Getting Started With Quantum Security & PQC
Everything you need to understand the quantum threat to cryptography and how to prepare. From foundational concepts to practical migration strategies, this series builds your quantum security knowledge from the ground up.
-
120,000 Tasks: Why Post‑Quantum (PQC) Migration Is Enormous
When I tell fellow CISOs, board members, or even seasoned program managers that the integrated program plan for a comprehensive quantum security / post-quantum cryptography (PQC) migration I recently worked on contained over 120,000 discrete tasks, the reaction is almost…
Read More » -
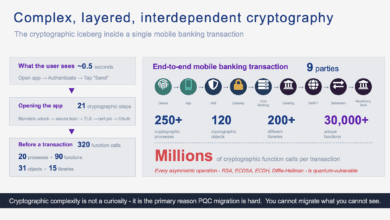
The Cryptographic Iceberg Inside a Mobile Banking Transaction
A single mobile banking payment triggers millions of cryptographic function calls across nine parties. Here's what actually happens - from silicon to settlement - and why it matters for quantum readiness. The Cryptographic Iceberg Inside a Mobile Banking Transaction 320…
Read More » -
Rethinking CBOM
The simplest way to explain CBOM is still the best. If SBOM is the ingredients list for software, CBOM is the ingredients list for the security assumptions that software depends on. Where SBOM tracks components and dependencies, CBOM tracks cryptographic…
Read More » -
Q-Day Isn’t an Outage – It’s a Confidence Crisis
Cybersecurity lore often paints Q-Day (the moment a quantum computer cracks RSA/ECC encryption) as an instant "Quantum Apocalypse" where every system gets hacked immediately. Planes falling from the sky, banks drained in seconds, an overnight digital Armageddon - if that…
Read More » -
Post-Quantum Negligence: Legal Risks of Failing to Prepare for the Quantum Threat
Quantum computing is no longer a far-off hypothesis - it’s a rapidly emerging reality that could render today’s encryption obsolete. For CISOs and their boards, this means a new kind of cybersecurity crisis is on the horizon. Sensitive data that…
Read More » -
Trust Now, Forge Later (TNFL) – The Overlooked Quantum Threat
What is "Trust Now, Forge Later" (TNFL)? Most discussions about quantum computing threats focus on “Harvest Now, Decrypt Later” (HNDL) - the idea that adversaries can collect encrypted data today and store it, hoping a future quantum computer will break…
Read More » -
Quantum Readiness Is Not (Just) a Vendor Problem
In the recent IBM's “Secure the Post-Quantum Future” report 62% of executives admitted that their organization is waiting for vendors to make them quantum‑safe. In other words, they expect cloud providers, network equipment makers and software vendors to embed post‑quantum…
Read More » -
Getting Started With Quantum Security and PQC Migration
Your complete roadmap to quantum-proofing your organization — from boardroom mandate to operational crypto-agility. This practitioner-curated Deep Dive series collects the PostQuantum.com articles you need to launch and run a quantum-readiness program, organized along the lifecycle most teams actually follow:…
Read More » -
Quantum-Readiness / PQC Full Program Description (Telecom Example)
Preparing a large telecom (or any enterprise) for the post-quantum cryptography era is a massive, multi-faceted undertaking, but it is achievable with foresight, resources, and commitment. We’ve seen that it involves much more than just installing new algorithms - it’s…
Read More » -
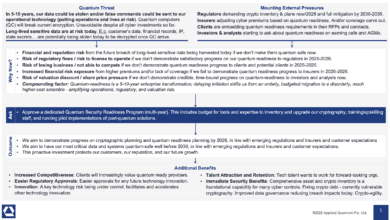
Forget Q-Day Predictions – Regulators, Insurers, Investors, Clients Are Your New Quantum Clock
Whether you personally believe Q-Day will come in 5 years or 50, the world around you isn’t taking chances - and neither can you. As a CISO, you’re now being implicitly (and sometimes explicitly) told by every corner of your…
Read More » -
Marin’s Law on Crypto-Agility: Adaptability Determines Survivability
Thesis: Migration time to safer cryptography is inversely proportional to an organization’s crypto-agility. Formally: Let A denote an organization’s crypto-agility (0 ≤ A ≤ 1) and Y the wall-clock time required to replace a cryptographic primitive across all in-scope systems.…
Read More » -
Securing Quantum Readiness Budget Now
From a CISO and business leadership perspective, the ask is clear: we need to secure budget and resources now to begin the multi-year journey of quantum-proofing our organization. This includes funding for risk assessments, cryptographic inventory tools, new encryption software/hardware,…
Read More » -
Risk-Driven Strategies for Quantum Readiness When Full Crypto Inventory Isn’t Feasible
Given the practical challenges, organizations may need to begin their quantum-readiness journey with a risk-driven approach rather than a theoretically perfect one. The essence of this strategy is to focus limited resources where they matter most – addressing the highest…
Read More » -
What is the Quantum Threat? A Guide for C‑Suite Executives and Boards
Boards do not need to dive into the scientific intricacies of qubits and algorithms, but they do need to recognize that this is a strategically important risk – one that can’t be simply delegated away. It requires the same level…
Read More » -
How CISOs Can Use Quantum Readiness to Secure Bigger Budgets (and Fix Today’s Problems)
Quantum readiness is not an exercise in science fiction – it’s a very practical program that yields benefits immediately. Regulators are pushing us all in this direction, which means boards are willing to fund it. The journey forces you to…
Read More »