Deep Dive Series
Getting Started With Quantum Security & PQC Migration
Post-quantum migration is not a patch cycle. It is the largest, most complex cryptographic overhaul most organizations will ever face — touching every system, every vendor, every protocol, and every assumption about how digital trust actually works. The challenge is not picking an algorithm. It is building the program: securing the mandate, finding the cryptography, documenting it, prioritizing what matters, and then migrating without breaking the business.
This Deep Dive series is a practitioner’s roadmap for that journey — organized along the lifecycle most teams actually follow. From boardroom business cases and budget justification, through cryptographic discovery and CBOM construction, to hybrid pilots, infrastructure hardening, and vendor governance, each phase links to detailed, opinionated guidance drawn from real-world PQC migration programs. The articles are designed to be read in sequence as laid out in the companion guide, or dipped into individually wherever your organization is today.
-
Post-Quantum, PQC, Quantum Security
How CISOs Can Use Quantum Readiness to Secure Bigger Budgets (and Fix Today’s Problems)
Quantum readiness is not an exercise in science fiction – it’s a very practical program that yields benefits immediately. Regulators are pushing us all in this direction, which means boards are willing to fund it. The journey forces you to finally catalog your cryptographic assets and clean up long-standing weaknesses, improving your security posture right now. It builds agility so you can handle any crypto…
Read More » -
Leadership
What is the Quantum Threat? A Guide for C‑Suite Executives and Boards
Boards do not need to dive into the scientific intricacies of qubits and algorithms, but they do need to recognize that this is a strategically important risk – one that can’t be simply delegated away. It requires the same level of governance attention as other enterprise-level risks like financial compliance, geopolitical factors, or pandemic preparedness. The comforting news is that if organizations act early, the…
Read More » -
Post-Quantum, PQC, Quantum Security
Risk-Driven Strategies for Quantum Readiness When Full Crypto Inventory Isn’t Feasible
Given the practical challenges, organizations may need to begin their quantum-readiness journey with a risk-driven approach rather than a theoretically perfect one. The essence of this strategy is to focus limited resources where they matter most – addressing the highest quantum-vulnerability risks first and implementing interim safeguards for the rest. Even the U.S. government’s guidance recognizes the need for prioritization. For example, the federal memo…
Read More » -
Post-Quantum, PQC, Quantum Security
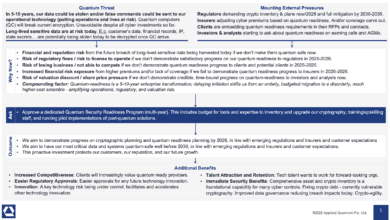
Securing Quantum Readiness Budget Now
From a CISO and business leadership perspective, the ask is clear: we need to secure budget and resources now to begin the multi-year journey of quantum-proofing our organization. This includes funding for risk assessments, cryptographic inventory tools, new encryption software/hardware, staff training or hiring, and pilot projects to start integrating PQC. The investment is justified not only by the avoidance of a potentially catastrophic future…
Read More » -
Post-Quantum, PQC, Quantum Security
Marin’s Law on Crypto-Agility: Adaptability Determines Survivability
Thesis: Migration time to safer cryptography is inversely proportional to an organization’s crypto-agility. Formally: Let A denote an organization’s crypto-agility (0 ≤ A ≤ 1) and Y the wall-clock time required to replace a cryptographic primitive across all in-scope systems. Then Y ≈ K ⁄ A for some complexity constant K. As A → 0, Y → ∞. Corollary: Raising A today shortens all future…
Read More » -
Q-Day
Forget Q-Day Predictions – Regulators, Insurers, Investors, Clients Are Your New Quantum Clock
Whether you personally believe Q-Day will come in 5 years or 50, the world around you isn’t taking chances - and neither can you. As a CISO, you’re now being implicitly (and sometimes explicitly) told by every corner of your ecosystem that quantum preparedness is mandatory. Regulators demand it via hard deadlines. Key clients and partners demand it in contracts and RFPs. Insurers will soon…
