My Articles, Opinions and Analyses
Quantum Machine Learning in 2026: A Real Frontier and an Honest Scorecard
A quantum computer naturally commands an exponentially large space, and machine learning is the art of taming such spaces. So why hasn't quantum AI delivered, and when will it? An evidence-first look at promise, hype, and timeline ...
The Quantum Random Number Generator (QRNG) Gold Rush
Everyone is selling quantum randomness. Most buyers can't tell the difference between genuine quantum entropy and a rebranded noise source with a quantum sticker on the box. This guide fixes that ...
Post-Quantum Deadlines Are Likely About to Compress. Here’s What I’m Seeing.
Governments spent 2025 publishing PQC roadmaps. In 2026, they started giving those roadmaps teeth. A draft US executive order, the EU's first binding PQC law, and vendor deadlines from Google and AWS are collapsing the compliance horizon from 2035 to 2028–2030 ...
Every Quantum Salary Guide I’ve Seen Is Fake. Here’s How I Proved It.
Recruitment agencies are flooding the market with "benchmarked" quantum salary data. I reverse-engineered the numbers in five different guides. Every single one was built from a formula, not from actual placement data ...
The Global PQC Migration Clock: Where Every Country Stands and Why the Gaps Between Them Matter More Than the Deadlines Themselves
Fifteen countries have now set PQC migration timelines. They all agree the migration must happen. They disagree on when, how, and with which algorithms. This capstone maps the convergence, the conflicts, and the compliance reality for organizations operating across borders ...
Quantum Radar Is Dead. The Physics Was Never There.
Fifteen years and over a hundred papers later, the verdict on quantum radar is in. The maximum range is limited to tens of meters by physics, not engineering. My earlier coverage was too generous ...
“They’ll Just Rent One”: The Quantum Threat Model Nobody Bothered to Check
Every article about quantum threats includes the throwaway line: criminals won't need their own quantum computer, they'll just rent one. The actual evidence says otherwise ...
PQC Governance: Who Should Lead Your Post-Quantum Migration, and How to Structure the Program
PQC migration is the most complex cryptographic transformation in enterprise history. Getting the governance model right determines whether it succeeds or stalls. Here's how to structure it ...
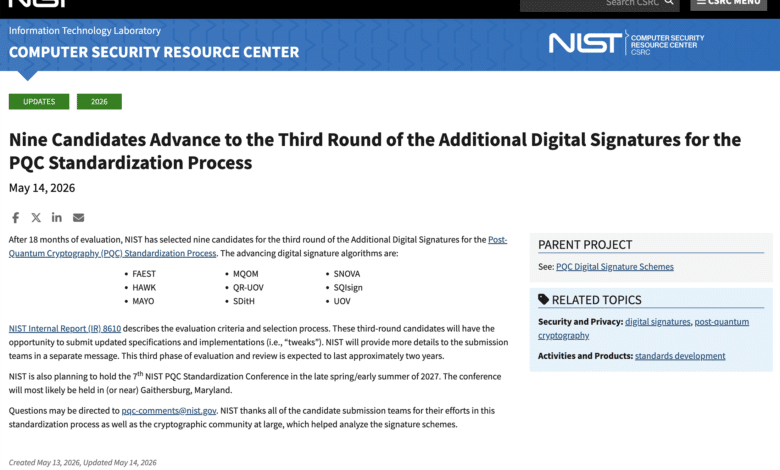
NIST Narrows the Field: Nine Post-Quantum Signature Candidates Advance to the Third Round
NIST just narrowed 14 post-quantum signature candidates to nine. The survivors span four distinct mathematical families, from isogeny-based compact signatures to multivariate schemes under active cryptanalytic fire. Here's what each candidate is, why NIST kept it, and what this means for your PQC migration planning ...
CNSA 2.0: The Complete Guide to NSA’s Post-Quantum Requirements
The definitive vendor-neutral reference to NSA's Commercial National Security Algorithm Suite 2.0 — the most operationally specific post-quantum cryptography mandate in the world. This guide breaks down every component of CNSA 2.0 in one place: the complete algorithm suite with NIST standard names and FIPS references (ML-KEM-1024, ML-DSA-87, AES-256, SHA-384/512, LMS, XMSS), why NSA mandates ...
The Quantum Threat to Cryptocurrencies: What’s Real, What’s Hype, and What to Do About It
Google Quantum AI estimates that breaking the 256-bit elliptic curve cryptography protecting Bitcoin and Ethereum would require fewer than 500,000 physical qubits and roughly nine minutes of runtime on a superconducting architecture. The same day that paper landed, a separate team published estimates showing the same computation could be performed with as few as 10,000 ...
