Quantum Sovereignty & the New Cold War
Quantum technologies are leaving the lab and entering the machinery of national power. In a world where advanced computing, sensing, and secure communications shape military advantage and economic competitiveness, “quantum sovereignty” is becoming a blunt strategic question: who can build, operate, trust, and control quantum capabilities – under geopolitical stress – without being cut off?
This series, “Quantum Sovereignty & the New Cold War,” treats sovereignty as more than a slogan. It shows how deep physics becomes geopolitical leverage, how that leverage reshapes alliances and markets, and how strategy ultimately turns into architecture: procurement rules, vendor dependencies, supply chains, standards, and cryptographic choices.
The timing is not theoretical. PQC standardization has already moved into formal standards and government migration planning, while export controls have expanded to include quantum computing items- signals that the “trust boundary” around quantum is hardening.
Articles in the series
Part 1: Quantum Sovereignty Primer: Inside the New Tech Arms Race
This opening installment introduces quantum sovereignty as a spectrum, not a binary. It frames the modern quantum race as a multi-actor competition where technological dependence can become a strategic liability, and it sets up the series’ central tension: nations want the benefits of global innovation, but they also want the ability to operate when geopolitics turns supply relationships into choke points.
The article builds intuition through the “who, why, and what’s at stake” lens: leading competitors, regional fast followers, and the stakes spanning security, economic advantage, and military power. It also foreshadows where the series goes next—into the physics drivers, the geopolitical map, and then the operational playbook that turns sovereignty from ambition into implementation choices.
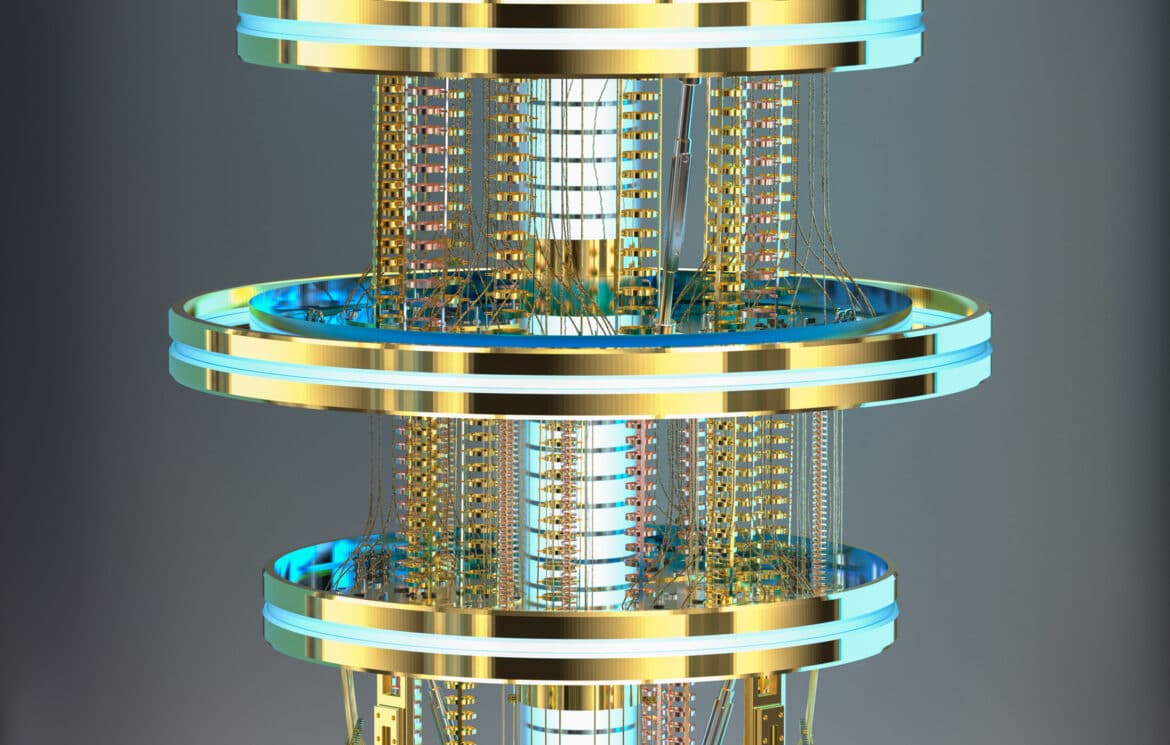
Part 2: Physics at the Heart of the New Cold War
This piece widens the aperture beyond “quantum hype” and explains why fundamental physics is re-emerging as a strategic asset class. It draws historical parallels to eras when physics breakthroughs reshaped global power, and it argues that the competition is not only about products – it is about mastery of scientific frontiers that cascade into defense, industry, and intelligence advantage.
