Cyber-Kinetic Security
PostQuantum.com – Industry news and blog on Quantum Computing, Quantum Security, PQC, Post-Quantum, AI Security, Cyber-Kinetic Security
-
OT Security in the Age of AI Exploits: What Anthropic’s Mythos Preview Means for Critical Infrastructure
On April 7, 2026, Anthropic disclosed Claude Mythos Preview, an AI model that autonomously discovers and exploits zero-day vulnerabilities in every major operating system and web browser. As I detailed in my analysis of the announcement, these capabilities represent a…
Read More » -
The Dual Risks of AI Autonomous Robots: Uncontrollable AI Meets Cyber-Kinetic Risks
The automotive industry has revolutionized manufacturing twice. The first time was in 1913 when Henry Ford introduced a moving assembly line at his Highland Park plant in Michigan. The innovation changed the production process forever, dramatically increasing efficiency, reducing the…
Read More » -
Digital Actions, Lethal Consequences: A Cyber-Kinetic Risk Primer
Our physical world is becoming more connected – which makes it more dependent on the cyber world. Many physical objects around us are no longer just physical, but extend into cyberspace, being remotely monitored and controlled. Consider the power plant…
Read More » -
Fortifying the Future: Cyber-Kinetic Risks in Kingdom of Saudi Arabia’s (KSA) Technological Zeitgeist
To fortify its cyber-kinetic defenses in line with growing digital transformation and infrastructural expansions, Saudi Arabia must adopt a multi-layered approach that encompasses regulation, technology, and human capital. To this end, the Kingdom has already embarked on a comprehensive strategy…
Read More » -
Cybersecurity Negligence and Personal Liability: What CISOs and Board Members Need to Know
“Could I personally be sued or fined if our company gets breached?” This uneasy question is crossing the minds of many CISOs and board members lately. High-profile cyber incidents and evolving regulations have made it clear that cybersecurity is not…
Read More » -
Saudi Arabia Vision 2030: Cybersecurity at the Core of Transformation
Last week, the Saudi Data and Artificial Intelligence Authority (SDAIA) launched a nationwide awareness campaign called “Ask Before”, intended to educate the public about the significance of personal data ahead of the implementation of a new national personal data protection system. Emphasizing…
Read More » -
Cybersecurity and Cryptographic Innovation in Canada
Canada has long punched above its weight in advanced technologies - from pioneering work in AI to early breakthroughs in quantum computing and blockchain. This innovative spirit extends to the domains of cybersecurity and cryptography, where Canadian researchers and companies…
Read More » -
Securing Society 5.0
A term first coined by the Japanese government, “Society 5.0” describes “A human-centered society that balances economic advancement with the resolution of social problems by a system that highly integrates cyberspace and physical space.” The fifth evolution of the society,…
Read More » -
Cybersecurity and Safety in the 5G-Enabled Smart-Everything World
Neil Harbisson calls himself a cyborg. Without the antenna implanted in his skull, he would not be able to see colour of any kind. Born with achromatopsia, a condition of total colourblindness that affects 1 in every 30 000 people,…
Read More » -
Opportunity and Cybersecurity in the Age of 5G
The human will to innovate is seemingly relentless. The history of our species is one of continual development, with the last 350 years, in particular, representing staggering technological progress. The first industrial revolution mechanized production using natural elements like water.…
Read More » -
IIoT and Trust and Convenience: A Potentially Deadly Combination
When microwave ovens first arrived on the market in 1967 they were met with public skepticism. Perhaps it was because, not long before, the same technology now promising to safely cook consumers’ evening meals was the backbone of a military…
Read More » -
5G Network: A Quantum Leap in Connectivity – and Cyber Threats
The timeline of human history is marked by inflection points of major technological advancement. The plow, the printing press, the telegraph, the steam engine, electricity, the telephone, the internet: each of these breakthroughs precipitated tectonic shifts in how people lived…
Read More » -
NFC Security 101 (Non-5G IoT Connectivity Options)
NFC is a short range two-way wireless communication technology that enables simple and secure communication between electronic devices embedded with NFC microchip. NFC technology operates in 13.56 megahertz and supports 106, 212, or 424 Kbps throughput. There are three available…
Read More » -
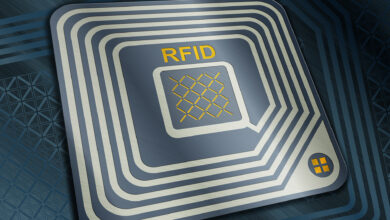
RFID Security 101 (Non-5G IoT Connectivity Options)
Radio-Frequency Identification (RFID) is a technology commonly used for identification, status administration and management of different objects. It is important for people identification, as it is commonly deployed in the latest biometric passports. It operates in several frequency bands like Low…
Read More » -
Wi-Fi Security 101 (Non-5G IoT Connectivity Options)
The Wi-Fi represents wireless technology that includes the IEEE 802.11 family of standards (IEEE 802.11a, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, IEEE 802.11ac, etc.). Within 50m range, it operates in 2.4 GHz and 5GHz frequency bands,. This technology was developed…
Read More »