Treasury Board’s PQC SPIN: Canada Turns Post‑Quantum Migration Into Dated, Auditable Requirements
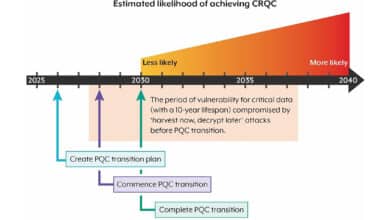
10 Oct 2025 – Treasury Board of Canada Secretariat has now formalized PQC migration as a measurable federal IT obligation via a Security Policy Implementation Notice (SPIN) titled “Migrating the Government of Canada to Post‑Quantum Cryptography.” It is both published and effective on October 9, 2025, and it does something the earlier PQC roadmap did not fully achieve on its own: it converts “plan to migrate” into specific deliverables with hard dates, explicit procurement triggers, and a named compliance monitoring path tied to Treasury Board’s broader compliance framework.
What SPIN covers and how it will be monitored
The SPIN’s scope is broad: it applies to any Government of Canada information system (departmental or enterprise) that employs cryptography, spanning network services, operating systems, applications, code development pipelines, and physical IT assets. It applies to the organizations listed in section 6 of the Policy on Government Security, and it frames the migration plan scope as systems handling up to and including Protected B; for classified systems and systems handling Protected C, departments are directed to contact the Cyber Centre (details for those environments are unspecified on the SPIN page).
On enforcement: the SPIN explicitly anchors consequences for non‑compliance to the Framework for the Management of Compliance (Appendix C for institutions, Appendix D for individuals) and states that Treasury Board will monitor progress and engage senior officials (CIO/CSO/DOCS/procurement official) when required-action deadlines are missed. SSC is also tasked with periodic updates to the IT Security Tripartite on infrastructure/network migration progress.
Every deliverable and deadline, in plain language
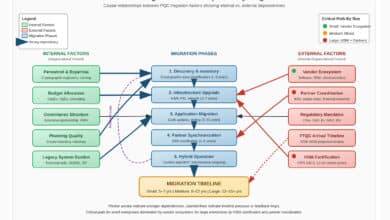
The SPIN lays out a three‑phase program (Preparation, Identification, Transition) and assigns dated deliverables to departments/agencies and to Shared Services Canada (SSC):
By April 1, 2026, departments/agencies must (a) develop a high‑level departmental PQC migration plan guiding Phase 1 and (b) begin annual PQC progress reporting with incremental plan updates; by the same date SSC must publish its own high‑level plan for systems it operates, share it to support dependency planning, and also begin annual progress reporting.
By April 1, 2027, departments/agencies and SSC must update their high‑level plans to guide Phase 2.
By April 1, 2028, departments/agencies (including SSC) must update system records in TBS’s Application Portfolio Management tool (or a comparable tool) so that each system record includes, at minimum: architecture/cryptographic details (algorithms, protocols, crypto components, hosting, dependencies), vendor and lifecycle data (contracts, refresh year), and migration oversight fields (POC, priority, status). By that same date they must also identify high‑priority systems (explicitly calling out “harvest now, decrypt later” exposure as an example) and engage SSC on upgrade/replace plans for SSC‑provided services.
Also on April 1, 2026, a procurement switch flips: all contracts with a digital component entered into after this date must include PQC‑aligned procurement clauses supporting (a) PQC compliant with Cyber Centre recommendations, (b) CMVP‑certified cryptographic modules, and (c) cryptographic agility for future configuration changes. Departments and SSC must, by April 1, 2028, update plans for Phase 3 and begin transitioning systems.
Finally, by end of 2031 high‑priority systems must be migrated, and by end of 2035 remaining systems must be migrated.
How SPIN operationalizes the roadmap and contract clauses—and what the market should expect
In practice, this SPIN is the bridge between strategy and execution. It directly references the Cyber Centre’s PQC roadmap (ITSM.40.001) for the overall migration concept and timeline, and it makes procurement requirements real by pointing departments to Cyber Centre procurement clause guidance – where ITSM.00.501 provides concrete example clause language procurement teams can lift into RFPs and contracts.
For vendors, the commercial implication is immediate: “PQC readiness” becomes a contractual term for new federal deals after April 1, 2026, and a data‑field expectation in enterprise application portfolios by April 1, 2028. Expect accelerated demand for: PQC‑capable roadmaps, CMVP validation planning, crypto-agile architectures, and credible interoperability testing – especially for products embedded in shared infrastructure and identity/PKI-dependent workflows. The SPIN also reduces ambiguity by tying “PQC compliant” to the Cyber Centre’s cryptographic algorithm baseline (ITSP.40.111).
Key gaps/risks remain: the SPIN does not specify reporting formats, scoring metrics, or audit methods (unspecified); “digital component” is not defined on the SPIN page (unspecified); and the instrument primarily governs federal systems (applicability beyond federal procurement is unspecified).
Three practical recommendations
- Vendors: publish a PQC transition plan mapped to ITSP.40.111 terminology and be ready to contractually commit to crypto agility + maintainable update paths.
- Vendors: treat CMVP readiness as a delivery milestone (not a marketing claim): plan timelines, evidence packages, and operating-mode constraints early.
- Procurement teams: pre‑bake SPIN‑aligned clauses into templates now so April 1, 2026 contracts don’t become a scramble – and require bidders to provide cryptographic inventories aligned to the SPIN’s 2028 APM data fields.
SPIN materially advances Canada’s quantum readiness by turning PQC migration into dated, trackable, procurement-enforced work rather than optional “roadmap intent.”
Quantum Upside & Quantum Risk - Handled
My company - Applied Quantum - helps governments, enterprises, and investors prepare for both the upside and the risk of quantum technologies. We deliver concise board and investor briefings; demystify quantum computing, sensing, and communications; craft national and corporate strategies to capture advantage; and turn plans into delivery. We help you mitigate the quantum risk by executing crypto‑inventory, crypto‑agility implementation, PQC migration, and broader defenses against the quantum threat. We run vendor due diligence, proof‑of‑value pilots, standards and policy alignment, workforce training, and procurement support, then oversee implementation across your organization. Contact me if you want help.