The article also shows how geopolitics feeds back into science: research security, espionage incentives, export-control pressure, collaboration frictions, and the “re-wiring” of where advanced research happens. The purpose in the series is to explain why physics-driven capabilities become leverage—and why quantum, as one of the most strategically loaded physics domains, predictably becomes part of a new Cold War-style competitive logic.
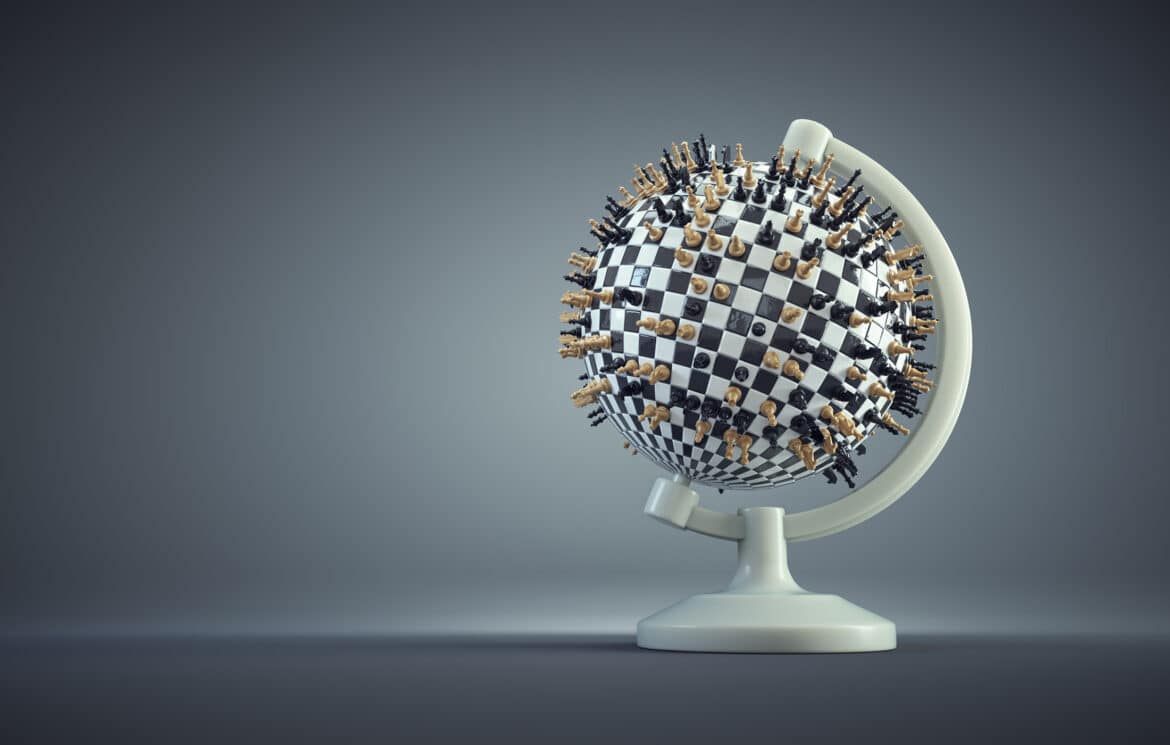
Part 3: Quantum Geopolitics: The Global Race for Quantum Computing
This installment is the macro map. It explains why quantum computing has geopolitical weight (cryptography, defense, economic competitiveness, and prestige) and situates quantum as a strategic technology that governments treat as both an innovation engine and a security concern.
It then surveys national approaches across key jurisdictions – including the United States, China, European Union, United Kingdom, India, and Russia – while highlighting the policy layer: export controls, security measures, standards, and the collaboration/competition dilemma. The outcome for the reader is a clearer sense of where the race is actually happening and how states are trying to translate quantum ambition into durable advantage.
