All Post-Quantum, PQC Posts
-
Post-Quantum, PQC, Quantum Security

The Quantum Random Number Generator (QRNG) Gold Rush
Everyone is selling quantum randomness. Most buyers can't tell the difference between genuine quantum entropy and a rebranded noise source with a quantum sticker on the box. This guide fixes that.
Read More » -
Post-Quantum, PQC, Quantum Security

Post-Quantum Deadlines Are Likely About to Compress. Here’s What I’m Seeing.
Governments spent 2025 publishing PQC roadmaps. In 2026, they started giving those roadmaps teeth. A draft US executive order, the EU's first binding PQC law, and vendor deadlines from Google and AWS are collapsing the compliance horizon from 2035 to 2028–2030.
Read More » -
Post-Quantum, PQC, Quantum Security

“They’ll Just Rent One”: The Quantum Threat Model Nobody Bothered to Check
Every article about quantum threats includes the throwaway line: criminals won't need their own quantum computer, they'll just rent one. The actual evidence says otherwise.
Read More » -
PQC Governance

PQC Governance: Who Should Lead Your Post-Quantum Migration, and How to Structure the Program
PQC migration is the most complex cryptographic transformation in enterprise history. Getting the governance model right determines whether it succeeds or stalls. Here's how to structure it.
Read More » -
Quantum Security & PQC

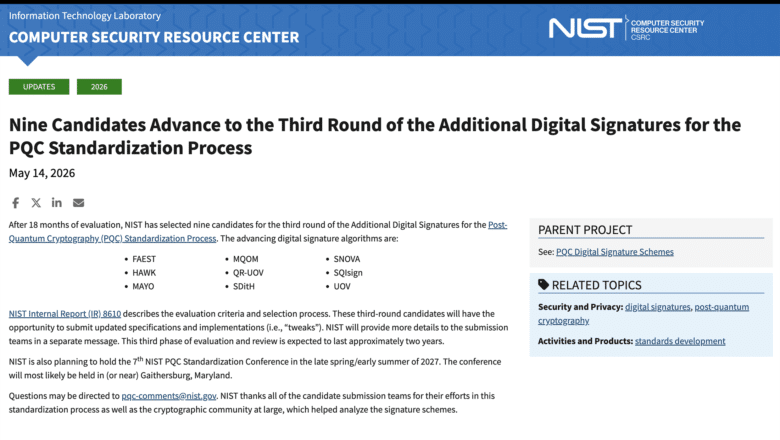
NIST Narrows the Field: Nine Post-Quantum Signature Candidates Advance to the Third Round
NIST just narrowed 14 post-quantum signature candidates to nine. The survivors span four distinct mathematical families, from isogeny-based compact signatures to multivariate schemes under active cryptanalytic fire. Here's what each candidate is, why NIST kept it, and what this means for your PQC migration planning.
Read More » -
Post-Quantum, PQC, Quantum Security

Pick One Layer: How to Choose the Post-Quantum Migration That Protects the Most
Recent research proves one post-quantum layer can protect all payload confidentiality. But which layer should you migrate first? Six enterprise architecture scenarios analyzed.
Read More » -
Post-Quantum, PQC, Quantum Security

The Anatomy of Quantum Denial: What Bitcoin’s Response to the Quantum Threat Teaches Every CISO
At Bitcoin 2026, the same main stage hosted engineers building quantum-resistant upgrades and a trio claiming quantum computers can never work because Bitcoin proves time is discrete. The dysfunction that produced this scene plays out in every enterprise boardroom facing PQC migration.
Read More » -
Post-Quantum, PQC, Quantum Security

Crypto-Agility Is an Architecture Problem, Not a Library Swap
Every PQC migration guide tells you to "be crypto-agile." After leading migrations at Fortune Global 500 scale, I can tell you where that advice fails: HSMs that can't upgrade, protocols with hard-coded algorithms, and embedded devices that will outlive the cryptography they verify.
Read More »