Pick One Layer: How to Choose the Post-Quantum Migration That Protects the Most
Recent research proves one post-quantum layer can protect all payload confidentiality. But which layer should you migrate first? Six enterprise architecture scenarios analyzed ...
The Quantum Utility Ladder: What Fault-Tolerant Quantum Computers Will Actually Be Used For
Most quantum computing coverage fixates on breaking encryption. The real near-term story is utility — chemistry, materials, energy, drug design. This article maps every major fault-tolerant quantum algorithm to its logical qubit requirements, T-gate costs, and the real-world problem it solves, from photosensitizer calculations at 350 qubits to bulk solid-state physics at 100,000. The ladder ...
The Narrow Advantage: Why Quantum Computing Will Transform Five Industries and Disappoint Twenty
After months of research and hundreds of papers, the picture is clear: quantum computing will deliver genuine competitive advantages for pharma, chemicals, batteries, advanced materials, and condensed-matter physics. For finance, logistics, and machine learning, the evidence is structurally weak. This capstone article synthesizes the full Quantum Utility Map series into a single strategic thesis ...
Quantum Computing by 2033: Which Industries Win, Which Wait, and Why
By 2033, fault-tolerant quantum computers with 2,000 logical qubits will create genuine competitive separation in pharma, chemicals, battery technology, and advanced materials. Finance, logistics, and machine learning face a structural barrier that no hardware improvement can fix. This strategic briefing maps the evidence and explains what to do about it ...
Quantum Snake Oil: A Field Guide to Misleading Quantum Technology Marketing
Sixteen terms. Two tracks. One field guide. The quantum technology market has the exact conditions that produce fraud in every emerging sector: high buzz, big money, low buyer literacy, and complex underlying science that most decision-makers cannot independently evaluate. This dictionary maps the terminology that CISOs, investors, and procurement officers encounter in vendor pitches: the ...
The Anatomy of Quantum Denial: What Bitcoin’s Response to the Quantum Threat Teaches Every CISO
At Bitcoin 2026, the same main stage hosted engineers building quantum-resistant upgrades and a trio claiming quantum computers can never work because Bitcoin proves time is discrete. The dysfunction that produced this scene plays out in every enterprise boardroom facing PQC migration ...
Crypto-Agility Is an Architecture Problem, Not a Library Swap
Every PQC migration guide tells you to "be crypto-agile." After leading migrations at Fortune Global 500 scale, I can tell you where that advice fails: HSMs that can't upgrade, protocols with hard-coded algorithms, and embedded devices that will outlive the cryptography they verify ...
Why Scaling Logical Qubits Gets Exponentially Harder — And Which Walls Hit First
Vendor roadmaps imply smooth growth from 100 to 100,000 logical qubits. The reality is that specific engineering dimensions hit qualitative walls at each scale, and which wall dominates depends entirely on the hardware modality ...
The Error Correction Revolution: Why qLDPC Codes, Magic State Cultivation, and Algorithmic Fault Tolerance Are Rewriting the Quantum Timeline
Between 2024 and 2026, three error correction advances reduced the physical qubit cost of fault-tolerant quantum computing by an order of magnitude or more. qLDPC codes compress the encoding ratio. Magic state cultivation shrinks factory footprint. Algorithmic fault tolerance cuts runtime overhead by a factor of the code distance. Together, they are rewriting the timeline ...
The Signature Supply Chain: How Deep Does Digital Trust Go?
From TPM attestation keys to container image signatures, modern systems depend on dozens of signature layers most security teams have never fully mapped. This deep dive exposes the full anatomy of the trust infrastructure a quantum computer would compromise ...
Why Quantum Won’t Save Wall Street (Yet): An Honest Assessment of Quantum Computing in Finance
The best quantum finance resource estimates, produced by Goldman Sachs' own research team, require logical clock speeds three orders of magnitude beyond any projected hardware. The quantum speedup for derivative pricing and portfolio optimization is quadratic, and quadratic is structurally insufficient. Here is what the evidence says and what financial institutions should do instead ...
PQC Standards Fragmentation: What Multinationals Must Plan For Now
Your New York office runs ML-KEM per NIST. Your Frankfurt office needs ANSSI-recommended hybrids. Your Shanghai office will require Chinese ICCS algorithms. Your Seoul subsidiary uses KpqC. You need one migration plan. This article maps how to build it ...
Quantum Sovereignty and the Utility Trap
The industries where quantum computing creates the most value are the industries most critical to national security. The hardware serving them is concentrated in a handful of companies and countries. The architectural decisions determining whether access is sovereign or dependent are being made now. This article explains the trap and how to avoid it ...