Pentagon CIO memo puts post-quantum crypto on a procurement leash

Table of Contents
22 Nov 2025 – A memo from The Pentagon CIO dated Nov. 18, 2025 (cleared for open publication Nov. 20) forces a shift from ad‑hoc PQC pilots to a controlled, enterprise migration program. It orders an all-systems cryptography inventory, requires Components to name PQC migration leads, makes PQC testing and acquisition subject to CIO intake/deployment approvals, and draws bright lines – most notably, it bars quantum key distribution (QKD) for confidentiality, authenticity, or integrity and sets Dec. 31, 2030 as the key retire-by date for PSK-based and symmetric “quantum resistance” approaches.
What happened and why the timing matters
The memo is published via the DoD Chief Information Officer public document library and signed by Katherine Arrington in a “performing the duties” CIO role. The document’s letterhead uses “Department of War” and the abbreviation “DoW,” but it is positioned as Pentagon-wide guidance.
The timing is not accidental. OMB’s memo M‑23‑02 (Nov. 2022) pushed federal agencies to inventory cryptography (for civilian, non‑NSS systems) and estimate the funding needed for PQC migration. Meanwhile NIST has published core PQC standards – FIPS 203/204/205 (Aug. 2024): ML‑KEM for key establishment and ML‑DSA/SLH‑DSA for digital signatures.
Against that backdrop, this memo reads like an attempt to stop “quantum-safe sprawl”: vendor-led crypto choices and incompatible deployments that turn into long-lived technical and contracting debt.
What the memo orders
The first move is visibility. Components must “identify and inventory any type of cryptography used” across virtually all system categories – explicitly including NSS and non‑NSS, business and weapons systems, cloud, mobile, physical access control, IoT, unmanned systems, and operational technology – “regardless of classification, location, connection, type, purpose, or use.”
The second move is ownership and coordination. Each Component must submit a roster of PQC migration leads (down to subordinate organizations) within 20 days of the memo date, then refresh the roster annually by Sept. 30. The memo designates Britta Hale as the department lead/point of contact for PQC and notes coordination across NSA, DoW PKI, and Defense Information Systems Agency.
The memo doesn’t label “migration phases,” but its implied sequence is clear: assign leads, inventory cryptography, run pilots only with intake approval, then deploy with deployment approval and burn down nonconforming approaches by 2030/2031.
The third move is control. Components must submit PQC-related artifacts (test plans/results, acquisition artifacts, risk mitigations, and related materials) immediately. The CIO office reviews them for security risk and interoperability constraints; issues must be addressed before acquisition or broader “engagement.” If the PQC Directorate identifies security issues, Components must stop tests or pilots and coordinate remediation; if issues cannot be mitigated, systems can be removed from PQC engagement. The attachment also says updated PQC requirements and approval processes will be maintained in a single CIO-hosted location.
The attachment formalizes two gates: (1) cryptographic intake approval before testing/piloting/using/acquiring PQC-related technology and (2) cryptographic deployment approval before deployment, informed by Intelligence Community, NIST, and National Security Agency certification outcomes.
What it does not specify is also important. The memo does not name specific PQC algorithms (it only says “NIST‑approved” and “CNSA 2.0‑listed” for NSS), it does not identify which protocol profiles (TLS, IPsec, S/MIME, SATCOM links, etc.) will be prioritized first, and it does not allocate new funding (only noting a desire to optimize fiscal investments).
The technical red lines and deadlines
The memo draws three unusually sharp boundaries.
It blocks QKD and related “quantum keying/confidentiality” technologies for confidentiality, authenticity, or integrity on Department networks – explicitly including QKD, QKD hybrids, quantum networking used for keying, non-local quantum randomness generation, and non‑FIPS random number generation – unless an exception is granted.
It targets “quantum resistance” built on pre‑shared keys (PSKs): if PSKs are not provisioned through NSA Key Management Infrastructure (KMI) for Type 1 devices, those solutions must be replaced with NIST‑approved (or CNSA 2.0‑listed for NSS) asymmetric PQC key-establishment algorithms by Dec. 31, 2030. New commercial PSK-based “quantum resistance” pilots/acquisitions are banned immediately.
It sunsets symmetric key establishment/agreement/distribution protocols used for “quantum resistance” by Dec. 31, 2030 – extended to Dec. 31, 2031 for solutions registered with NSA’s Commercial Solutions for Classified (CSfC) program – with an exemption for symmetric key distribution protocols used prior to 2010.
Memo requirements versus NIST’s standards baseline
NIST supplies the cryptographic primitives; the Pentagon memo supplies an enterprise governance wrapper around adopting them. For National Security Systems, the memo’s “CNSA 2.0‑listed” language aligns with NSA-led policy and certification pathways tied to the National Manager role.
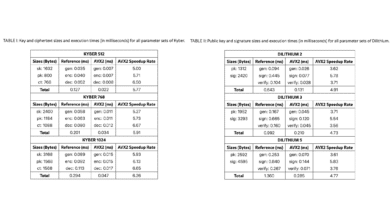
| Topic | Pentagon memo requirement | NIST baseline / recommendation context |
|---|---|---|
| PQC algorithms | Requires “NIST‑approved” (and CNSA 2.0-listed for NSS); no names | FIPS 203/204/205 standardized ML‑KEM, ML‑DSA, SLH‑DSA; HQC selected as a backup KEM candidate |
| Inventories | Inventory all cryptography across NSS, weapons, OT, cloud, mobile | NIST doesn’t mandate inventories; OMB mandates prioritized inventories for civilian non‑NSS systems |
| Governance and gates | PQC leads in 20 days; intake + deployment approval required | NIST does not prescribe governance; civilian timelines are driven by OMB and agencies |
| Deprecation deadlines | 12/31/2030 (and 12/31/2031 for CSfC-registered symmetric solutions) | NIST standards don’t set deadlines; deadlines are set by implementers and NSS policy frameworks |
Why it matters and what I think happens next
The inventory requirement is the real forcing function. PQC migrations fail when organizations do not know where cryptography actually lives – especially in identity/PKI, embedded systems, weapons subsystems, and vendor-managed services. This memo makes that ignorance an unacceptable state across both enterprise IT and the long tail of mission and platform systems.
I read the approval model as an attempt to prevent “cryptographic debt”: quantum-safe point solutions that can’t interoperate, can’t be certified, or can’t be upgraded at scale. The bans – particularly on QKD-for-security and on PSK/symmetric quantum-resistance workarounds – signal a push toward standardized, certifiable public-key PQC. For vendors, the practical implication is that PQC claims will be treated like a safety case: show the artifacts, the interoperability story, and the certification path.
The risk is throughput. Central gates only work if the PQC Directorate has engineering capacity – test harnesses, interoperability profiles, reference architectures, and procurement language – to clear decisions quickly. Otherwise, Components will either wait or route around governance in ways that recreate fragmentation.
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.