All Post-Quantum, PQC Posts
-
Post-Quantum, PQC, Quantum Security

The Quantum Random Number Generator (QRNG) Gold Rush
Everyone is selling quantum randomness. Most buyers can't tell the difference between genuine quantum entropy and a rebranded noise source with a quantum sticker on the box. This guide fixes that.
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Deadlines Are Likely About to Compress. Here’s What I’m Seeing.
Governments spent 2025 publishing PQC roadmaps. In 2026, they started giving those roadmaps teeth. A draft US executive order, the EU's first binding PQC law, and vendor deadlines from Google and AWS are collapsing the compliance horizon from 2035 to 2028–2030.
Read More » -
Global PQC Migration Timelines

The Global PQC Migration Clock: Where Every Country Stands and Why the Gaps Between Them Matter More Than the Deadlines Themselves
Fifteen countries have now set PQC migration timelines. They all agree the migration must happen. They disagree on when, how, and with which algorithms. This capstone maps the convergence, the conflicts, and the compliance reality for organizations operating across borders.
Read More » -
Post-Quantum, PQC, Quantum Security

“They’ll Just Rent One”: The Quantum Threat Model Nobody Bothered to Check
Every article about quantum threats includes the throwaway line: criminals won't need their own quantum computer, they'll just rent one. The actual evidence says otherwise.
Read More » -
PQC Governance

PQC Governance: Who Should Lead Your Post-Quantum Migration, and How to Structure the Program
PQC migration is the most complex cryptographic transformation in enterprise history. Getting the governance model right determines whether it succeeds or stalls. Here's how to structure it.
Read More » -
Quantum Security & PQC

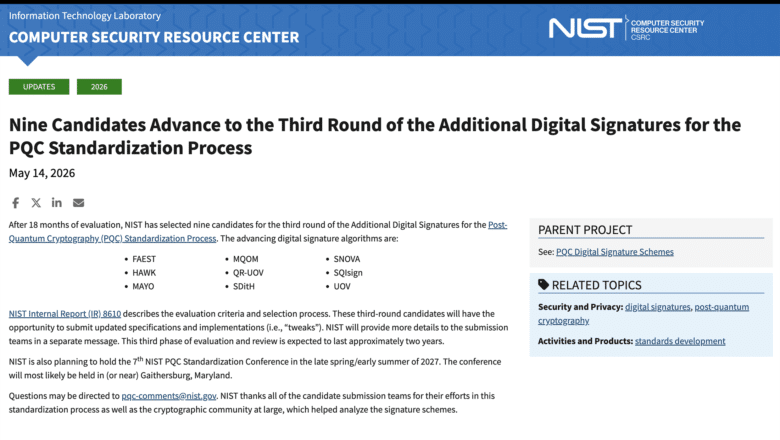
NIST Narrows the Field: Nine Post-Quantum Signature Candidates Advance to the Third Round
NIST just narrowed 14 post-quantum signature candidates to nine. The survivors span four distinct mathematical families, from isogeny-based compact signatures to multivariate schemes under active cryptanalytic fire. Here's what each candidate is, why NIST kept it, and what this means for your PQC migration planning.
Read More » -
CNSA 2.0

CNSA 2.0: The Complete Guide to NSA’s Post-Quantum Requirements
The definitive vendor-neutral reference to NSA's Commercial National Security Algorithm Suite 2.0 — the most operationally specific post-quantum cryptography mandate in the world. This guide breaks down every component of CNSA 2.0 in one place: the complete algorithm suite with NIST standard names and FIPS references (ML-KEM-1024, ML-DSA-87, AES-256, SHA-384/512, LMS, XMSS), why NSA mandates only the highest parameter levels, the full category-by-category transition timeline…
Read More » -
Quantum Threat to Cryptocurrencies

The Quantum Threat to Cryptocurrencies: What’s Real, What’s Hype, and What to Do About It
Google Quantum AI estimates that breaking the 256-bit elliptic curve cryptography protecting Bitcoin and Ethereum would require fewer than 500,000 physical qubits and roughly nine minutes of runtime on a superconducting architecture. The same day that paper landed, a separate team published estimates showing the same computation could be performed with as few as 10,000 reconfigurable neutral atom qubits over roughly ten days. Neither machine…
Read More »