Deep Dive Series
CRQC Quantum Capability Framework
A cryptographically relevant quantum computer will not emerge from a single breakthrough. It requires the simultaneous maturation of nine distinct capabilities — across error correction, logical gate operations, and end-to-end system execution — plus the engineering and manufacturing scale to build it for real. Progress in any one domain is necessary but not sufficient. The CRQC arrives when all nine converge.
This Deep Dive series maps those capabilities in detail, tracks where each stands today, and applies the framework to the questions that matter most: which hardware modality is closest, what would it actually cost to build and operate a CRQC, and can anyone afford to power one? The capability framework article is the comprehensive reference; the individual capability articles and the applied analyses below go deeper on each dimension.
-
Post-Quantum, PQC, Quantum Security
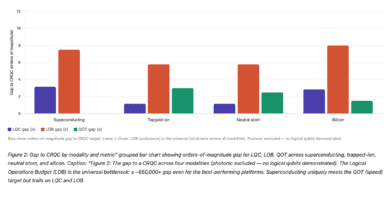
The CRQC Scorecard: How Close Is Each Quantum Modality to Breaking Your Encryption?
Yesterday, two papers landed that set social media on fire. Google Quantum AI published a landmark resource estimate showing that fewer than 500,000 superconducting qubits could break Bitcoin's elliptic curve cryptography in under nine minutes. Hours later, a team from Oratomic, Caltech, and UC Berkeley — including some of the most credible names in fault-tolerant quantum computing — dropped a paper claiming that Shor's algorithm…
Read More » -
Post-Quantum, PQC, Quantum Security
What It Will Actually Cost to Break RSA-2048: Energy, Hardware, People, and the Bill Nobody’s Talking About
Breaking one RSA-2048 key on a CRQC could cost $2–5 million when you add up energy, amortization, personnel, and facilities All three approaches share silicon's core advantages: compatibility with semiconductor industry infrastructure, small qubit footprint (~50 nm), and long coherence times enabled by isotopic purification of ²⁸Si. But they diverge sharply on how qubits are defined, controlled, and manufactured. Approach 1: Atomically Precise Donor Qubits…
Read More » -
Post-Quantum, PQC, Quantum Security
The Enormous Energy Cost of Breaking RSA‑2048 with Quantum Computers
The energy requirements for breaking RSA-2048 with a quantum computer underscore how different the post-quantum threat is from conventional hacking. It’s not just about qubits and math; it’s about megawatts, cooling systems, and power grids. Today, that reality means only the most potent actors would even contemplate such attacks, and even then only for the crown jewels of intelligence. Tomorrow, advances in both quantum engineering…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability E.1: Engineering Scale & Manufacturability
Building a cryptography-breaking quantum computer (often dubbed Q-Day) will demand far more than just better algorithms or a few more qubits. It requires a massive scale-up in engineering - reaching hundreds of thousands or even millions of physical qubits - and doing so in a practical, manufacturable way. Engineering Scale & Manufacturability (Capability E.1) is about bridging the gap between today’s laboratory prototypes and tomorrow’s…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability B.4: Qubit Connectivity & Routing Efficiency
Qubit connectivity refers to which qubits can interact directly (perform two-qubit gates) with each other. This is often visualized as a connectivity graph: each node is a qubit, and an edge between two nodes means those qubits can be coupled for a two-qubit gate. Some hardware has a dense graph (even complete or all-to-all connectivity), meaning any qubit can directly entangle with any other. Others…
Read More » -
Post-Quantum, PQC, Quantum Security
Cryptographically Relevant Quantum Computers (CRQCs)
Cryptographically Relevant Quantum Computers (CRQCs) represent a seismic shift on the horizon of cybersecurity. In this article, we’ve seen that CRQCs are defined by their ability to execute quantum algorithms (like Shor’s and Grover’s) at a scale that breaks the cryptographic primitives we rely on daily. While still likely years (if not a decade or more) away, their eventual arrival is not a question of…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability D.3: Continuous Operation (Long-Duration Stability)
One of the most critical requirements for a cryptographically relevant quantum computer (CRQC) is continuous operation - the ability to run a complex quantum algorithm non-stop for an extended period (on the order of days) without losing quantum coherence or needing a reset. In practical terms, the entire quantum computing stack - qubits, control electronics, error-correction processes, cooling systems - must sustain stable performance for…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability D.1: Full Fault-Tolerant Algorithm Integration
Imagine a quantum computer that can execute an entire algorithm start-to-finish with errors actively corrected throughout. Full fault-tolerant algorithm integration is exactly that: the orchestration of all components - stable logical qubits, high-fidelity gates, error-correction cycles, ancilla factories, measurements, and real-time feedback - to run a useful quantum algorithm reliably from beginning to end. This capability is essentially the “system integration” of quantum computing, bringing…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability D.2: Decoder Performance (Real‑Time Error Correction Processing)
In a fault-tolerant quantum computer, qubits are continuously monitored via stabilizer measurements (producing “syndrome” bits) to detect errors. The decoder is a classical algorithm (running on specialized hardware) that takes this rapid stream of syndrome data and figures out which qubits have experienced errors, so that corrections can be applied immediately. Achieving real-time decoding at scale is enormously challenging: a CRQC may need to handle…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability C.2: Magic State Production & Injection (Non-Clifford Gates)
Magic states are an essential “extra ingredient” for universal quantum computing, often metaphorically likened to a magic catalyst enabling otherwise impossible operations. Quantum algorithms require not only robust qubits and error correction, but also a way to perform non-Clifford gates - operations outside the easy Clifford group. These non-Clifford gates (like the T gate or controlled-controlled-Z) are the key to achieving universal quantum computation, yet…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability C.1: High-Fidelity Logical Clifford Gates
Cryptographically Relevant Quantum Computers (CRQCs) will rely on a suite of core capabilities - and high-fidelity logical Clifford gates are among the most essential. This capability refers to performing the fundamental set of quantum logic operations (the Clifford gates: Pauli X, Y, Z flips; the Hadamard (H); the phase gate (S); and the controlled-NOT (CNOT), among others) on logical qubits with speed and reliability. In…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability B.3: Below-Threshold Operation & Scaling
“Below-threshold operation” refers to running a quantum processor at error rates below the critical threshold of a quantum error-correcting code. In simple terms, there is a tipping point in error rates: if each quantum gate and qubit has an error probability lower than this threshold, adding more qubits and more error-correction actually reduces the overall error rate of the computation. If error rates are above…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability B.2: Syndrome Extraction (Error Syndrome Measurement)
Quantum syndrome extraction - also called error syndrome measurement - is the process of measuring collective properties of qubits to detect errors without destroying the encoded quantum information. It is essentially the sensor mechanism of a quantum error-correcting code, analogous to measuring parity checks in a classical error-correcting code. In a stabilizer code (the leading framework for quantum error correction, introduced by Gottesman in the…
Read More » -
Post-Quantum, PQC, Quantum Security
Capability B.1: Quantum Error Correction (QEC)
Quantum Error Correction (QEC) is the first and arguably most critical capability in the roadmap toward a cryptographically relevant quantum computer (CRQC). Without QEC, a large-scale quantum computer cannot reliably perform the billions of operations needed to break modern encryption - no matter how many qubits we build. In essence, QEC is what allows many noisy physical qubits to behave like a single near-perfect qubit.…
Read More »