Read More » -
Post-Quantum, PQC, Quantum Security
Quantum-Readiness / PQC Full Program Description (Telecom Example)
Preparing a large telecom (or any enterprise) for the post-quantum cryptography era is a massive, multi-faceted undertaking, but it is achievable with foresight, resources, and commitment. We’ve seen that it involves much more than just installing new algorithms - it’s about transforming an organization’s approach to cryptography across potentially thousands of applications and devices, under uncertain timelines and in coordination with many external players. In…
Read More » -
Post-Quantum, PQC, Quantum Security
Quantum Readiness Is Not (Just) a Vendor Problem
In the recent IBM's “Secure the Post-Quantum Future” report 62% of executives admitted that their organization is waiting for vendors to make them quantum‑safe. In other words, they expect cloud providers, network equipment makers and software vendors to embed post‑quantum cryptography (PQC) so that internal teams can simply apply updates. This mindset is understandable - modern enterprises depend on vast supply chains - but it…
Read More » -
Post-Quantum, PQC, Quantum Security
Trust Now, Forge Later (TNFL) – The Overlooked Quantum Threat
What is "Trust Now, Forge Later" (TNFL)? Most discussions about quantum computing threats focus on “Harvest Now, Decrypt Later” (HNDL) - the idea that adversaries can collect encrypted data today and store it, hoping a future quantum computer will break the encryption and expose sensitive information. This risk is very real, especially for data that needs to remain confidential for decades (think government secrets, health…
Read More » -
Post-Quantum, PQC, Quantum Security
Post-Quantum Negligence: Legal Risks of Failing to Prepare for the Quantum Threat
Quantum computing is no longer a far-off hypothesis - it’s a rapidly emerging reality that could render today’s encryption obsolete. For CISOs and their boards, this means a new kind of cybersecurity crisis is on the horizon. Sensitive data that is safely encrypted now may be sitting like a ticking time bomb, waiting to be cracked by tomorrow’s quantum machines. The message is clear: security…
Read More » -
Post-Quantum, PQC, Quantum Security
Q-Day Isn’t an Outage – It’s a Confidence Crisis
Cybersecurity lore often paints Q-Day (the moment a quantum computer cracks RSA/ECC encryption) as an instant "Quantum Apocalypse" where every system gets hacked immediately. Planes falling from the sky, banks drained in seconds, an overnight digital Armageddon - if that nightmare doesn’t happen, some assume Q-Day wasn’t so bad after all. But this view misses a crucial point. The real catastrophe of Q-Day isn’t that…
Read More » -
Post-Quantum, PQC, Quantum Security
Rethinking CBOM
The simplest way to explain CBOM is still the best. If SBOM is the ingredients list for software, CBOM is the ingredients list for the security assumptions that software depends on. Where SBOM tracks components and dependencies, CBOM tracks cryptographic assets - algorithms, protocols, certificates, keys, and related material - and the relationships that turn "implemented somewhere" into "actually used here." This is not happening…
Read More » -
Post-Quantum, PQC, Quantum Security
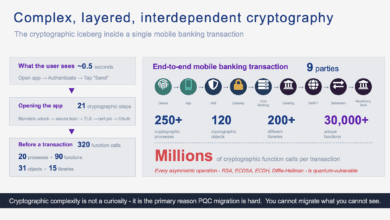
The Cryptographic Iceberg Inside a Mobile Banking Transaction
A single mobile banking payment triggers millions of cryptographic function calls across nine parties. Here's what actually happens - from silicon to settlement - and why it matters for quantum readiness. The Cryptographic Iceberg Inside a Mobile Banking Transaction 320 function calls before you even type an amount It takes roughly half a second. You press your thumb against the sensor, your banking app opens,…
Read More » -
Post-Quantum, PQC, Quantum Security
120,000 Tasks: Why Post‑Quantum (PQC) Migration Is Enormous
When I tell fellow CISOs, board members, or even seasoned program managers that the integrated program plan for a comprehensive quantum security / post-quantum cryptography (PQC) migration I recently worked on contained over 120,000 discrete tasks, the reaction is almost always the same. First, there is a polite silence. Then, the inevitable furrowing of the brow. Finally, the question: "Surely, you mean you counted every…
Read More »