the quantum adiabatic theorem. Instead of discrete gate operations, AQC involves slowly evolving a quantum system’s Hamiltonian such that it remains in its lowest-energy (ground) state, effectively “computing” the solution as the system’s final state. AQC and its practical subset known as quantum annealing are particularly geared toward solving optimization…
Read More » -
Quantum Computing
Quantum Hacking: Cybersecurity of Quantum Systems
While these machines are not yet widespread, it is never too early to consider their cybersecurity. As quantum computing moves into cloud platforms and multi-user environments, attackers will undoubtedly seek ways to exploit them.
Read More » -
Post-Quantum, PQC, Quantum Security
Quantum Ethics: Why We Must Plan for a Responsible Quantum Future
New technologies bring not only breakthroughs but also new risks and dilemmas - and quantum computing is no exception. Quantum computers promise to solve problems beyond the reach of classical machines, from cracking complex optimization puzzles to simulating new drugs and materials. Yet experts warn that quantum’s “known unknowns” include serious ethical challenges arising from potential abuse, misuse, or unintended consequences. In other words, along…
Read More »