Deep Dive Series
Getting Started With Quantum Security & PQC Migration
Post-quantum migration is not a patch cycle. It is the largest, most complex cryptographic overhaul most organizations will ever face — touching every system, every vendor, every protocol, and every assumption about how digital trust actually works. The challenge is not picking an algorithm. It is building the program: securing the mandate, finding the cryptography, documenting it, prioritizing what matters, and then migrating without breaking the business.
This Deep Dive series is a practitioner’s roadmap for that journey — organized along the lifecycle most teams actually follow. From boardroom business cases and budget justification, through cryptographic discovery and CBOM construction, to hybrid pilots, infrastructure hardening, and vendor governance, each phase links to detailed, opinionated guidance drawn from real-world PQC migration programs. The articles are designed to be read in sequence as laid out in the companion guide, or dipped into individually wherever your organization is today.
-
Post-Quantum, PQC, Quantum Security
The Challenge of IT and OT Asset Discovery
Every CISO understands the simple truth: you can’t protect what you don’t know you have. A comprehensive inventory of IT and OT assets - from servers and laptops to industrial controllers and IoT sensors - is the foundation of effective cybersecurity. In theory, building this asset inventory sounds straightforward. In practice, it’s one of the hardest tasks in cybersecurity today. Many enterprises find that even…
Read More » -
Post-Quantum, PQC, Quantum Security
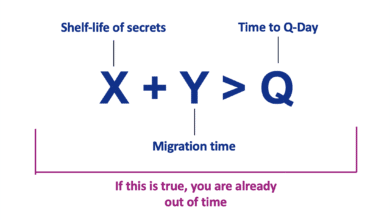
Mosca’s Theorem and Post‑Quantum Readiness: A Guide for CISOs
Mosca’s Theorem is a risk framework formulated to help organizations gauge how urgent their post-quantum preparations should be. It is often summarized by the inequality X + Y > Q, where: X = the length of time your data must remain secure (the required confidentiality lifespan of the information). Y = the time required to migrate or upgrade your cryptographic systems to be quantum-safe (your…
Read More » -
Post-Quantum, PQC, Quantum Security
Challenges of Upgrading to Post-Quantum Cryptography (PQC)
The shift to post-quantum cryptography is not a distant problem but an imminent challenge that requires immediate attention. The quantum threat affects all forms of computing—whether it’s enterprise IT, IoT devices, or personal electronics. Transitioning to quantum-resistant algorithms is a complex, resource-intensive task that demands coordination across the supply chain, extensive security audits, and careful management of performance and cost issues.
Read More » -
Post-Quantum, PQC, Quantum Security
Evaluating Tokenization in the Context of Quantum Readiness
As the quantum era approaches, organizations face the daunting task of protecting their sensitive data from the looming threat of quantum computers. These powerful machines have the potential to render traditional cryptographic methods obsolete, making it imperative to explore innovative strategies for quantum readiness. One often overlooked yet highly promising approach is tokenization.
Read More » -
Post-Quantum, PQC, Quantum Security
Ready for Quantum: Practical Steps for Cybersecurity Teams
“How do we actually get started and secure the budget for this, now?”. This comprehensive guide is the answer: a practical, step-by-step playbook for launching and running a quantum security program, updated with the latest lessons on budgeting, cryptographic inventory, risk mitigation workarounds, challenges of post-quantum migration, and achieving crypto-agility in a pragmatic way. We’ll bridge the gap between high-level warnings and on-the-ground execution, giving…
Read More » -
Post-Quantum, PQC, Quantum Security
Cryptography in a Modern 5G Call: A Step-by-Step Breakdown
Modern telecommunications networks rely on multiple layers of cryptography at every step of a call or data session. Understanding the complexity of the process and the amount of cryptography involved is critical for post-quantum migration planning - an initiative some of my advanced telecommunications clients are kicking off these days. And many are widely underestimating how much cryptography is used. From the moment a user’s…
Read More » -
Post-Quantum, PQC, Quantum Security
Planning the First Year of a Quantum Readiness Program
Embarking on a quantum readiness program can be daunting, so it’s helpful to break it into phases with concrete goals. Below is a pragmatic 12-month plan (roughly divided into phases) that a CISO-led team could follow. Based on a medium-size financial services company. This assumes you’re starting from little/no quantum readiness and want to establish momentum quickly:
Read More » -
Post-Quantum, PQC, Quantum Security
Dos & Don’ts of Crypto Inventories for Quantum Readiness
Relying on asset owners, developers or IT personnel to identify and report in interviews or survey responses every instance of cryptographic usage is not just impractical; it simply does not work...
Read More » -
Post-Quantum, PQC, Quantum Security
Common Failures in a Quantum Readiness Program
Even well-run quantum readiness programs can stumble. Here are some common pitfalls in crypto-agility/PQC efforts and how to avoid them: Treating PQC as a simple library or drop-in swap. Perhaps the biggest mistake is underestimating the ecosystem changes required. Simply implementing a PQC algorithm in code but ignoring the surrounding systems (PKI, certificates, protocols) is a recipe for trouble.
Read More » -
Post-Quantum, PQC, Quantum Security
Introduction to Crypto-Agility
As we edge closer to the Q-Day—the anticipated moment when quantum computers will be capable of breaking traditional cryptographic systems—the need for crypto-agility becomes increasingly critical. Crypto-agility is the capability of an organization to swiftly and efficiently transition between different cryptographic algorithms and protocols in response to emerging threats and technological advancements.
Read More » -
Post-Quantum, PQC, Quantum Security
Mitigating Quantum Threats Beyond PQC
The article explores limitations of PQC and explores alternative and complementary approaches to mitigate quantum risks. It provides technical analysis of each strategy, real-world examples of their deployment, and strategic recommendations for decision-makers. The goal is to illuminate why a diversified cryptographic defense – beyond just rolling out new algorithms – is essential to achieve long-term resilience against quantum-enabled adversaries.
Read More » -
Post-Quantum, PQC, Quantum Security
Engaging and Managing Vendors for Quantum Readiness
Vendors provide critical software, cloud platforms, fintech solutions, IoT devices, and more - and these often rely on vulnerable cryptographic algorithms under the hood. If a key vendor lags in upgrading their encryption, it could expose your data or systems to quantum-enabled attacks. Engaging vendors early allows you to:
Read More » -
Post-Quantum, PQC, Quantum Security
Bills of Materials for Quantum Readiness: SBOM, CBOM, and Beyond
Quantum computing threat is forcing organizations to inventory their digital assets like never before. With powerful quantum attacks on the horizon, businesses must identify what they have - software, cryptography, sensitive data, hardware - before they can secure it. Security standards and government directives now urge a comprehensive cryptographic inventory as the first step toward quantum readiness. In practice, compiling these inventories is daunting. Modern…
Read More » -
Post-Quantum, PQC, Quantum Security
Quantum Era Demands Changes to ALL Enterprise Systems
In my work with various clients, I frequently encounter a significant misunderstanding about the scope of preparations required to become quantum ready. Many assume that the transition to a post-quantum world will be straightforward, involving only minor patches to a few systems or simple upgrades to hardware security modules (HSMs). Unfortunately, this is a dangerous misconception. Preparing for this seismic shift is far more complex…
Read More » -
Post-Quantum, PQC, Quantum Security
Post-Quantum Cryptography PQC Challenges
The transition to post-quantum cryptography is a complex, multi-faceted process that requires careful planning, significant investment, and a proactive, adaptable approach. By addressing these challenges head-on and preparing for the dynamic cryptographic landscape of the future, organizations can achieve crypto-agility and secure their digital assets against the emerging quantum threat.
Read More »