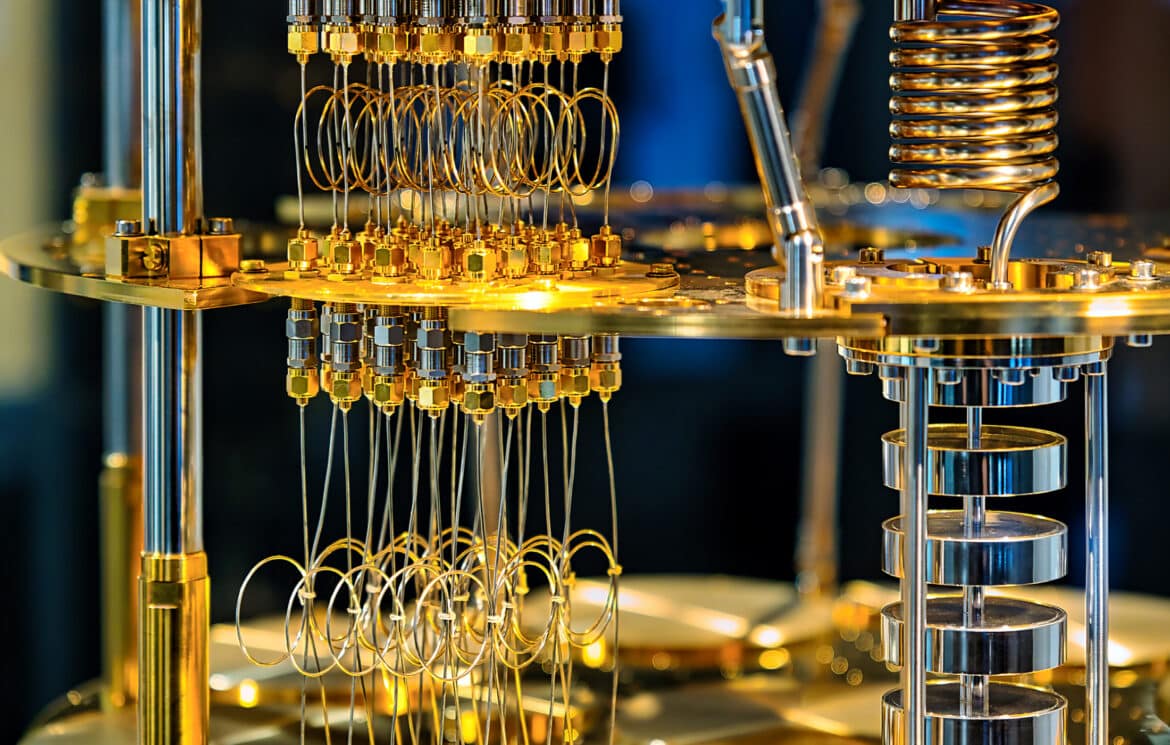
Part 4: Quantum Sovereignty in Practice: When Geopolitics Becomes Architecture
This piece is the pivot from geopolitics to engineering reality. It argues that quantum sovereignty is not only a “strategy document” problem – it becomes a systems-integration and architecture problem the moment you have to procure, deploy, secure, and operate quantum capabilities in the real world.
The article outlines a practical sovereignty playbook: selective domestic capability-building, open and modular architectures to reduce lock-in, diversified partnerships, niche specialization, supply chain and knowledge-base resilience, and the “people layer” of talent and operating know-how. Crucially, it sets up the next installment by linking sovereignty strategy to “sovereign optionality” – the idea that the realistic goal for most actors is not autarky, but the ability to pivot when dependencies become liabilities.
Part 5: Quantum Sovereign Optionality: Agility Over Autarky
This installment zooms in on the strategy that makes sovereignty practical for everyone who cannot (and should not) try to rebuild the full quantum stack alone. It reframes sovereignty as agility: the ability to verify, swap, and recompose dependencies fast enough to survive shocks – rather than the fantasy of total self-sufficiency.
The article then lays out a pragmatic optionality toolkit: standardize interfaces and embrace open platforms, cultivate multiple partnerships, focus on niche strengths, build domestic capabilities for verification and integration, and streamline policy so that “swaps” can happen without multi-year paralysis. It also argues that optionality can be a national advantage – especially when combined with trusted supply chains and standards leadership – because resilience often comes from having credible alternatives, not from insisting everything must be local.
Part 6: Sovereignty in the PQC Era: Standards, Trust, and Crypto-Agility
The final installment brings the sovereignty debate into the cryptographic layer—the part that quietly underpins digital power. It starts from a simple observation: PQC is entering the standards stage, but global adoption will not be frictionless or uniform, because standards are also instruments of trust, influence, and strategic autonomy.
The article explores how and why PQC could fragment: states pursuing independent algorithm suites, customizing parameters, layering domestic crypto over international standards, and building “crypto-agile” architectures that can rotate algorithms as trust and threat models change. It also highlights the systemic consequence of sovereignty-driven cryptography: interoperability becomes harder, compliance becomes messier, and “secure by standard” splits into “secure by bloc,” with alliances shaping what is trusted, certified, and deployed.